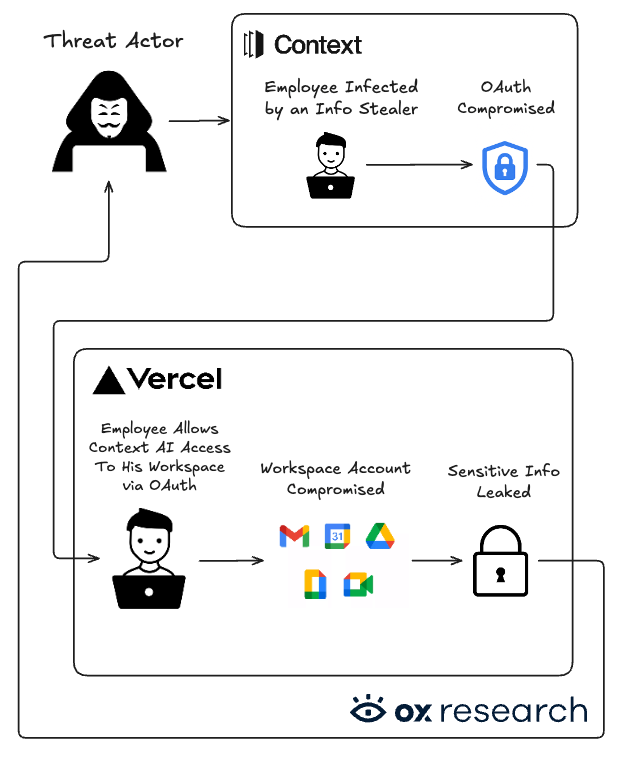
A compromised Context AI employee triggered a chain of events that reached a Vercel employee’s Workspace account, leading to a Vercel database breach now being sold on BreachForums for $2M
Breaking News: Breaking News: Vercel and Context AI were breached; Vercel’s internal database containing user data is now being sold on BreachForums for $2M
Overview
On April 19, 2026, Vercel, a web development platform that enables developers to host and scale websites, announced it was breached via a third party, Context AI, which was also breached.
A Vercel employee used Context AI with his Vercel Enterprise Google account and gave Context AI full read access to his Google Drive. Context AI disclosed that they experienced a security incident last month, in which an unauthorized actor gained access to their OAuth tokens, enabling access to a subset of users on their legacy and experimental products.
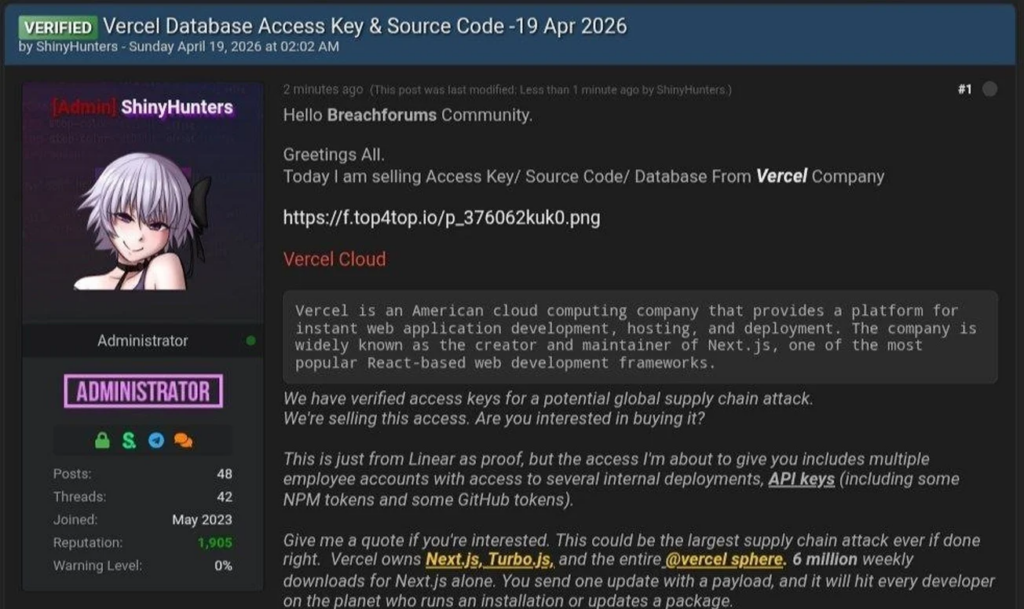
Following the breach, threat actors posted the leaked Vercel database for sale at $2M on BreachForums, a well-known hacker forum used to buy and sell stolen data.
