TL;DR
The OX Research team discovered a vulnerability in DataEase (CVE-2026-23958) that allows attackers to brute-force admin passwords. Passwords are hashed with MD5 and used as JWT signing secrets, exposing weak credentials to attack. This is one of several critical vulnerabilities we discovered across popular open-source BI tools. More findings coming soon.
Severity: High
Affected Versions: All versions of DataEase up to 2.10.19
About DataEase
DataEase is an open-source business intelligence (BI) and data visualization platform designed as a lightweight alternative to proprietary enterprise tools. Maintained by FIT2CLOUD, it allows developers and analysts to build interactive, drag-and-drop dashboards by connecting to a wide array of databases like MySQL, Oracle, and ClickHouse.
The DataEase project is highly popular, with over 23K stars and 3.8K forks on GitHub, indicating widespread adoption across organizations seeking cost-effective BI solutions.
What We Discovered (CVE-2026-23958)
We discovered that the DataEase server uses an MD5 hash of the admin password as the secret key for signing authentication and authorization JWTs. This creates a critical vulnerability: MD5 is a weak hashing algorithm, allowing attackers to reverse or brute-force the hash to recover the plaintext password. Furthermore, an attacker can forge valid JWTs by brute-forcing the signature using various MD5 password hashes, effectively bypassing the server’s security.
Impact
- Admin account takeover through password brute-forcing
- Full system access and backend compromise
- Data exposure: Access to all connected databases, credentials, and sensitive business data
Who Is Affected?
All organizations running publicly accessible DataEase servers on vulnerable versions (up to v2.10.19) are affected.
Based on our Shodan analysis, we identified 95 publicly exposed DataEase instances.
Responsible Disclosure
We contacted the DataEase team on July 10, 2025, and they responded that a fix would be issued in the v2.10.19 release, which will be published on January, 2026.
Recommendations
- Upgrade once possible to DataEase v2.10.19 or later
- Use unique passwords for different accounts, and don’t use default passwords even for your internal services
Technical Analysis – CVE-2026-23958
Attack Scenarios: How could this be exploited in the wild?
- An attacker can brute-force an administrator’s password by repeatedly signing JWTs with guessed secrets and submitting them to token‑verification endpoints.
- Publicly accessible DataEase instances can be identified and targeted remotely, allowing attackers to forge valid admin JWTs and fully compromise the application.
Attack Graph
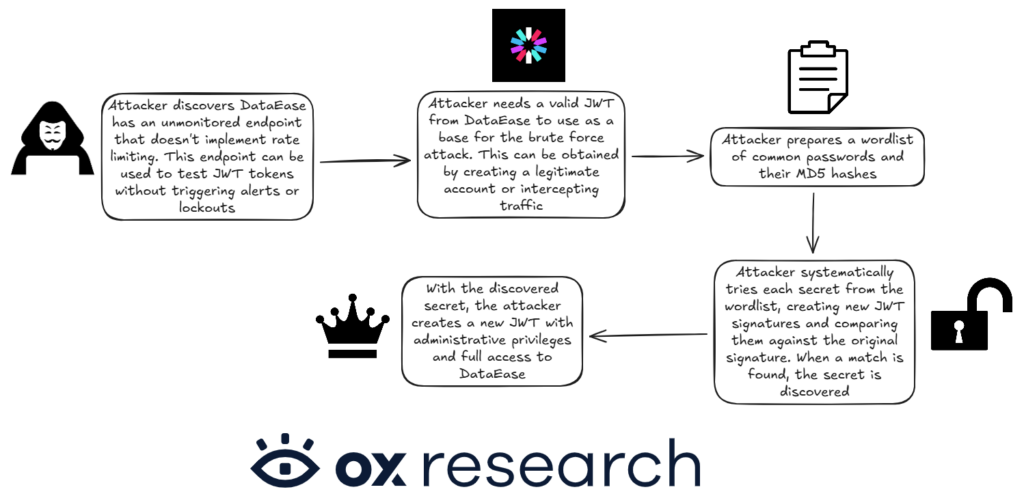
How it works
This vulnerability allows an attacker to compromise admin accounts, granting full control over the application and access to sensitive business data.
During a security review of DataEase’s source code, we identified a critical flaw in the way JSON Web Tokens (JWTs) are signed. The application uses the MD5 hash of a user’s password as the JWT signing secret.
Because this secret is deterministically derived from the password, an attacker can brute-force an admin’s password by targeting unmonitored API endpoints that validate JWT tokens.
The code that’s generating the password’s hash is inside this file:
sdk/common/src/main/java/io/dataease/auth/filter/CommunityTokenFilter.java
The secret is calculated by making use of the MD5 of the user’s password as can be found here:
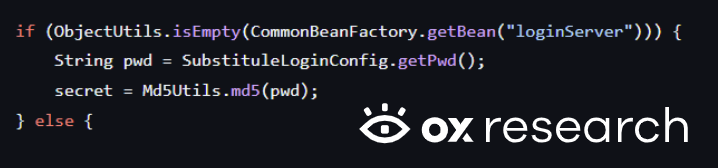
Diving into the function: the class method used to derive the hash was changed from “getPwd” to “getSecret” which removed the use of MD5 hashing of the password.

