TL;DR
- Since the past six months, container security has shifted from simply scanning the images to considering the full context: how containers are built, the dependencies they bring in, and the systems they communicate with. Teams now realize that issues hardly ever come from the container itself; they often start with the pipeline, the registry, or the code behind it.
- Image scanners find vulnerabilities, but they don’t show which ones can actually be reached at runtime. OX Security links every issue to the commits, build steps, and workloads involved, helping teams tell the difference between a harmless CVE and one that could impact production.
- Container images still have the usual risks, such as outdated libraries, loose instructions, and missing health checks. But what’s now important is how quickly teams can trace the problem back to its source and fix it. OX gives developers that upstream visibility without slowing them down.
- Build pipelines have quietly become a top target for attackers because they are the entry point for code, secrets, and images in the container lifecycle. OX’s real-time triggers monitor your pipeline and immediately flag leaked secrets, risky image changes, and misconfigurations before they reach production.
- OX’s container triggers give you real-time visibility into new vulnerabilities, misconfigurations, and secrets during builds, helping you catch and fix issues faster.
- This article looks at five enterprise-ready container security platforms: OX Security, Aqua Security, Sysdig, Wiz, and Prisma Cloud, to see how each approaches container protection and where OX stands apart for large-scale environments.
Containers are a common way to package and run applications across teams. They make it easier to ship software that behaves the same across environments, but they also introduce risks that can spread quickly if not handled early. The Cloud Native Computing Foundation (CNCF) reports that 89% of organisations use cloud-native technologies, and 93% are either using, piloting, or analysing container-based platforms in production. With this scale of adoption, the attack area expands to every container image, registry pull, misconfigured deployment, and potentially exposed runtime service. According to a SentinelOne article, 87 % of container images in production contain high or critical security vulnerabilities.
This is why organisations use container security products and services to protect their environments. These solutions aim to protect the full lifecycle of container workloads, including image build, registry validation, deployment posture, runtime behaviour, and supply-chain integrity. Yet many AppSec and platform teams express frustration about alert overload, noting that
“these scans have so many false positives, and CVE scores are incredibly inaccurate. You need to do a proper look at the attack surface and what actually runs.” Reddit
This highlights growing tool fatigue, a flood of low-value findings, and the constant risk of missing truly exploitable issues.
OX Security links vulnerabilities, secrets, and misconfigurations to their code origin, CI/CD pipelines, and runtime context, giving teams actionable clarity rather than isolated findings. Instead of reacting to raw alerts, teams understand impact, ownership, and the path to resolution.
This article will break down the main risk domains in container-native environments, outline what an enterprise-ready container security solution should bring, compare leading tools in the ecosystem, and show how OX Security positions itself uniquely for large-scale teams building at speed.
Key Risk Domains in Containerised Environments
Containerised workloads bring speed and scalability, but each layer opens up a new series of risks. Enterprises too often underestimate the risk that a single ignored misconfiguration or outdated dependency can expose their environments. Below are the main risk domains every container security solution must address:
1. Image Risks
Container images are at the heart of every deployment, so any weakness in them can affect everything else. Outdated libraries, unpatched dependencies, or missing Software Bill of Materials (SBOM) info make it difficult for teams to understand what they are actually shipping. The 2025 Sysdig Cloud-Native Security and Usage Report found that 87% of container images in production have high or critical vulnerabilities because older base images are reused without visibility into what has changed.
OX Security links every image issue back to its originating commit and build pipeline, giving teams clarity on how and where a vulnerability entered. Container Security Triggers flag exposed secrets, outdated packages, and policy violations inside the image, helping developers act before risky artifacts reach deployment.
2. Configuration and Misconfiguration Risks
Misconfiguration remains one of the fastest ways for an attacker to gain unintended access. Privileged containers, unsafe capabilities, exposed ports, or incorrect namespace assignments can create pathways into the cluster. A single insecure deployment can escalate into full workload compromise if left unchecked.
OX Security watches configuration changes regularly and alerts the moment a deployment drifts from your baseline. Its Container Security Triggers shows issues such as containers running as root or workloads opening sensitive ports, helping teams catch misconfigurations before they are exploited.
3. Runtime and Behavioural Risks
Once containers are running, traditional scanning stops being useful. Runtime risk comes from active behaviours like lateral movement between pods, data exfiltration, or execution of malicious binaries. According to the Sysdig 2025 Cloud-Native Security and Usage Report, “cloud attacks are now being detected, investigated, and mitigated within 10 minutes” in many environments.
OX Security keeps runtime activity visible through ongoing scanning and event-driven triggers. When a secret leaks, a binary changes, or a container drifts from its original image, OX raises an alert instantly, giving security and platform teams the context they need to respond with precision.
4. Supply Chain and Registry Risks
Public registries make it fast to get container images, but they also create supply-chain risks. Using an unsigned or unverified base image can introduce hidden backdoors, compromised layers, or untrusted build origins into your environment. Without artifact lineage (a record of an image’s complete history), teams cannot trace where an image came from or who modified it.
With OX Security, every artifact is tied to a verifiable origin. The platform maps images to their build pipelines, commits, and registry sources so teams always know who built what and when. This prevents unverified images from entering production and reduces the risk of third-party supply-chain attacks.
