This post by OX Research team was published on Dec 24, 2025
Attackers Could Exploit Zlib To Exfiltrate Data. CVE-2025-14847
Attackers Could Exploit Zlib To Exfiltrate Data
TL;DR
Critical MongoDB Memory Leak
The Situation: A major vulnerability allows unauthenticated attackers to remotely leak sensitive data from MongoDB server memory. No login is required.
CVE: CVE-2025-14847
The Story: A flaw in zlib compression allows attackers to trigger information leakage. By sending malformed network packets, an attacker can extract fragments of private data.
Affected Packages
| Major Version | Affected Versions | Fixed Versions |
| 8.2 | 8.2.0 to 8.2.2 | 8.2.3 |
| 8.0 | 8.0.0 to 8.0.16 | 8.0.17 |
| 7.0 | 7.0.0 to 7.0.27 | 7.0.28 |
| 6.0 | 6.0.0 to 6.0.26 | 6.0.27 |
| 5.0 | 5.0.0 to 5.0.31 | 5.0.32 |
| 4.4 | 4.4.0 to 4.4.29 | 4.4.30 |
| 4.2 | 4.2.0 and later | N/A |
| 4.0 | 4.0.0 and later | N/A |
| 3.6 | 3.6.0 and later | N/A |
Overview
A flaw in the zlib library enables attackers to leak information from MongoDB servers, the attacker can send the payload, without authentication, as the bug is exploited on the network level.
Who is affected
Any server with a publicly exposed MongoDB port for MongoDB servers within the affected versions list, and also private servers where attackers might reach through lateral movement.
What is the potential damage
Attackers can exploit this to extract sensitive information from MongoDB servers, including user information, passwords, API keys and more. Although the attacker might need to send a large amount of requests to gather the full database, and some data might be meaningless, the more time an attacker has the more information could be gathered.
Recommended Actions
Immediate Actions:
- If you have a publicly exposed MongoDB server within the affected packages – update immediately to the fix version
- Close ports that are not in use that might be used by attackers to send direct network requests to the MongoDB server
- If possible – disable zlib compression in your servers, although it might affect performance, it could help mitigate these kind of attacks
Technical Analysis
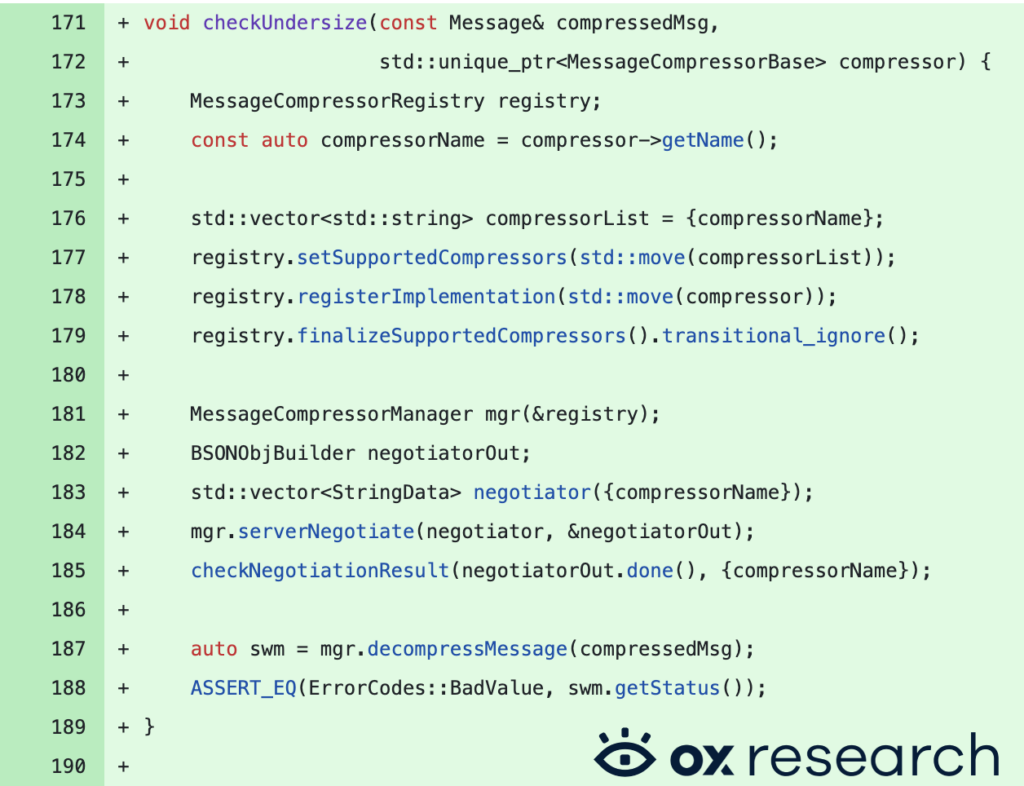
This commit containing the fix is a security and stability patch for MongoDB’s network transport layer. It addresses a vulnerability where the database could be forced to allocate or process “undersized” or memory buffers during the decompression of network messages.
