The MCP flaw hit organizations that did everything right. Here’s how to harden your architecture against it
During our recent research into MCP Supply Chain Vulnerability (download here), we found two AI systems – Flowise & Upsonic – that recognized the risk of passing user input directly to MCP STDIO configurations and took steps to address it.
In order to avoid RCE, both Flowise & Upsonic implemented the recommended approach: input sanitization. Any user input to a custom STDIO MCP goes through a series of checks, where only approved commands can pass (python, npx), and no special characters can be passed (&, |, >). This removed most of the attack surface – but it was unable to account for a fundamental behavior of languages like Python and Node.js, where arguments passed as parameters can themselves invoke OS-level commands, bypassing sanitization entirely.
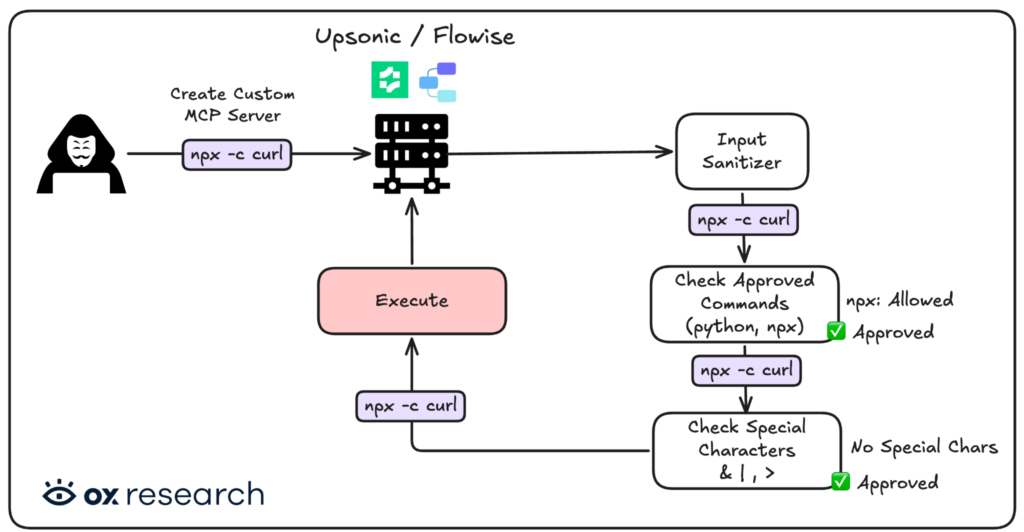
This shows that even when implementing best practices (as recommended by Anthropic) and maintaining well-secured code, developers cannot anticipate every edge case – leaving some API calls exposed.
When the underlying protocol is vulnerable, threat actors will find creative ways to bypass existing defenses, particularly when the goal is command execution and server takeover on high-value targets.
POC
Remediation
Developers and organizations encountering this issue should consider the following to prevent direct input-to-execution vulnerabilities from affecting their applications:
- Execute code and STDIO MCP servers inside an isolated sandbox environment
This prevents access to sensitive information on the server and limits the impact of both malicious actors and compromised MCP servers from reaching API keys, environment variables, and the hosting network. - Disable command execution where it isn’t needed
In most cases, STDIO MCP servers weren’t part of the original design. Disabling this capability by default – and enabling it only for approved users or specific use cases – eliminates this attack surface entirely. - Add authentication to your applications
If STDIO MCP usage is by design, a strong authentication mechanism and proper access controls can block unauthorized actors from gaining access and executing code. - Avoid using unauthenticated AI services that have access to sensitive information
Most AI services we tested – including LangFlow – were unauthenticated. Any threat actor gaining access to one can reach sensitive information, API keys, and AI data, and perform lateral movement across the hosting network.


)