While Vercel stated that their software remained safe, the full impact remains unknown. Threat actors getting access to their internal database might imply that other assets were compromised as well – including API keys, GitHub tokens and NPM accounts. Popular packages maintained by Vercel, such as Next.js, Turbopack, AI SDK, should be used cautiously and pinned to specific versions, to avoid future supply chain attacks.
Our research is based on our own threat analysis, alongside information gathered from Vercel, Context AI, Hudson Rock, and Jaime Blasco (@jaimeblascob on X).
Who is affected
While Vercel and Context AI stated that a limited subset of customers were affected, we cannot confirm whether the threat actors gained access to any other networks or internal tooling.
Our recommendation is that Vercel and Context AI customers should consider themselves breached and remediate accordingly.
Remediation
Recommended Actions
Immediate Actions:
- Rotate your keys immediately. Enable 2FA where possible
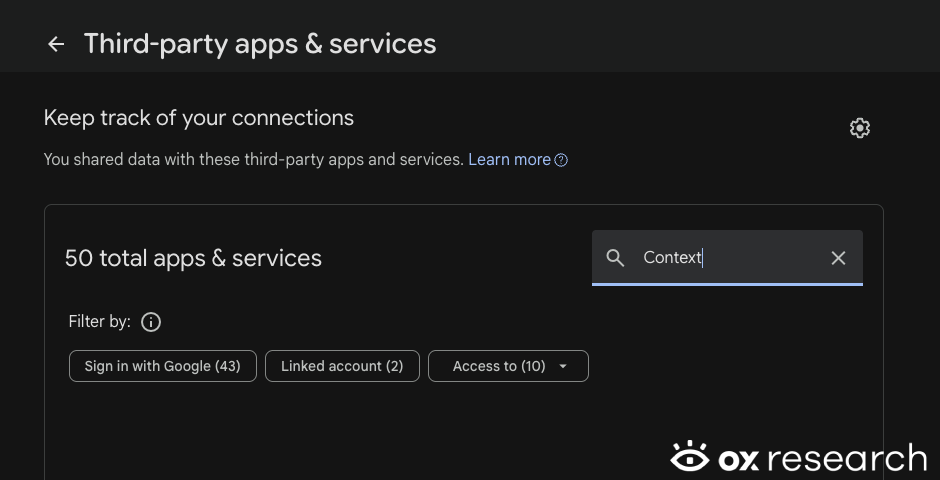
- Check your Google Account third party apps for the following ID or application name:
- 110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com
- Context AI
- Check if the Context AI Chrome Extension was installed:
- omddlmnhcofjbnbflmjginpjjblphbgk
- Treat Vercel and Context AI apps, connected databases and API Keys as compromised
- While Vercel and Context AI said that a limited number of customers were affected, we still don’t know the full scale of this breach
- Make sure packages maintained by Vercel are pinned to a specific version
