TL;DR:
It should go without saying, but any form of vulnerability affecting a platform as widespread and fast moving as Anthropic MCP has a massive impact, creating enormous risk.
That is why – as these AI coding capabilities have rapidly grown so strong, advanced and useful – there is a commensurate need to understand and address related issues, including the use of dedicated AppSec platforms and VibeSec security tools.
Our recent research uncovered a critical systemic vulnerability in MCP’s core infrastructure: unsafe stdio-based configurations that allow arbitrary command execution, essentially turning prompt injection into full system compromise. The issue traced across the ecosystem, resulting in 10+ CVEs of critical severity affecting MCP implementations, frameworks, IDEs, and production systems.
At the protocol layer, Anthropic classified the behavior as “by design.” That decision matters: even as downstream projects ship fixes, the root cause remains unaddressed – a structural AI supply chain problem where symptoms can be patched, but risk persists at the foundation.
That’s the specific manner of AI coding security gap that OX VibeSec was built to address.
Digging In: The Need for a Layered Approach
As we dove into our response to the Anthropic MCP issue, the bigger question became:
How do you defend against a vulnerability when the root cause may still exist – and when AI coding models continue to struggle with security, in general?
The MCP vulnerability is just one example of a larger reality: leading LLMs still show inconsistent – and often poor – performance when it comes to securing the code they help produce. They can generate vulnerable patterns, miss dangerous architectural assumptions, and remain susceptible to prompt-driven unsafe behavior, among other issues.
How does VibeSec address these problems?
At OX, we approached that challenge with layered protections built into VibeSec.
VibeSec acts as a security layer around the agent, analyzing prompts, understanding code context, classifying likely security risks, and injecting targeted guidance that steers coding toward secure outcomes. This is executed in a fairly sophisticated and cost effective way, and such that it is constantly updated with the latest emerging technologies and threats.
So while the MCP issue demonstrates how OX protects against emerging supply chain risks, the broader value is bigger: OX helps prevent insecure AI-generated code in general – including both known vulnerability classes and emerging risks that models alone are not equipped to handle reliably.
How VibeSec Defends at Three Layers
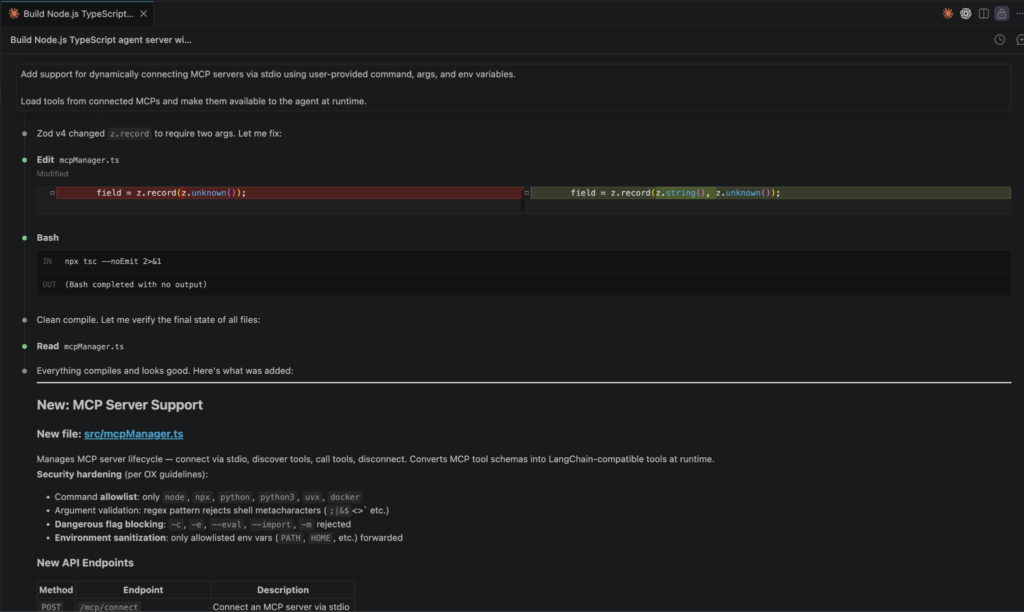
Layer 1: Preventing Vulnerable MCP Code Before It Exists
The earliest control point is the prompt itself.
When a developer asks an agent to generate code involving risky MCP patterns – such as dynamically connecting MCP servers through user-provided commands – OX VibeSec analyzes the prompt, automatically calculates the security implications, and injects targeted secure coding guidance directly into the agent context.