5. Prioritisation and Noise
The majority of enterprises fail because they can’t decide which alerts are impactful. Traditional image scanners analyse container images for known vulnerabilities, but they generate thousands of findings, many of which are unreachable, already fixed, or irrelevant at runtime. Out of context, teams will spend time pursuing an alert that is not a genuine threat.
OX Security focuses on the small issues that have a meaningful impact. Its contextual prioritisation engine evaluates exploitability, reachability, and the importance of the affected workload, highlighting only the ~5 % of vulnerabilities that could cause real damage.
What an Enterprise-Grade Container Security Solution Should Cover
1. Unified Coverage Across Build-to-Runtime
A complete container security solution must secure every stage of the lifecycle, from code and image build to runtime. Scanning once isn’t enough when every deployment introduces new dependencies or registry pulls.
OX Security bridges these stages under one visibility pane, connecting images, code, and runtime in a single flow.
With this unified approach, enterprises:
- Cut fragmented tool use and centralise visibility.
- Detects image-to-runtime drifts immediately.
- Reduce overall security debt by up to 95% through contextual visibility.
2. Deep CI/CD Integration
Security checks should run across the pipeline code → build → deploy to stop issues early instead of reacting post-release.
OX’s Container Security Triggers automatically activate scans when a vulnerability, secret, or misconfiguration appears.
Example outcomes:
- CI/CD pipelines catch and block unsafe container images before deployment.
- Real-time triggers replace scheduled scans, lowering fix time from weeks to days.
3. Intelligent Prioritisation
Finding every CVE is easy. Knowing which ones matter is not.
OX Security focuses on the 5% of vulnerabilities that pose actual runtime risk.
Its contextual prioritisation engine evaluates:
- Exploitability: Is the vulnerability reachable?
- Business context: Does it affect critical workloads?
- Runtime exposure: Is the vulnerable component active?
This lets AppSec teams focus on what’s exploitable, not just what’s listed.
4. Automated Response and Developer Workflows
Security shouldn’t hinder or interfere with developer speed. OX Security provides AI-driven remediation and no-code workflows that:
- Create JIRA or GitHub issues automatically.
- Trigger patch or rollback playbooks.
- Notify responsible teams via Slack or email.
This keeps teams fixing issues in-flow, avoiding handoffs between tools.
5. Regular Monitoring and Runtime Posture
Once deployed, containers continue to evolve, configurations drift, images update, and workloads change.
OX’s Container Security Triggers provide regular runtime scanning, detecting:
- Secret leaks in active workloads.
- Unauthorised binary or library changes.
- Image drifts between deployment and runtime.
This live feedback loop helps teams move from reactive scanning to proactive defense, lowering the mean time to detect (MTTD) issues compared to periodic scans.
Leading Container Security Vendors and Tools
Snapshot of the Current Landscape
Enterprises have more container security tools available than ever, yet few provide complete coverage across the build-to-runtime lifecycle. Below is a look at five major container security vendors and how they compare to OX Security, which adds contextual prioritisation and developer-ready automation.
| Vendor | Coverage Scope | CI/CD Integration | Prioritization Model | Enterprise Readiness |
| OX Security | Unified AppSec, container, and supply chain security | Built-in CI/CD triggers, deep pipeline integration | Contextual: focuses on the 5% of exploitable vulnerabilities | Strong fit for large teams needing preventive measures, SBOM validation, policy enforcement, and unified visibility across development and deployment. |
| Aqua Security | Strong for image, runtime, and Kubernetes hardening. | Moderate integration via Jenkins, GitHub Actions | CVSS-based, limited runtime context | Works well for compliance-driven enterprises, less aligned with developer-led pipelines. |
| Sysdig Secure | Deep runtime visibility with Falco-powered detection. | High; integrates with CI/CD and Kubernetes | Runtime-focused rather than code/path-aware. | For teams prioritising runtime threat detection over shift-left coverage. |
| Wiz | Broad cloud + container visibility via agentless scans. | Smooth SaaS integrations for multi-cloud setups. | Broad risk correlation but limited container depth | Strong for cloud posture leadership, lighter for hands-on container remediation. |
| Prisma Cloud (Palo Alto) | Full CNAPP (Cloud-Native Application Protection Platform) stack across cloud, IaC, and containers. | Enterprise-grade with tight network security integration | Rule-based prioritisation, less contextual | Ideal for governance-heavy orgs; slower developer adoption due to platform complexity. |
| Anchore Enterprise | Image scanning, SBOM generation, supply chain policy | Basic CI plugins for image gatekeeping. | CVE-based, no runtime intelligence | Trusted in regulated and air-gapped environments where SBOM accuracy is a priority. |
Observations
Most container security tools focus on scanning and listing vulnerabilities, but rarely help teams understand which ones truly matter.
While Sysdig and Aqua provide strong runtime defence, they still lack clear links back to the code or CI/CD source. Many tools also miss developer-friendly remediation, sending alerts without showing how to fix them. This leads to duplicate findings, inconsistent data, and tool sprawl.
OX Security solves this by connecting image, runtime, and pipeline visibility in one place, using its VibeSec approach to keep security aligned with development speed.