NPM examples:
- Next.js
- SWR (stale-while-revalidate)
- Turborepo
- AI SDK
- A list of Vercel NPM packages can be found here: https://www.npmjs.com/~vercel-release-bot
Important Note
Key rotation and checking for the compromised Google App ID are recommended for any organization or individual, not just Vercel customers. As supply chain attacks become increasingly common, regular key rotation is a must for any organization’s security.
Remediation Steps
Check for the Context AI Google Oauth Application
Check for the Context AI Google Oauth Application
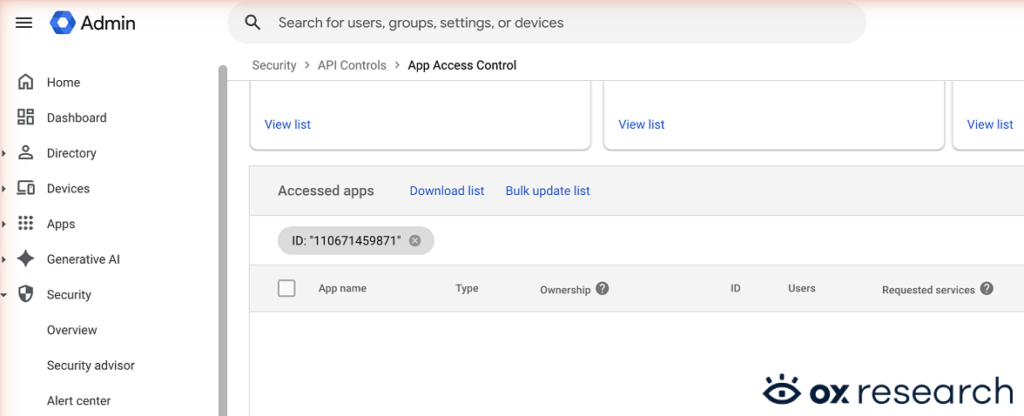
For Google Admins
- Enter admin.google.com and navigate to:
- Security
- Access and Data Control
- API Controls
- Manage Third-Party App Access
- Then filter the accessed apps by the following compromised Context AI Google App ID:
- 110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com
For Personal Google Accounts
- Enter myaccount.google.com/connections
- Filter by Context AI to check if you gave Context AI access to your Google Drive
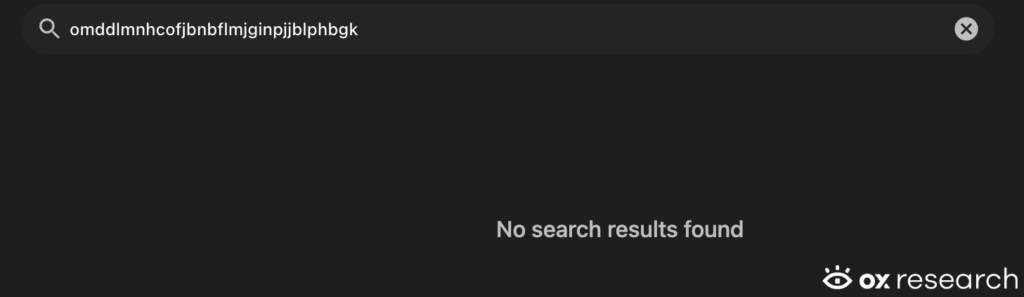
Check if the Context AI Chrome Extension was installed
- Open the Chrome browser and browse to chrome://extensions/
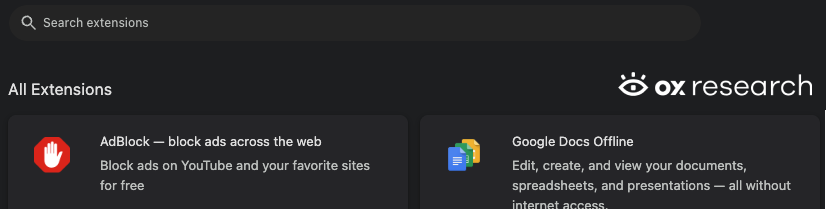
- Filter by Context AI’s name, or extension ID – omddlmnhcofjbnbflmjginpjjblphbgk
Threat Analysis
Vercel Incident Flow
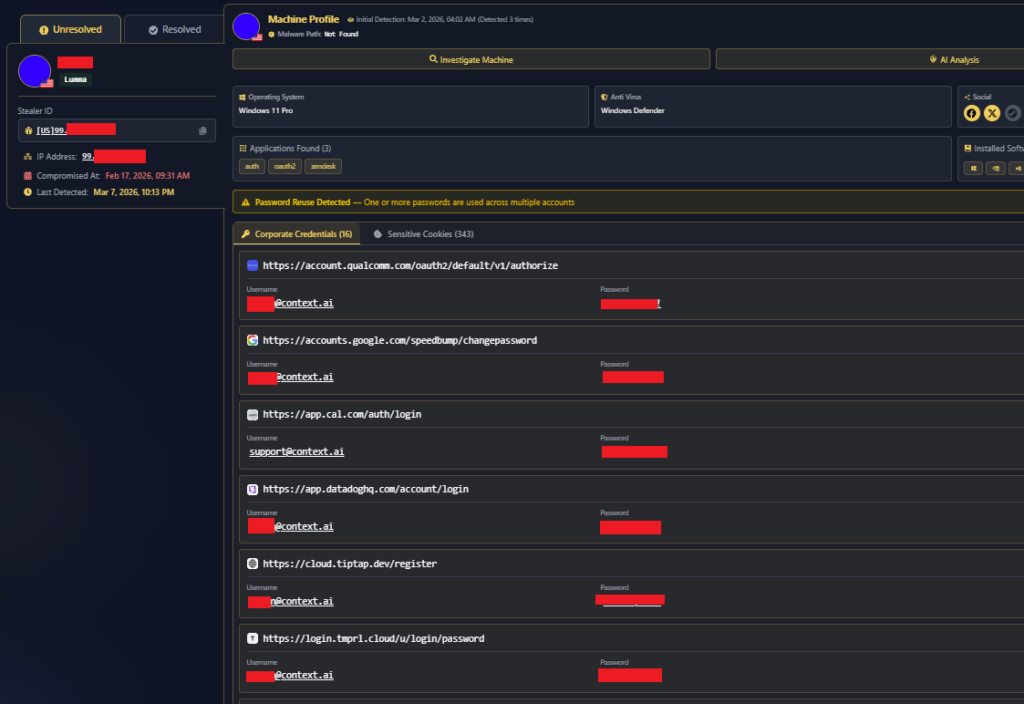
- Initial compromise (Context.ai): An employee of Context.ai was targeted after downloading game exploits, resulting in device compromise and credential exposure.
