OX Security researchers discovered a Zero-Day vulnerability – CVE-2025-11158 -affecting 2,600+ publicly exposed Pentaho instances
TL;DR
The OX Research team exploited a remote code execution vulnerability – CVE-2025-11158 – in Pentaho: a zero-day vulnerability, related to CVE-2022-43938 (1-Day) allowing non-admin business users to run malicious Groovy scripts in reports — leading to full server compromise.
Severity: Critical – 9.1 CVSS
Affected Versions: All versions of Pentaho up to 10.2.0.6, including 9.3.x and 8.3.x
Patched version: 11.0
Impact: This vulnerability allow attackers to execute arbitrary code on the server, leading to full system compromise and potential data theft or malware deployment.
Overview
Pentaho is a widely used open source enterprise data integration and analytics platform that helps organizations access, prepare, and analyze data from multiple sources through tools like Pentaho Data Integration and Pentaho Business Analytics. It’s trusted across industries such as marketing, Financial Services, Healthcare, and more, and is used by thousands of companies worldwide, including many in the Fortune 100 for scalable data workflows and business intelligence. Its broad adoption by enterprises and diverse user base — from IT and BI teams to data engineers — reflects its role in helping organizations unify and derive insights from complex data.
Based on our Shodan search, we identified approximately 2,607 publicly exposed Pentaho instances, all of which are potentially vulnerable to remote code execution.
What We Found
During our analysis of the Pentaho Platform, the OX Research team identified a distinct remote code execution vulnerability affecting the product.
It is a 0-day vulnerability (CVE-2025-11158) related to CVE-2022-43938, which allows a user with the “Business User” role to achieve remote code execution. Despite the existence of a prior fix, we identified a technique that still enables the injection of malicious Groovy scripts into report files created with Pentaho Report Designer. When these reports are uploaded and processed by the server, the embedded Groovy code is executed, allowing arbitrary system commands to run.
This vulnerability leads to remote code execution on the Pentaho server and can result in full system compromise under realistic attack scenarios.
Who Is Affected?
All organizations running the Pentaho Platform – versions up to 10.2.0.6, including 9.3.x and 8.3.x – on publicly accessible servers are affected. The patched version is 11.0
Potential Damage
- Remote code execution on the Pentaho server
- Full system compromise with execution at the privileges of the Pentaho process
- Theft or manipulation of sensitive data processed by Pentaho
- Deployment of malware or persistence mechanisms on the server
- Lateral movement to other systems within the internal network
Responsible Disclosure
We contacted Hitachi Vantara on 15-Jul-2025, and they responded that a fix will be issued. On March 9, 2026 the fix was made publicly available.
Recommendations
- Apply the security patch from Hitachi Vantara.
- Limit access to Pentaho servers to trusted internal networks and avoid public exposure whenever possible.
- Restrict user roles and permissions, ensuring only trusted administrators have full access.
- Monitor and audit report uploads and database connection inputs to detect unusual or suspicious activity.
- Implement network segmentation and intrusion detection to reduce the risk of lateral movement in case of a compromise.
Technical Analysis – CVE-2025-11158
Attack Scenarios: How could this be exploited in the wild?
- A user with the Business User role can upload a malicious report file containing embedded Groovy code, which is executed when the report is processed by the server.
- Once code execution is achieved, an attacker can take full control of the Pentaho server, access sensitive data, deploy malware, and pivot to other systems within the internal network.
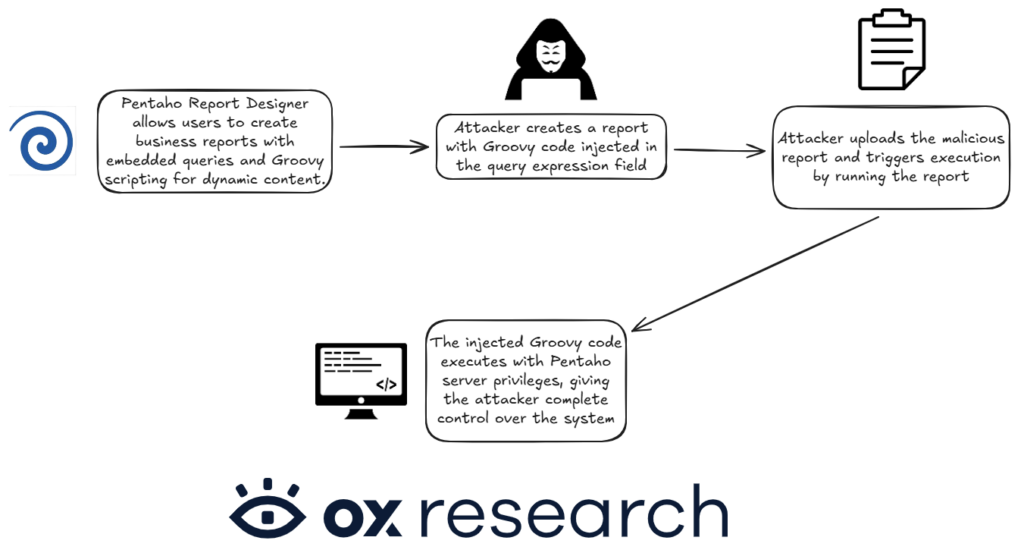
Attack Graph
How it works
The identified vulnerabilities in Pentaho stem from unsafe handling of user-controlled input in features that are designed to extend the platform’s flexibility, specifically database connectivity and report execution.
The vulnerability, relating to CVE-2022-43938, impacts Pentaho’s report handling functionality. Pentaho Report Designer allows users to create and upload reports that include data queries and logic. These reports support Groovy scripting, which runs on the Java Virtual Machine. Despite prior fixes, we identified a technique that allows a Business User to inject malicious Groovy code into the query section of a report file. When the report is uploaded and processed by the Pentaho server, the embedded Groovy script is executed with server-side privileges.
The core issue is that user-supplied input is executed by the backend without sufficient validation or sandboxing. This allows attackers to transform legitimate platform features into an execution vector, ultimately resulting in remote code execution and full system compromise.
RCE via Business User Role (Related to CVE-2022-43938)
We identified a technique by which a user with the Business User role can achieve RCE, using a method similar to that described in CVE-2022-43938, despite the applied fix.
Pentaho Report Designer allows users to create custom reports that include data queries and logic, which can then be uploaded and run on the Pentaho server. This feature introduces a serious vulnerability: attackers can inject malicious Groovy scripts into the query section of a report file.
When such a report is uploaded and processed by the Pentaho server-even by a non-admin “Business User” who has permission to upload reports-the embedded Groovy code is executed on the server. Because Groovy is a powerful scripting language that runs on the Java platform, it can be used to run arbitrary system commands.
As a result, this vulnerability enables remote code execution (RCE) on the server, allowing an attacker to potentially take control of the system, steal data, or perform other malicious actions-all by embedding code in what appears to be a regular report file.
Exploitation PoC
A PoC of the 0-day leading from business user to RCE on the server can be found here:
Too Good to BI True
This advisory is part of Too Good to BI True, OX Security’s research into the security posture of the most widely deployed open-source Business Intelligence platforms. Across five platforms, our researchers achieved full exploitation chains in every single one — reaching data that should never have been accessible. The findings include four zero-day discoveries and over 45,000 publicly exposed instances.
Read the advisories:


)