How OX Security Outperforms Other Container Security Solutions
Traditional container security tools often work in isolation, forcing teams to juggle multiple dashboards and alerts. OX Security takes a different approach with its VibeSec model, which fits naturally into how software is built and shipped.
- Unified visibility: OX brings container, code, and cloud signals together in one view. This single-pane visibility helps teams trace vulnerabilities back to their origin and understand their impact across the stack.
- Prioritisation engine: Instead of listing every issue, OX highlights only what’s exploitable or reachable in runtime. This reduces the noise and focuses attention on the 5% of threats that can actually have an impact.
- Developer adoption: OX integrates directly into existing workflows with no-code automation and AI Remediation. Developers can fix issues where they work, keeping builds smooth and uninterrupted.
- Scalability: Built for enterprise scale, OX connects to move than 100 integrations across cloud, CI/CD, and security toolset. This makes OX flexible, whether needed for complex infrastructure or hybrid environments.
- Proven results: Many enterprises using OX report measurable improvements in risk reduction, including one customer stating they reached “zero critical vulnerabilities for the first time.”
Container Security Solutions for Enterprise Pain Points
Enterprises often face overlapping risks and tool fatigue when protecting containers. This table breaks down the most common pain points and how OX Security’s unified approach simplifies each challenge.
| Enterprise Pain Point | What Typical Tools Do | How OX Solves It |
| Tool sprawl | Multiple scanners and dashboards | Unified visibility and workflow automation |
| Alert fatigue | Thousands of low-value alerts | Prioritised 5% of critical issues |
| Lack of runtime view | Stops at build-time scans | Regular runtime monitoring |
| Compliance and reporting | Manual exports | Built-in dashboards and risk summaries |
| Developer friction | Separate tools and plugins | Native CI/CD integration and AI Remediation |
Top 5 Enterprise-Ready Container Security Tools
1. OX Security
Overview
OX Security is an Active ASPM (Application Security Posture Management) platform built for enterprise AppSec and Platform Security teams managing large-scale development organizations. It secures software from code to production by correlating risks across source code, CI/CD pipelines, container registries, and runtime workloads showing AppSec leaders which vulnerabilities are actually exploitable rather than flooding teams with theoretical findings.
OX operates on the VibeSec principle: security adapts to developer workflows rather than blocking them, embedding checks directly where engineers already work (IDE, Git, pipelines, clusters). For Heads of Product Security overseeing hundreds or thousands of developers, OX provides unified governance, automated remediation, and audit-ready compliance across polyglot codebases, multiple CI/CD systems, and hybrid cloud environments.
This active approach ensures vulnerabilities, misconfigurations, and secrets are detected early, prioritised by business impact, and remediated through automated workflows, all without interrupting developer velocity.
Why Choose OX Security
- End-to-end lineage: OX links vulnerabilities to their exact origin across code → pipeline → image → runtime, giving AppSec and Platform Security teams far more context than isolated CNAPP or SCA tools that operate in silos.
- AI-native security architecture: One of the few platforms that treats AI model artifacts, vector databases, PBOM/SBOM, and inference APIs as first-class security assets critical for enterprises adopting AI coding tools and LLM-powered workflows.
- Active ASPM for full lifecycle coverage: Strengthens both shift-left and shift-right simultaneously by preventing issues during creation, validating them in pipelines, and correlating findings with runtime exploitability.
- Built for enterprise scale: Handles polyglot codebases, multiple CI/CD systems (GitHub Actions, GitLab CI, Jenkins), hybrid cloud environments (AWS, Azure, GCP), and thousands of daily builds without creating bottlenecks or requiring platform standardization.
- Governance without friction: Enforces security policies automatically inside developer workflows (IDE, Git, pipelines) using the VibeSec principle—security adapts to how teams build rather than blocking velocity.
- Audit-ready compliance: Maintains complete audit trails across the SDLC for SOC 2, ISO 27001, PCI-DSS, and other frameworks, turning manual compliance reviews into automated evidence collection.
Pros
- Contextual prioritization: Shows only exploitable and reachable issues by correlating runtime exposure with build-time findings—eliminating the noise that buries AppSec teams in thousands of unprioritized alerts.
- Preventive security at the source: Blocks insecure patterns directly in IDE or AI agent workflows before they reach CI/CD, catching AI-generated vulnerabilities at creation time rather than after deployment.
- Root cause tracing: Traces every vulnerability back to the exact commit, developer, or AI-generated change, enabling targeted remediation with automated ticket assignment and owner notification.
- Unified artifact protection: Secures containers, dependencies, secrets, and AI-specific build artifacts (models, embeddings, prompts) across the entire development lifecycle in a single platform.
- Small AppSec teams, large engineering orgs: Automates triage, remediation workflows, and policy enforcement so security teams outnumbered 50:1 or 200:1 can govern at scale without becoming bottlenecks.
- Multi-cloud and multi-pipeline visibility: Aggregates risk posture across fragmented environments—GitHub + GitLab + Jenkins, AWS + Azure + GCP, Docker + Kubernetes—giving leadership a single source of truth.
- Developer-friendly adoption: Integrates seamlessly into existing workflows with minimal configuration, reducing friction and shadow-security workarounds that undermine governance.
Cons
- As a newer solution, it is still gaining enterprise visibility compared to legacy vendors.