This secret, which is derived from the administrator’s password and is significantly easier to guess, is then used to sign the JWT, as shown later in the code.
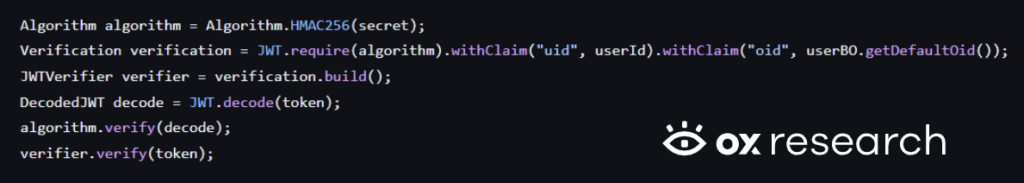
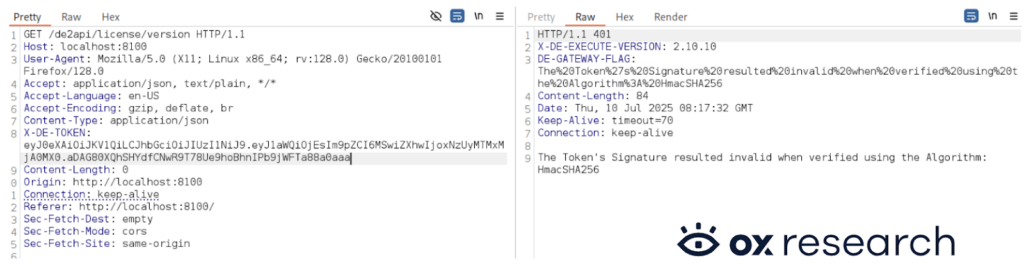
We then set up a local instance of DataEase and verified that the secret is calculated indeed as we understood while diving into the source code:

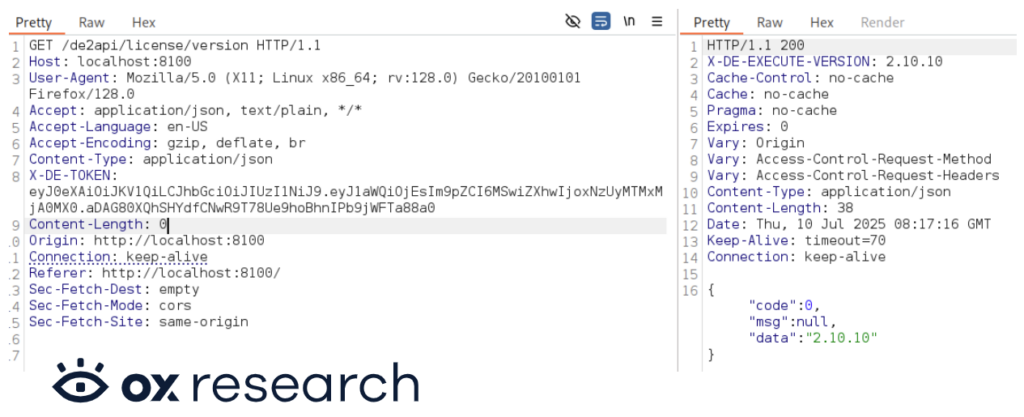
Later, we found an endpoint that can be used to take advantage of the vulnerability found in order to brute-force the secret of the administrator user without being limited by rate limiting, leading us to take over the administrator account and getting administrator access to the DataEase application:
KUDOS
We would like to thank Xu Wei (徐伟) from FIT2CLOUD for being responsive and collaborating with us to help keep the project secure and fix the vulnerability.
Too Good to BI True
This advisory is part of Too Good to BI True, OX Security’s research into the security posture of the most widely deployed open-source Business Intelligence platforms. Across five platforms, our researchers achieved full exploitation chains in every single one — reaching data that should never have been accessible. The findings include four zero-day discoveries and over 45,000 publicly exposed instances.
Read the advisories:


)



