Microsoft’s Popular Document Converter Exposes Sensitive Files to Malicious Local Applications
Severity: High
Affected Versions: All versions of MarkItDown MCP Server
Impact: Local Privilege Escalation, Arbitrary File Read, Credential Theft
TL;DR
OX Research has discovered a vulnerability in Microsoft’s MarkItDown MCP server that exposes developer machines to file theft and credential harvesting. When the MCP service is running, any malicious local application can exploit a privilege escalation flaw to read arbitrary files – including SSH keys, AWS credentials, API tokens, source code, and configuration files – outside of intended working directories.
MarkItDown’s widespread adoption makes this vulnerability a threat to the developer community and software supply chain security.
About MarkItDown & its MCP
MarkItDown is a Microsoft-maintained open-source project that provides file conversion and document parsing capabilities, and it now includes an MCP (Model Context Protocol) server for integration with LLM applications such as Claude Desktop.
MarkItDown is widely adopted by developers with over 90k GitHub stars and 5k forks. Its MCP server is prominently advertised in the main repository README as an integration point for LLM applications such as Claude Desktop.
We identified a local privilege escalation vulnerability that allows a malicious local application to read arbitrary files under the MCP service’s privileges. This issue is significant because it breaks the intended security boundary of the MCP server and exposes sensitive system and application data on machines where the service is running.
Who is Affected?
Any user who runs the MarkItDown MCP service on their system may be exposed to unauthorized local file disclosure, including access to credentials, configuration files, source code, and other sensitive data.
Potential damage
This vulnerability enables local privilege escalation and significantly increases the risk of system and data compromise, especially on developer machines and shared environments.
An attacker who exploits this vulnerability can gain unauthorized access to sensitive files under the MarkItDown MCP service’s privileges, including credentials, API keys, configuration files, proprietary source code, and user data.
This can lead to further system compromise, lateral movement into other services, data theft, and full account takeovers in connected cloud environments. On developer machines, this significantly increases the risk of supply chain attacks and large-scale credential leakage.
Recommendations
- Limit MCP access – Run the service only with limited permissions, and on isolated machines with no file access to sensitive data.
- Apply access controls – Ensure only allowed directories are accessible by the MCP process.
Why We Chose to Focus on MCPs?
These findings extend OX Security’s broader MCP research initiative, which uncovered a systemic, design-level vulnerability in Anthropic’s MCP STDIO implementation — a flaw that propagated silently through downstream AI agent frameworks, developer IDEs, and MCP marketplaces, exposing an estimated 150 million downloads to risk.
Technical Analysis
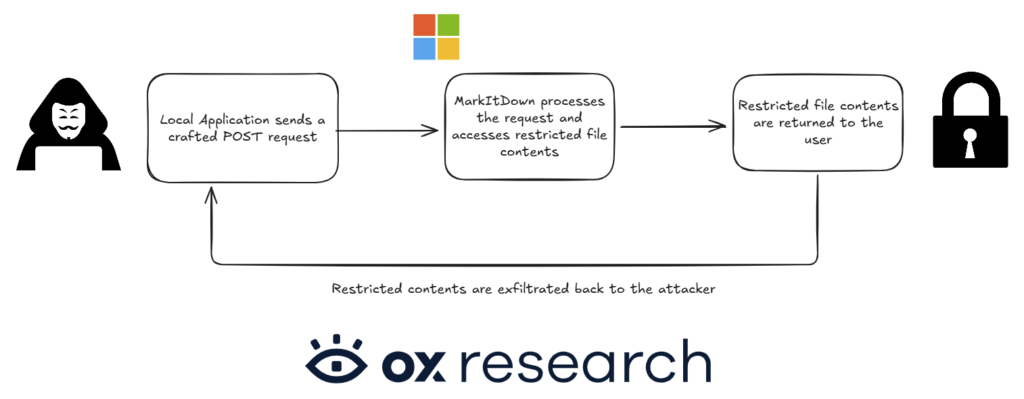
We examined how the convert_to_markdown MCP tool handles user-supplied URIs and found that it allows local file paths to be processed. By understanding how these inputs are handled internally, we were able to submit a crafted request that the MCP accepted and executed. As a result, the tool accessed and returned the contents of a file on the local system, based on the permissions granted to the MCP.
To identify the root cause of the vulnerability, we examined how the convert-to-markdown functionality works and how client-supplied input is used by the application, ultimately leading to data being read from the server.
We started by investigating the convert_to_markdown MCP tool inside the MarkItDown codebase:
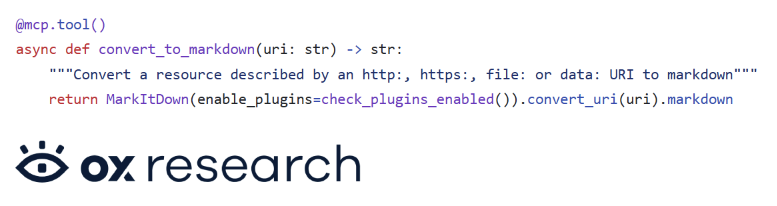
Calling covnert_uri function with an uri we can control, leads to the:
- Check if URI starts with “file:”
- Calling file_uri_to_path(uri) to extract the path
- Calling convert_local(path, …) with the extracted path.
Diving deeper into file_uri_to_path function
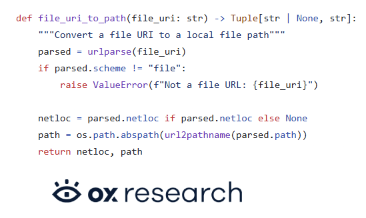
For example, for file:///etc/passwd, this returns (None, ‘/etc/passwd’).
Then, inside the function convert_local we will find where the file contents are actually accessed, the system opens the file in binary mode and reads it:
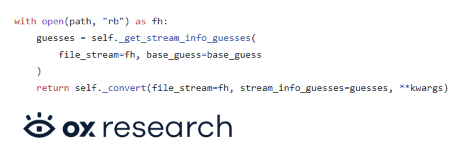
Based on the permissions granted to the MCP, it would have permission to read the relevant file.
Following the propagation of our uri parameter, we were able to craft a request that will be accepted by the MCP and get executed:
curl -L -X POST http://localhost:3001/mcp \
-H "Content-Type: application/json" \
-H "Accept: application/json, text/event-stream" \
-d '{
"jsonrpc": "2.0",
"id": 1,
"method": "tools/call",
"params": {
"name": "convert_to_markdown",
"arguments": {
"uri": "file:///c:/nirza"
},
"_meta": {
"progressToken": 1
}
}
}'
Which gave us in the response the contents of the restricted file.
Video PoC
Responsible Disclosure
We contacted Microsoft Security Response Center (MSRC) on 8-Dec-2025. Microsoft responded, sending to the project’s documentation, adding that: “this behavior is working as designed and does not represent a security vulnerability. Markitdown runs with the same privileges as the user who starts the process – it does not elevate permissions at any stage.
Authentication is not built into the service, and this is clearly documented. The recommended (and default) configuration binds the service to 127.0.0.1, ensuring that only local processes can connect”.