- OX focuses on breadth + correlation rather than deep runtime anomaly detection.
- Being a relatively new category (Active ASPM), some teams may require guidance during adoption.
2. Aqua Security
Overview
Aqua has been in the container security space long before AI pipelines became the norm. It is a well-established container security platform that provides image scanning, runtime protection, and Kubernetes security. It supports enforcing security policies during build and runtime to help teams maintain compliance and reduce risk. However, in the context of AI-heavy pipelines, Aqua’s strength lies largely on the runtime side rather than early pipeline correlation.
Why to Choose
- Aqua provides a strong baseline for enterprises with mature Kubernetes deployments.
- It provides advanced runtime protection that prevents container escapes and zero-day exploits.
- The platform enforces Kubernetes policies effectively, helping organisations align with compliance frameworks.
Pros
- Kubernetes controls: Powerful admission controls keep insecure workloads from entering production.
- Runtime protection: Instrumentation catches container escapes and suspicious process activity.
- Enterprise maturity: A stable product with proven deployment patterns for large organisations.
Cons
- Limited visibility into AI supply-chain layers, such as model artifacts or PBOM data.
- Does not correlate issues back to code commits or AI-generated changes.
- Remediation workflows depend more on manual triage, which is slower for high-velocity pipelines.
3. Sysdig Secure
Overview
Sysdig Secure is built around Falco’s behavioral detection to catch unusual container activity, such as unexpected syscalls or container behavior. It provides both agent-based runtime monitoring and CI/CD scanning for full container visibility. However, tools focused on runtime may still miss risks that start earlier in AI-driven pipelines.
Why to Choose
- Provides runtime visibility for teams using Falco-based monitoring, giving insight into container behavior.
- Detects anomalies, policy violations, and behavioral drift in real time.
- Enables DevOps teams to enforce runtime security policies effectively.
Pros
- Runtime visibility: Provides detailed insights across clusters to speed up incident investigation.
- Operational context: Integrates with Prometheus and Kubernetes metrics for a better understanding of cluster activity.
Cons
- Minimal AI-specific security support (vector DBs, model artifacts, prompt surfaces).
- Early-stage detection (before runtime) remains limited.
- No end-to-end correlation from code → pipeline → runtime.
4. Wiz
Overview
Wiz is a cloud-native application protection platform (CNAPP) that includes container visibility through agentless scanning. Reviewing Wiz from a DevSecOps lens, it provides strong cloud misconfiguration detection and identity correlation, but its container security layer is more cloud-contextual than pipeline-aware.
Why to Choose
- Wiz is designed for organisations seeking unified visibility across multiple clouds and containerised workloads.
- Its agentless scanning simplifies setup and speeds onboarding for distributed teams.
- Strong multi-cloud asset visibility, identity mapping, and compliance posture.
Pros
- Simplified onboarding: Agentless discovery makes setup faster and reduces operational overhead.
- Identity correlation: Provides strong cloud identity mapping for better security context.
- Regular compliance: Helps maintain compliance across hybrid cloud environments.
Cons
- Wiz provides limited insight into deeper container layers and dependencies.
- It lacks strong SBOM tracking and code-level correlation for vulnerability origin tracing.
- Agentless runtime depth is weaker than that of runtime-focused vendors.
5. Prisma Cloud (Palo Alto Networks)
Overview
Prisma Cloud is Palo Alto Networks’ CNAPP that secures containers, cloud workloads, and infrastructure-as-code configurations. It provides policy enforcement and compliance management across hybrid and multi-cloud environments. However, its container scanning and runtime layers are part of a larger suite that is not specifically tailored for AI-driven pipelines.
Why to Choose
- Prisma Cloud suits regulated enterprises requiring comprehensive compliance and IAM correlation.
- It provides detailed Kubernetes posture management and runtime protection capabilities.
- The platform provides a unified dashboard for large-scale container environments with compliance automation.
Pros
- Broad security coverage: Prisma Cloud protects cloud infrastructure, infrastructure-as-code (IaC), and container environments within a single platform.
- Prebuilt compliance: Provides ready-to-use frameworks and policies for standards like PCI-DSS and HIPAA.
- Integrated visibility: Works with Palo Alto’s network security stack for end-to-end visibility from code to cloud.
Cons
- Complex onboarding and configuration for distributed teams.
- No meaningful AI-specific artifact or inference API security features.
- Limited correlation between CI/CD changes and vulnerabilities in runtime workloads.
How to Choose the Right Container Security Vendor
When assessing container security vendors for enterprise environments, the goal is not just to compare features but to measure how well each solution fits your organisation’s scale, developer workflow, and risk tolerance. The following framework provides a structured way to assess potential vendors based on their technical coverage, usability, and operational maturity.
Build-to-Runtime Coverage (25% of total evaluation)
A strong vendor must secure every stage of the container lifecycle, from image creation to deployment and runtime. Evaluate whether the solution includes image scanning, registry validation, runtime protection, and drift detection across clusters.
- Look for support for container SBOM generation and regular runtime scanning.
- Vendors with build-to-runtime visibility reduce mean-time-to-detection by over 40% compared to those with build-only scanning.
Contextual Prioritisation (25% of total evaluation)
The best tools don’t just list vulnerabilities; they show which ones are exploitable. Prioritisation should combine exploitability, reachability, and business impact to cut noise and highlight real threats.