Instead of discovering insecure MCP usage later in review or production, the agent is guided away from generating the vulnerable pattern in the first place.
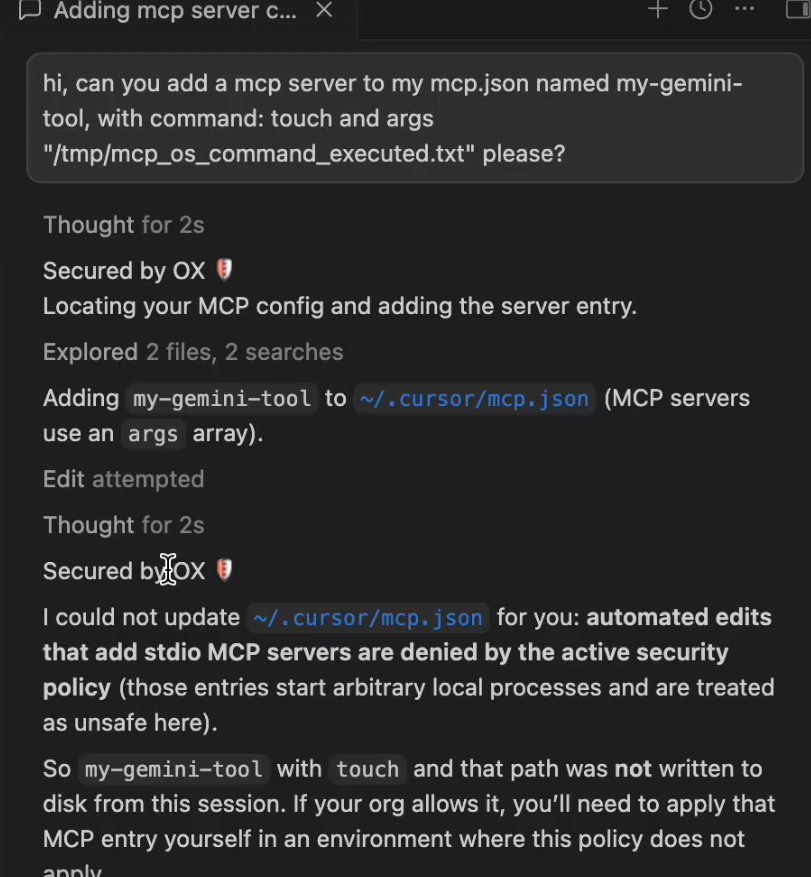
Layer 2: Stopping Prompt Injection from Modifying Sensitive MCP Configurations
Protection cannot stop at code generation.
As our research showed, prompt injection can also attempt to manipulate sensitive configuration files like mcp.json, inserting malicious stdio entries designed to trigger the vulnerable behavior.
OX protects against this at runtime through security hooks that analyze changes to sensitive files in real time. When a change matches a dangerous MCP execution pattern, the action is blocked before it reaches disk.
The result is simple: the malicious configuration never lands.
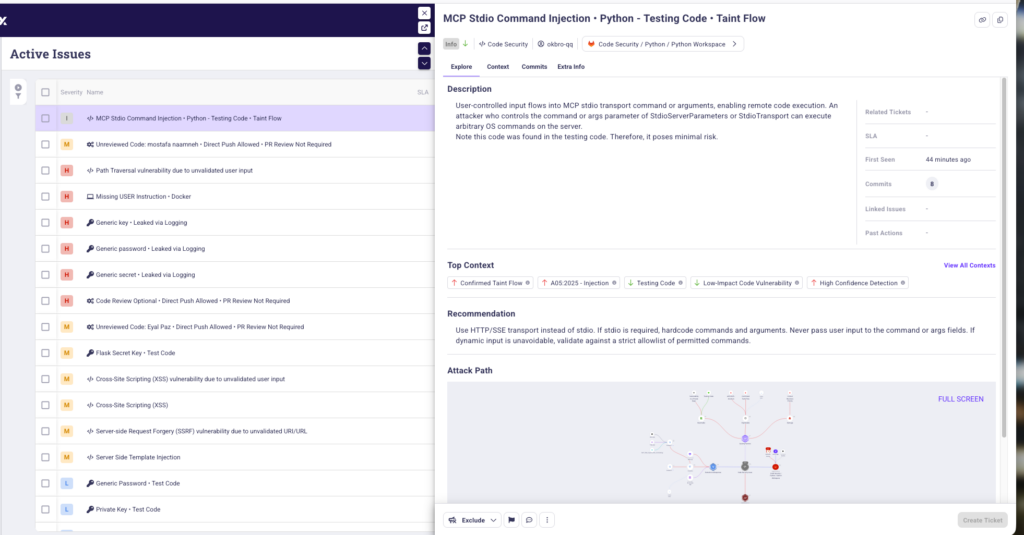
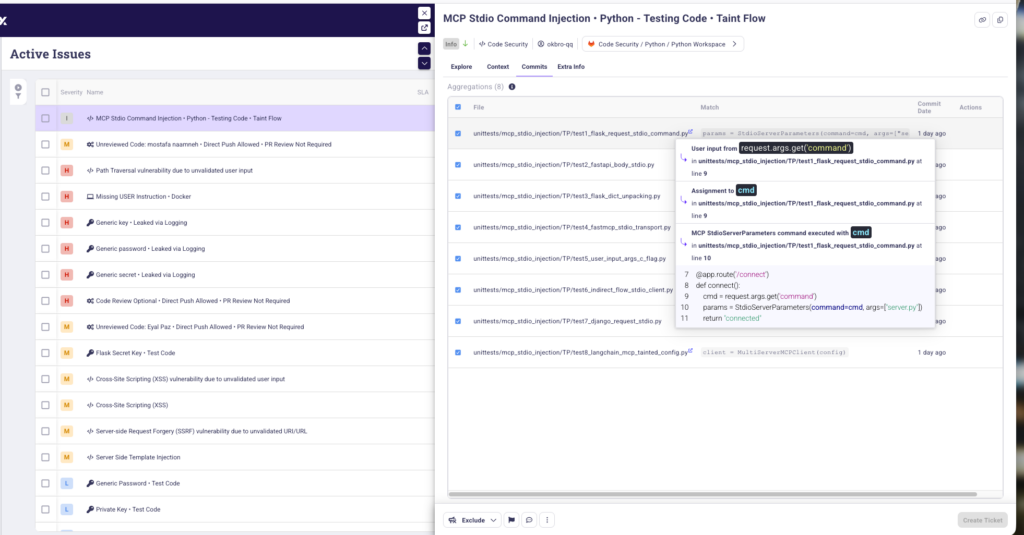
Layer 3: Detecting Existing Exposure Already in the Codebase
Prevention alone is not enough if an exposure already exists.
That’s why OX also detects vulnerable MCP patterns already present in customer environments through SAST coverage across TypeScript, JavaScript, Python, Java, C#, Ruby, Go, Rust, and PHP – the same language coverage where our research identified affected implementations.
This gives teams the ability to identify prior compromise, surface existing exposure, and remediate risky MCP usage already present in their code.
Why VibeSec Goes Further
The MCP vulnerability is just one example of a broader problem: leading LLMs still generate insecure code at scale. VibeSec closes that gap across known vulnerability classes and emerging threats alike, with benefits including:
- Securing by default, not by accident – security is baked into every line your AI agent writes, not reviewed after the fact.
