The OX Research team exploited a known Redash sandbox escape vulnerability that allows remote code execution when the Python data source is enabled, leading to full server compromise
Severity: Critical
Vulnerability: Sandbox Escape (Known)
Affected Versions: All versions of Redash with the Python data source enabled
Impact: Remote code execution leading to full server compromise and potential data exposure
TLDR
Redash is a popular open-source data visualization and analytics platform that lets users connect to data sources, run queries, and build interactive dashboards. Designed for data analysts, engineers, and technical teams, it has approximately 28,000 GitHub stars and 4,500 forks, reflecting widespread adoption across the open-source ecosystem.
The OX Research team identified and exploited a known sandbox escape in Redash’s Python data source. When this feature is enabled, any user with query access can break out of the sandbox and execute arbitrary commands on the underlying server. No patch is available.
Impact
- Remote code execution on the Redash server
- Full compromise of the underlying system and application environment
- Exposure or manipulation of sensitive data accessible through Redash
- Deployment of malware or persistence mechanisms on the server
- Lateral movement to other systems within the internal network
Who Is Affected?
All Redash instances where the Python data source is enabled are potentially affected. Any deployment allowing users to run Python queries can be exploited, exposing the server to remote code execution and full compromise.
Recommendations
- Disable the Python data source in Redash unless it is absolutely required
- Restrict access to Redash instances and avoid exposing them publicly to the internet
- Limit user permissions to ensure only trusted users can create or run Python queries
- Monitor query execution and system activity for signs of sandbox abuse or unexpected command execution
Technical Analysis
Attack Scenarios: How could this be exploited in the wild?
- An attacker gains access to a Redash instance where the Python data source is enabled and submits a malicious Python query that escapes the sandbox.
- By abusing Python internals through the insecure getattr usage, the attacker executes arbitrary system commands on the Redash server.
- Once code execution is achieved, the attacker can take full control of the server, access sensitive data, and pivot to other systems within the network.
Attack Graph
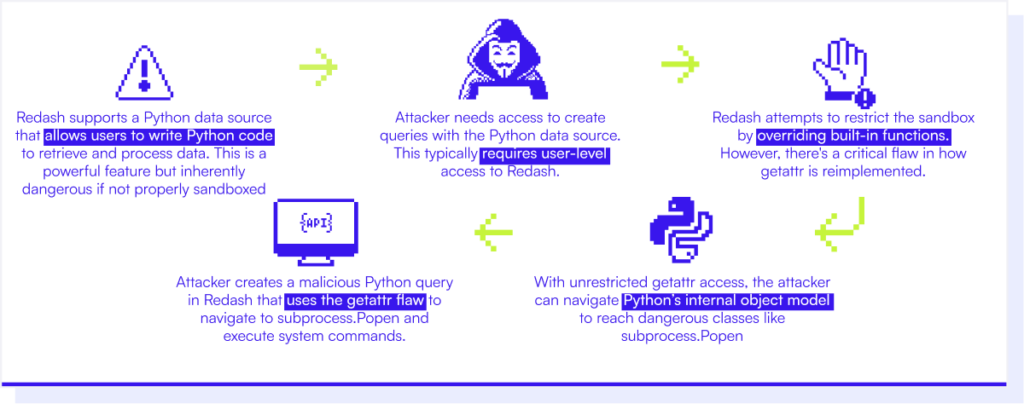
How it works
Redash supports a Python data source that allows users to execute Python code to retrieve and process data. Because executing arbitrary Python code is inherently dangerous, Redash attempts to mitigate this risk by running the code inside a restricted sandbox environment.
However, the sandbox implementation is flawed. Within the sandboxed execution context, Redash reassigns Python’s built-in getattr function to what is intended to be a restricted version. Due to an implementation error, the unrestricted built-in getattr is still accessible. As a result, any use of getattr inside the sandbox bypasses the intended security controls.
By looking into the source code at:
python.py – getredash/redash · GitHub
It can be observed that an insecure version of getattr is assigned to builtins[“getattr”].
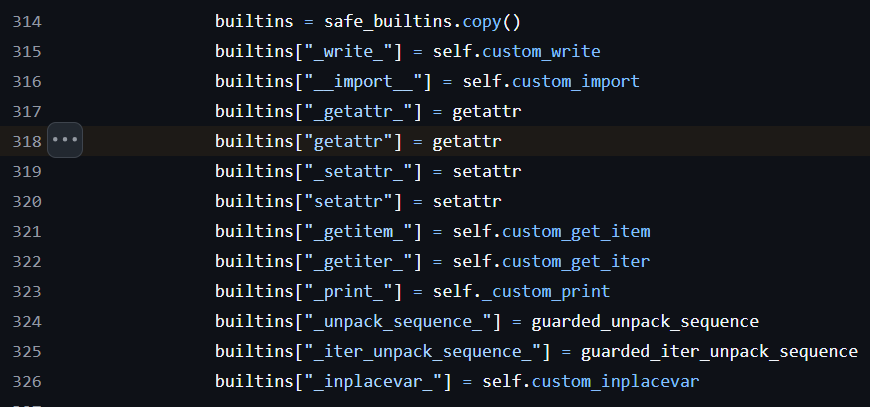
As a result, any use of getattr within the sandbox will invoke the unrestricted built-in function, potentially bypassing security controls.
An attacker can leverage this behavior to access Python’s internal object model. By navigating from basic objects to their base classes and enumerating all loaded subclasses, the attacker can locate powerful classes such as subprocess.Popen. Once accessed, these classes can be used to spawn new processes and execute arbitrary system commands.
This sandbox escape fully breaks Redash’s security boundary for the Python data source. When the feature is enabled, a malicious query is sufficient to achieve remote code execution on the Redash server, resulting in full system compromise.
Too Good to BI True
This advisory is part of Too Good to BI True, OX Security’s research into the security posture of the most widely deployed open-source Business Intelligence platforms. Across five platforms, our researchers achieved full exploitation chains in every single one — reaching data that should never have been accessible. The findings include four zero-day discoveries and over 45,000 publicly exposed instances.
Read the advisories:





