Four in every five enterprises are set to increase their cloud budgets over the next 12 months. If everyone’s doing it, surely you’re thinking that it’s time to jump on the bandwagon.
The great thing about cloud migration is that it isn’t a bandwagon, a phase, or a fad that’s going to pass by. It’s the future of business, and companies are migrating towards either a hybrid solution or a cloud service completely to unlock advantages like optimized workflows and scalability.
Azure is a popular choice when you’re considering a public cloud provider, and it currently holds 20% of the market share. Yet, increased usage comes with heightened security risks. The following are the top 5 security best practices when using Azure.
Key Differences Between Azure and AWS
Selecting one vendor over the other boils down to the needs and goals of your business and the workloads you’ll need to run. AWS is an old dog as far as technology is concerned, but that doesn’t mean it’s not at its peak. AWS tops the charts when it comes to the breadth and depth of the cloud services it provides, from storage to analytics and developer tools to enterprise applications.
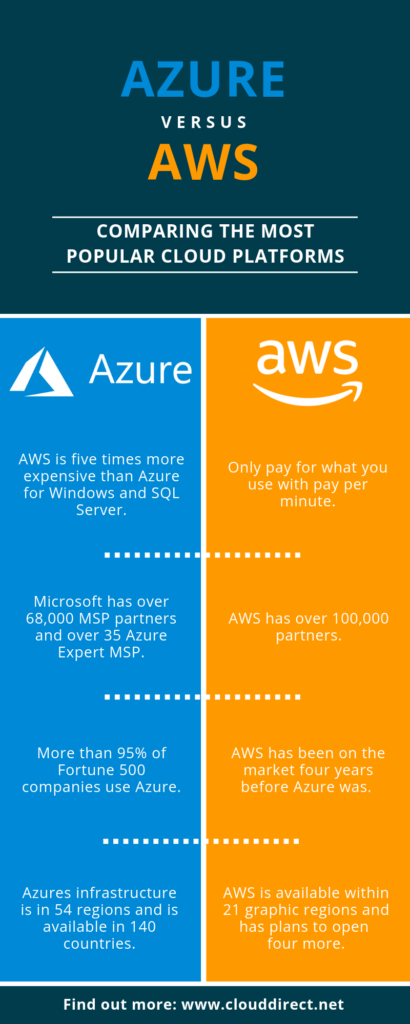
While AWS might be a front-runner, Azure is hot on its heels. Microsoft Azure is a popular choice among C-level executives due to the familiarity that developers have with the processes and procedures of Windows, and Azure’s integration with Office 365 and Teams. Azure Stack provides enterprises with the requirements to deploy Azure cloud services from a local data center with a shared management portal, code, and APIs for interoperability. These enticing features are contributing to Azure’s 40% growth per year.
What are the Benefits of Cloud Technologies?
1. Reduced CapEx
Establishing and maintaining data centers has a cost, whether it’s an on-premise setup that requires the procurement and upkeep of essential hardware or a third-party data center that requires an annual contract renewal. With cloud services, the pay-as-you-go pricing ensures that you pay for consumption and not for maintenance and backup.
2. Reliability
While hardware problems and the resulting downtime is rare with cloud deployment, some vendors offer to manage backups and disaster recovery, as well as promising 99% uptime. All this makes cloud migration a reliable option.
3. Scalability
The ability to easily scale up or down in terms of data storage capacity, processing power, and networking in response to your changing business needs is vital. Achieving the same level of scalability with an on-premise setup would be slow and expensive.
4. Convenience and Availability
The ability to access your applications from anywhere at any time allows for flexible schedules and productive remote work environments.
5. Implementation
The features mentioned above help provide an environment that allows your business to focus on innovation, optimization, and accelerated workflows. This helps development teams to turn their energies to the SDLC, which in turn contributes to revenue and growth.
What are the Challenges of Cloud Adoption and Migration?
1. Dealing with Integration
In most medium to large businesses, it is rare to find isolated systems. Usually, there are interconnected applications that are coupled at process and data levels. Integration can be a complex problem because you’ll need to perform a thorough discovery and workload analysis to obtain clarity on the integration needs and interdependent policies and processes.
2. Migration Costs
As well as the cost of migrating to the cloud, you’ll also need to allocate budget to retiring traditional on-prem hardware.