- Credential exposure: Data extracted from the compromised machine (per Hudson Rock analysis) included Google Workspace credentials and login details for multiple applications.
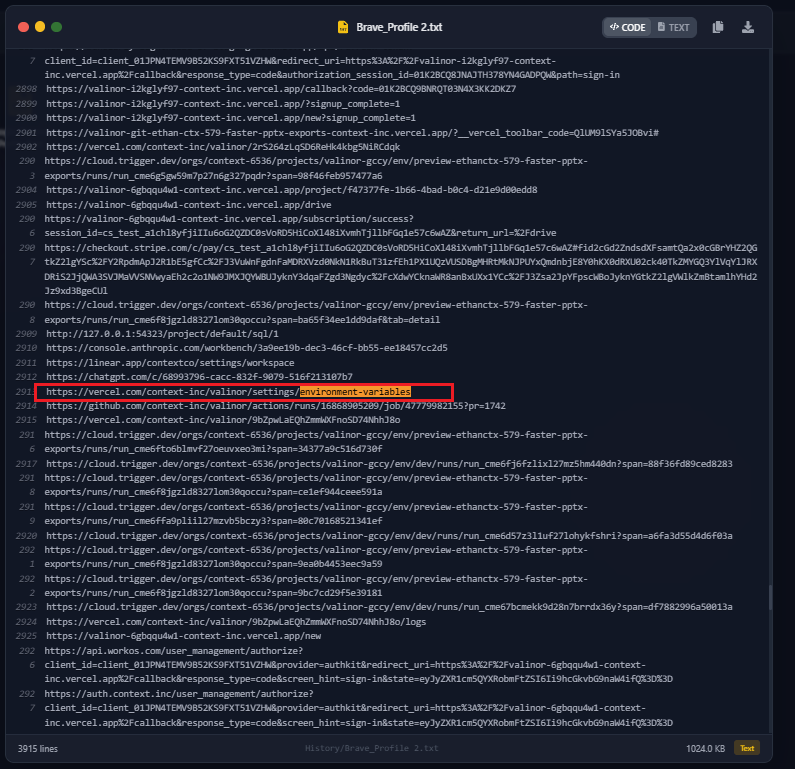
- Transition to Vercel: A Vercel employee installed a browser extension linked to the Context.ai incident environment, which enabled the attacker to gain access and pivot into the employee’s Vercel Google Workspace account.
- Internal access: Once inside Vercel, the attacker accessed environment variables that were not marked as sensitive and were not encrypted at rest.
- Privilege expansion: The attacker enumerated these variables and used them to expand access within the environment.
- Escalation: The attacker later claimed on BreachForums to have obtained a Vercel database access key and portions of source code.
Lumma Stealer deployment refers to the methods threat actors use to install malware on victims’ machines. There are several common ways this attack is carried out:
- Phishing and fake downloads: Attackers trick users into installing the malware by disguising it as legitimate software.
- Bundling with cracked or pirated software: The malware may be embedded in game cheats, cracked applications, and similar files.
- Distribution via social platforms: Malicious files are shared through platforms such as Discord, Telegram, and online forums.
In the case of Context.ai, an employee was targeted after downloading game exploits. This initial compromise allowed the attackers to gain access to a large number of the company’s credentials.
While analyzing the data extracted from the compromised machine, it was found – based on HudsonRock’s findings – that it included Google Workspace credentials, along with keys and login details for several applications:
The initial access began when a Vercel employee installed a malicious browser extension linked to a breach at Context.ai. This enabled the attacker to gain access and pivot from Context.ai-related access into the employee’s Vercel Google Workspace account, ultimately leading to the compromise.
After gaining initial access, the attacker was able to access environment variables that were not marked as sensitive and, therefore, were not encrypted at rest. Although these variables were not intended to contain sensitive information, the attacker was able to enumerate them and use the data to gain further access.
According to the attacker’s post on BreachForums, the intrusion led to access to a Vercel database key as well as source code.