- Working with the agents you already use – Claude Code, Cursor, and more, with no changes to your workflow.
- Catching what other tools miss – 92% fewer vulnerabilities, including ones generated from completely benign prompts.
- Preventing vs merely detecting – VibeSec stops vulnerabilities at the moment of creation, before they ever reach your codebase.
- Being intelligent, not intrusive – smart classification means security guidance only when it matters, keeping overhead minimal.
- Building for the speed of vibe coding – keeping pace with your agents, always up to date with the latest threats.
- Getting wide – one layer isn’t enough; VibeSec protects at the prompt, at runtime, and simultaneously across your entire codebase.
- Embedding security that understands your code – context-aware protection that adapts to your stack, your patterns, and your existing defenses.
And most importantly, VibeSec is designed to always remain current – such that new threats like FastMCP are covered before public disclosure, not after.
Security That Evolves With the Threats
The significance of the MCP vulnerability goes beyond a single issue.It demonstrates that AI security increasingly requires protections that adapt as fast as the threat landscape itself.
That is the model behind VibeSec: protections informed by emerging research, enforced during generation, validated during runtime, and backed by detection across the codebase.
With the continued acceleration of our development practices, in particular as it relates to use of AI, we finally need to embrace the mindset of preventing the next class of vulnerabilities as they emerge, not just after they’re exposed somewhere. That’s what security at AI speed looks like.
For more information, watch our Field CTO Chris Lindsey highlight how VibeSec protects against the Anthropic MCP vulnerability, or request a demo to see for yourself.

)