3. A Lack of Cloud Readiness
This can manifest either in the form of unskilled and inexperienced manpower or legacy applications that can’t support your cloud migration journey. Understanding the complexity of your business’s application landscape can give you clarity.
4. Security
The volume of data stored in the cloud can make it particularly enticing to hackers. Also, migration involves a third party cloud provider, which further increases the attack vector. Therefore, you may need to develop a shared responsibility model when adopting cloud strategies.
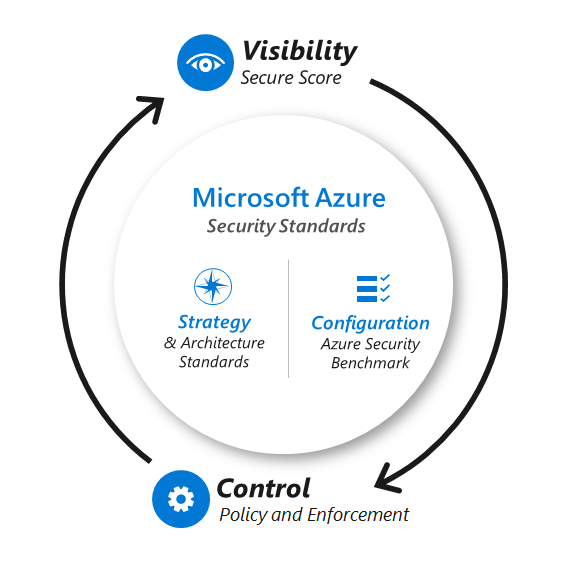
5 Azure Security Best Practices to Implement Today
Let’s look at the key Azure security best practices that you can follow to ensure a safe and swift cloud migration.
1. Educate and Upskill Your Teams
Ensure that the relevant teams have set aside time for technical education on cloud technology and cloud security. They need to become familiar with the recommended configurations and best practices, along with which resources to depend on when they’re making security decisions. Microsoft offers extensive resources that can help in such training. Identifying different or new protocols that are unique to cloud security can go a long way in starting off this journey. One of the ways you can foster this is by setting security KPIs to make your teams aware of the business’s shared security goals, then introducing upskilling as needed.
2. Enabling Passwordless or Multi-Factor Authentication
Passwords offer very little support in terms of thwarting attacks on administrators’ accounts. Instead, relying on passwordless sign-in methods can offer more in terms of security as these approaches by helping you keep track of trusted devices. The Azure AD multi-factor authentication is a benchmark that you can execute as an alternative to passwordless approaches.
3. Using Identity-based Access Control
While you can use key-based authentication for cloud and API authentication, it’s difficult to secure these keys at scale. One way to tackle this potential vulnerability is to get in the habit of using identity-based access control. Another useful initiative is the development of a security champion program, where interested members from the dev teams can receive further training on security protocols and act as a bridge between all departments on security-related matters.
4. Automation of Threat Detection
Threat detection can help in the prevention of any malicious attacks and subsequent data loss. Azure offers native features to help remediate attacks in the form of its Defender product. If you want to add an extra layer of protection and peace of mind, you could choose a solution like Ox Security that enables you to continuously monitor your SDLC from code to cloud. If threats are automatically detected, Ox Security alerts you so you can make informed decisions to minimize the crisis.
5. Integrating DevSecOps
Integrating DevSecOps involves automating security into every step of the SDLC and is the natural evolution in response to SDLC attacks. Similarly, Ox Security helps you ensure the SDLC stays in a secure state, quickly identify blindspots, and remediate risks according to business priorities.
Stay Safe From Code to Any Cloud With Ox Security
Public cloud spending reached $332.3 billion in 2021, with no signs of slowing down. As you continue to future-proof your business by adopting the cloud, it’s important to remember that your entire SDLC requires continuous monitoring to ensure it doesn’t drift from its secure state – and that includes maintaining the secure state of cloud technologies.
Ox Security ensures the security and integrity of all cloud artifacts, so you can turn your attention to other tasks in your cloud migration or adoption journey. There’s no time for your development teams to continuously monitor vulnerabilities when they’re focused on contributing to huge new changes in your business. Instead, Ox Security steps in to automatically block risks, detect anomalies, and maintain software pipeline integrity.
Book a demo or get started for free today.