The fix addresses an issue in message_compressor_zlib.cpp, the line that was originally used to return the size of decompressed data used the line – “return {output.length()};”, this tells the code to return the amount of allocated memory instead of the actual length of the decompressed data, the new line – “return length;” ensures that only the real length of the decompressed data will be returned.
src/mongo/transport/message_compressor_zlib.cpp

Source: https://github.com/mongodb/mongo/commit/505b660a14698bd2b5233bd94da3917b585c5728
Further analysis can show the code used to test the undersize memory corruption inside src/mongo/transport/message_compressor_manager_test.cpp, where the compressor code is fed with malicious values to check if the memory allocation issue still occurs.
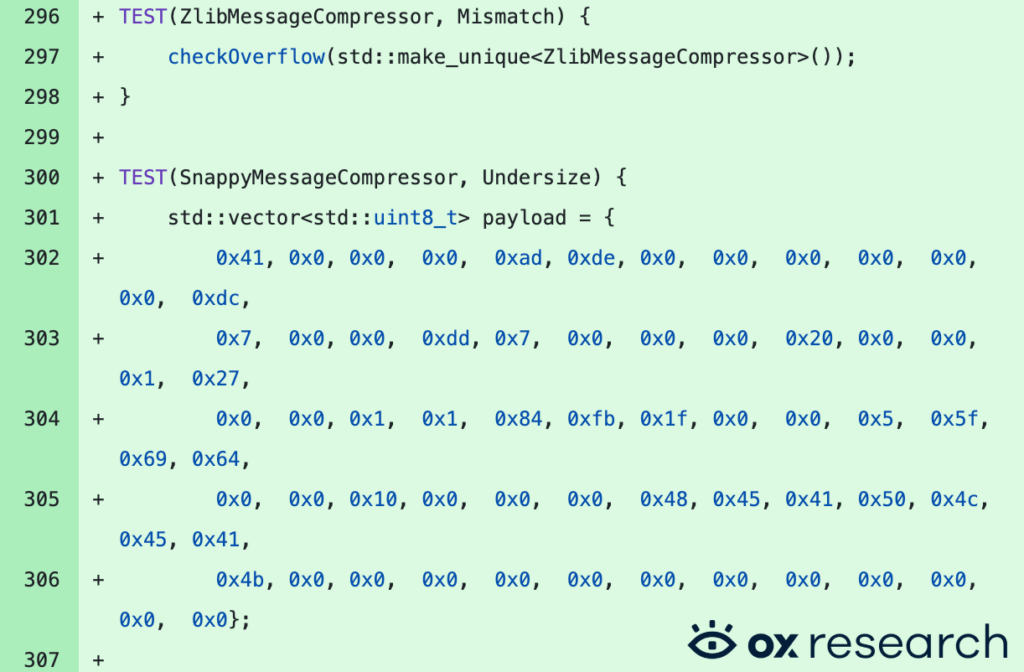
Source: https://github.com/mongodb/mongo/commit/505b660a14698bd2b5233bd94da3917b585c5728
Worried your environment was exposed? Contact us to validate your exposure and understand the impact.
Conclusion
What happened: A major vulnerability allows unauthenticated attackers to remotely leak sensitive data from MongoDB server memory (CVE-2025-14847). No login is required.
If you are using MongoDB, update to the latest fix version or disable zlib decompression.