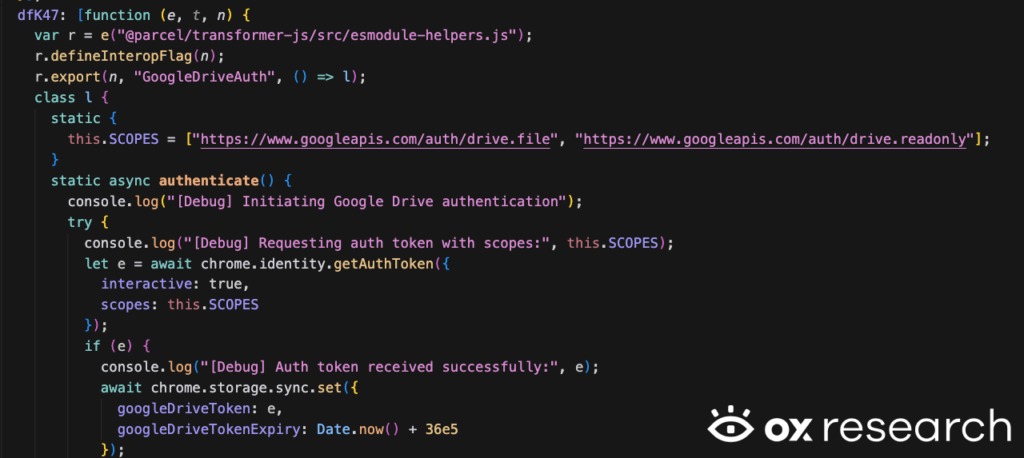
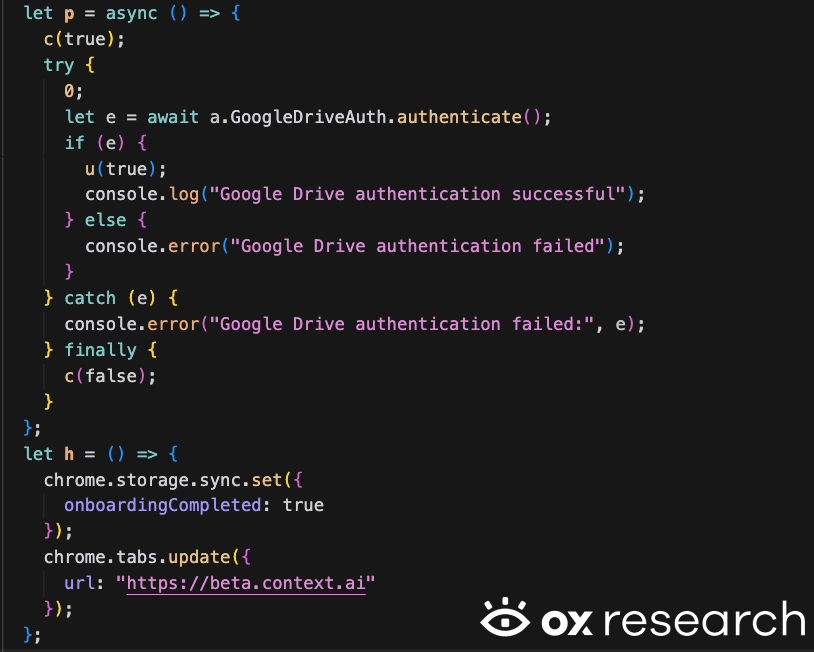
Context AI – Chrome Extension
The IOC referenced on Vercel’s website can be found inside the Context AI Chrome Extension (omddlmnhcofjbnbflmjginpjjblphbgk). The extension was removed on March 27, 2026, and allowed users to search and gather information from their Google Drive files and documents.
The extension used an OAuth2 Google App login. Users logging in this way granted the Context AI app full read access to all of their Google Drive files.

Source: Context AI Chrome Extension
During the onboarding process, users were required to connect their Google account and allow access to Google Drive.
Upon completing onboarding, users were redirected to beta.context.ai.
As of April 20, 2026, the beta.context.ai URL is no longer accessible.
IOCs
- Context AI Google Drive OAuth
- 110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com
- Context AI Chrome Extension
- omddlmnhcofjbnbflmjginpjjblphbgk
Conclusion
The latest Vercel and Context AI breach shows a clear common pattern in AI systems and supply chain security.
As we’ve seen in our latest MCP supply chain research, AI based systems are being shipped faster than their security review and process capabilities.
Context AI’s breach isn’t a one off attack, it’s a systematic process built by threat actors, to compromise, breach, and perform lateral movement inside and between organizations, as they did in the Axios, Trivy and Shai Huluid attacks in the last year.
Rotating keys, enabling 2FA and auditing your 3rd party connections has moved from being a recommendation to a survival tactic in 2026. Organizations that want to protect themselves from being the next Vercel or Axios should implement best practices for their security immediately.
References
https://vercel.com/kb/bulletin/vercel-april-2026-security-incident