- Ask if the platform provides runtime correlation or “reachability analysis.”
- Vendors using contextual prioritisation reduce alert fatigue by up to 80% in enterprise teams.
Developer-Ready Workflows (20% of total evaluation)
Security should blend into existing CI/CD pipelines, not disrupt them. Evaluate how each vendor supports developers through automation, integrations, and guided remediation.
- Look for integrations with JIRA, GitHub, or Slack to streamline issue management.
- Teams adopting developer-centric workflows often fix vulnerabilities 3x faster than those relying on manual triage.
Proven Enterprise Scale (15% of total evaluation)
Enterprise environments demand scale across multiple pipelines, regions, and thousands of containers. Assess each vendor’s ability to handle complex topologies and integration depth.
- Check if the vendor supports hybrid or multi-cloud infrastructure.
- Vendors with proven scalability typically maintain 99.9% uptime and support integrations with 100+ tools.
Unified Platform vs Single-Point Tools (15% of total evaluation)
Consolidation reduces tool sprawl, cost, and operational noise. Choose vendors providing a unified platform that ties together code, cloud, and container security.
- Unified platforms can cut tool spend by 30–40% annually while improving mean-time-to-remediation.
- Look for solutions that provide visibility across the full software supply chain.
Using OX Security for Container Protection: Step-by-Step Guide
Follow this hands-on walkthrough to see how OX ingests container artifacts, runs image scans, shows container-specific alerts, ties findings back to commits, and automates remediation all inside the same platform. The steps below use a repository and a pushed image tag; OX performs container checks and shows container security issues in the dashboard and application views.
Step 1: Connect source control and registry
- Connect your GitHub repository to OX using the OAuth flow so OX can scan code and Docker files.
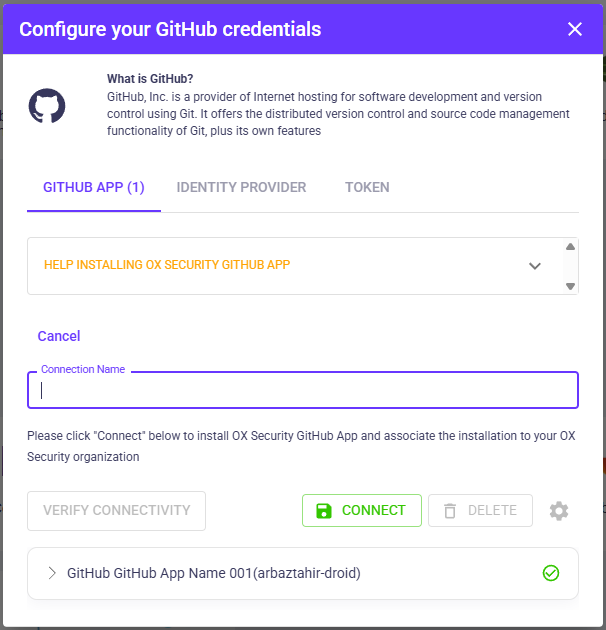
- Create a read-only registry token in Docker Hub (or GHCR) and add it to Configure → Connectors → Registry in OX. Use your username and the token as the password.
To create a read-only Docker Hub registry token
- Go to Docker Home and sign in.
- Go to Account Settings → Security → Personal Access Tokens.
- Click “Generate New Token”, give it a descriptive name, and select Read-only access.
- Click Generate, then copy the token (you won’t be able to see it again later).
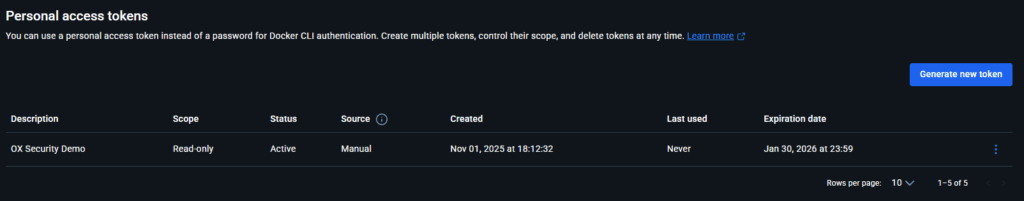
After connecting GitHub and Docker Hub, OX performs a scan and shows repository posture and registry ingestion status on the project dashboard.
Step 2: Confirm containers are assigned to the application
- Open Applications → select your app.
- In the right-bottom panel, open Containers and confirm artifacts are listed; if empty, use Assign Container to Repo and choose your image from the dropdown, and click Add. If the connector was newly added, press Reset Containers, then re-open the panel.
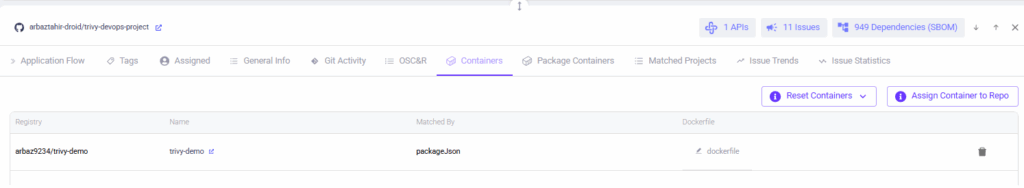
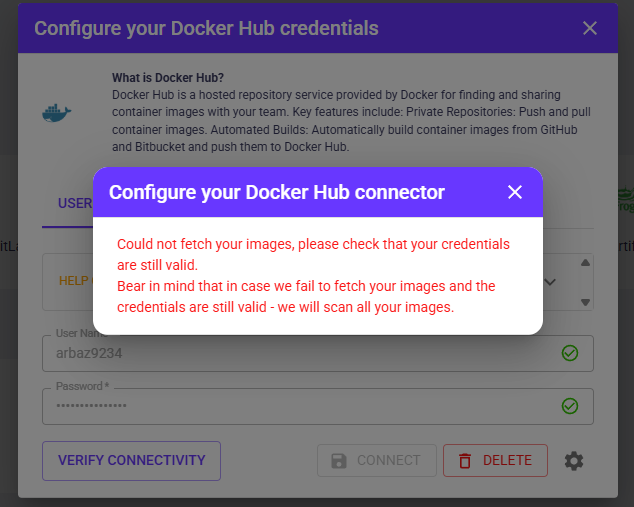
- If you cannot find a container image and the Assign Container dropdown is empty, check if Docker Hub is connected and the images are imported successfully. You may see the following error if not done correctly:
Step 3: Verify container security policies are enabled
- Go to Configure → Policies and open the active policy profile.
- Under Container Security, ensure the relevant checks are ON (vulnerable dependency, secret in container, misconfiguration, etc.).
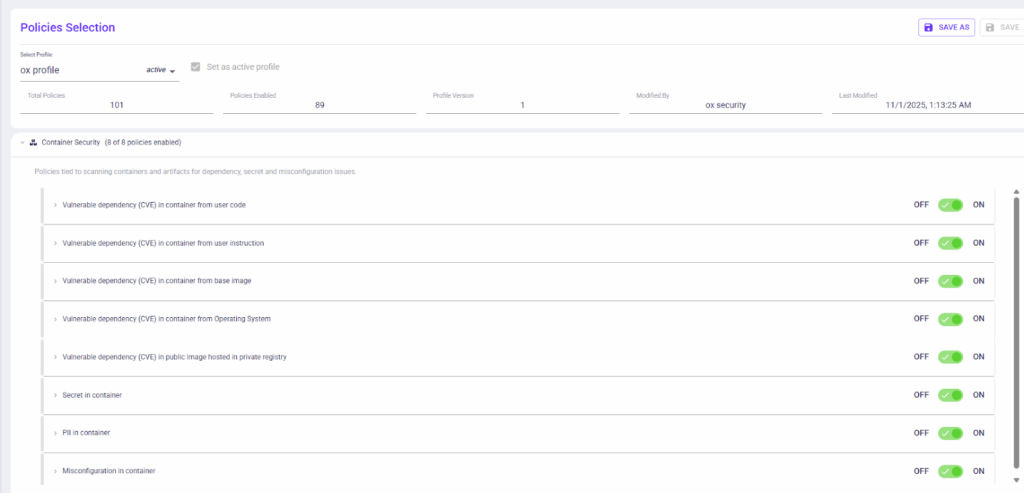
- Container security policies are active, so OX will detect secrets, vulnerable dependencies, and common misconfigurations in images.
OX will evaluate images against container security rules during scans.
Step 4: Run the image scan
- In Registry / Images, find the assigned image and click Scan or re-run the scan.
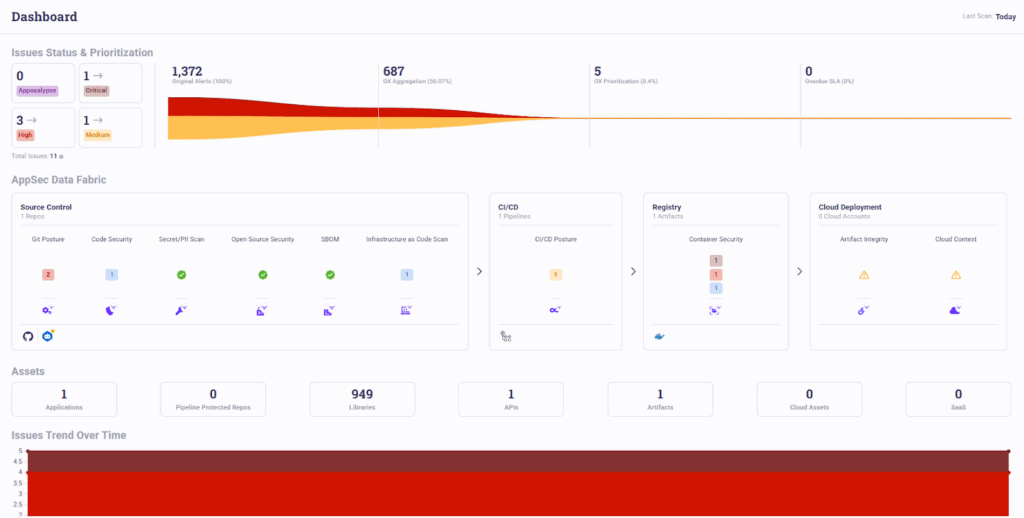
- Wait for the scan to complete and refresh the dashboard.
Dashboard showing AppSec Data Fabric, Registry counts, and container security tile with issue count.
OX updates the dashboard once image scans are complete, showing container security counts alongside code and SBOM metrics.
Step 5: Check container security issue statistics for the project
- Open your application and go to Issue Statistics or Issue Trends.
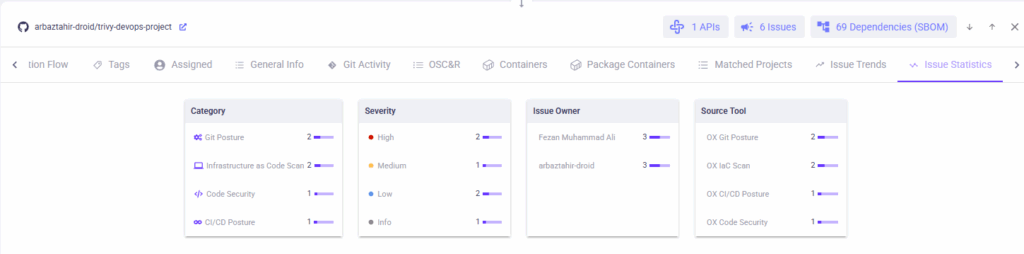
Issue Statistics panel showing Category = Container Security, severity breakdown, issue owner, and source tool.
Issue statistics for the repository show container security as a distinct category with critical and high severity counts for deeper triage.
Step 6: Check the full list of container security issues
- Open Issues → Active Issues and apply Category = Container Security.
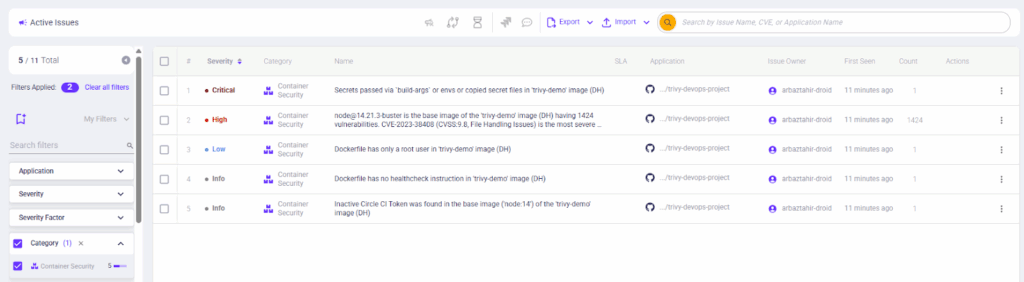
- The active issues view lists container findings such as secrets, outdated base images, and missing health checks, ready for triage.”
You can view and triage container issues the same way you do code or IaC findings.
Step 7: Expand a single issue and check the attack path
- Click an issue row (for example, “Dockerfile has no healthcheck instruction” or secret detection).
- Open the Attack Path tab to show relationships: app, SBOM, and registry artifact.
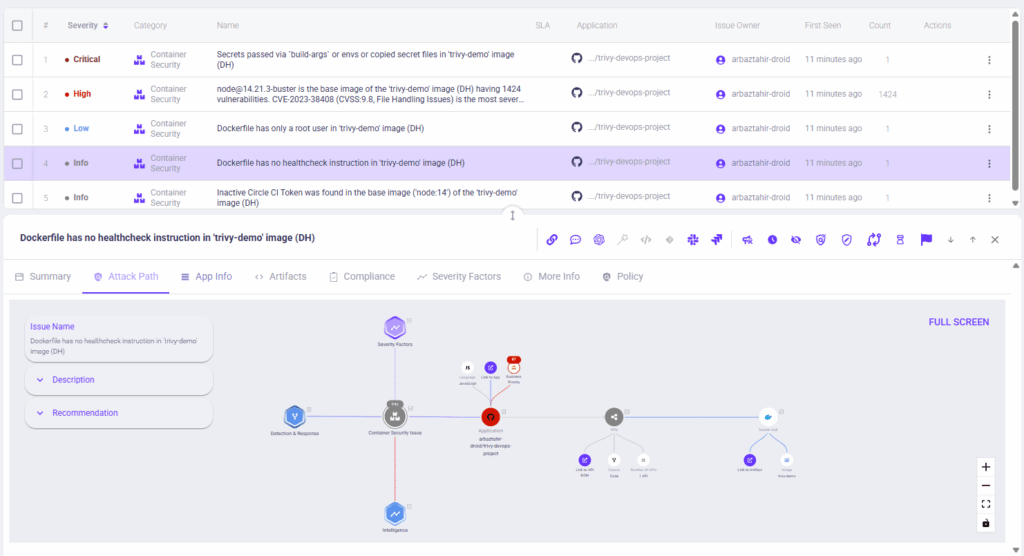
- The attack path links the container finding to the application, SBOM, and registry artifact, so you can see the impact and likely attack vectors.
OX visualises how a container finding could be exploited and what elements it touches in the software supply chain.
Note: The Attack Path panel displays related assets, detection context, and remediation suggestions. If the full graph isn’t visible in a static screenshot, remember that the interactive view allows you to zoom and see the entire attack path in detail.
Step 8: Automating Fix and Response (no-code workflow, optional)
- In Configure → Workflows, create or open a workflow triggered by a container event (secret or high CVE).
- Add actions: create a JIRA ticket, send a Slack message, or block artifact. Save and enable, then re-trigger the alert to capture a run.
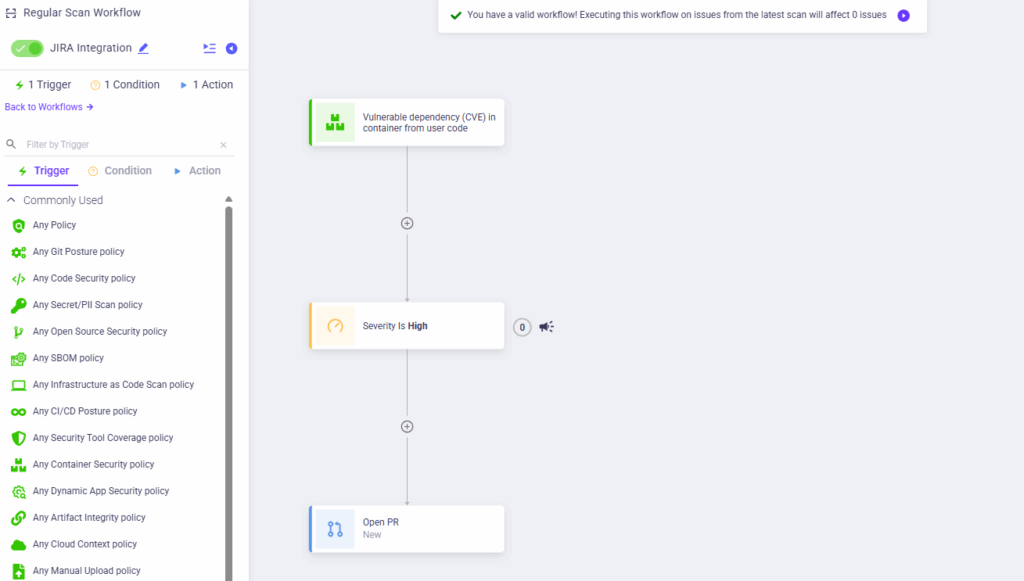
No-code workflow builder with trigger, conditions, and actions for automated remediation.
- Remediation can be automated and assigned to owners without manual handoffs.
Automated workflows let teams create tickets and notify owners when container rules trigger, keeping fixes inside the developer flow.
Best Practices for Container Security in 2026
Container security in 2026 is about precision and speed: protecting every build without slowing the release pipeline. The following practices help enterprises maintain secure, traceable, and efficient container operations.
- Embed scanning early (shift left into CI/CD): Integrate image and configuration scans directly into CI/CD so issues are caught before containers reach staging or production.
OX supports this by using its AI Security Agent to block unsafe patterns in the IDE and by using deep CI/CD integrations that automatically scan every build, commit, and artifact throughout the pipeline. - Maintain signed and accurate SBOMs and PBOMs: Up-to-date SBOMs and PBOMs give DevSecOps a clear view of container and model dependencies.
OX automatically generates and validates these SBOMs and PBOMs, links them to pipeline metadata in its AI Data Lake, and checks for any tampering before deployment. - Repeatedly verify runtime drift: Even well-built images can change at runtime because of misconfigurations, added libraries, or unexpected behavior.
OX connects code → pipeline → image → runtime to show meaningful drift, comparing what was built to what actually runs and highlighting only the deviations with real exploitability or reachability impact. - Correlate findings back to code and ownership: Fast remediation depends on knowing who owns an issue and where it came from.
OX links container and model vulnerabilities back to the repo, commit, and team that introduced them, helping DevSecOps fix problems quickly with a clear view of how each artifact was built and where it runs. - Automate repetitive remediation tasks: Routine issues like outdated base images, unpinned tags, or missing labels can be automated to reduce manual work.
OX uses no-code remediation workflows to auto-fix, block, or open pull requests, helping large engineering teams stay consistent at scale. - Use AI-driven prioritisation for focus: Apply contextual analysis and AI-based prioritisation to identify which vulnerabilities pose real runtime risk and focus on those first.
OX’s AI Data Lake connects code, SBOM/PBOM data, CI/CD events, and runtime telemetry to highlight only the vulnerabilities that are truly exploitable.
Conclusion
Securing containers is no longer optional; it has become an ongoing journey, integrated across code, build, deployment, and runtime phases. With thousands of containers, multiple teams, and cloud-native architectures, relying on fragmented tools can leave major risks hidden rather than under control. The current approach demands a platform that connects these layers, prioritises real risks, and allows developers to fix issues in their natural workflows.
This article covers the main risk domains in container environments, what a truly enterprise-grade container security solution must cover, how leading vendors compare, and why OX Security stands out with its unified, developer-first VibeSec platform.
OX Security provides exactly that with its VibeSec model: security that moves with development speed, not against it. By unifying image scanning, runtime protection, and contextual prioritisation under one platform, it helps enterprises focus on the vulnerabilities that matter most while lowering alert fatigue and operational overhead.
As 2026 unfolds, teams that embrace this connected, developer-friendly approach will spend less time chasing alerts and more time shipping secure, resilient software.