TL;DR
- Aikido is an application security platform that combines SAST (Static Application Security Testing), SCA (Software Composition Analysis), and container scanning in a single interface. It focuses on detecting vulnerabilities in code and dependencies, but as teams grow, its simplified model and limited integration depth can restrict visibility across larger, multi-pipeline environments.
- AppSec teams need platforms that provide active risk correlation, context-aware prioritization, and flexible governance while integrating unified dashboards into existing CI/CD workflows.
- This shift toward Application Security Posture Management (ASPM) is driven by the need for real-time insight across repositories, pipelines, and deployments, and not just static scanning results. Tools like OX Security, Snyk, Checkmarx, Veracode, and Qualys provide stronger integration ecosystems and more advanced automation to reduce security debt faster.
- This guide compares the top five Aikido alternatives for 2026: OX Security, Snyk, Checkmarx One, Veracode, and Qualys, focusing on visibility, scalability, developer experience, and readiness for current DevSecOps environments.
Aikido positions itself as an all-in-one security tool for developers, bringing code and dependency scanning under one interface. It focuses on simplicity, providing Static Application Security Testing (SAST) and Software Composition Analysis (SCA) through a single dashboard. While this makes it accessible for smaller engineering teams, reviews and user feedback suggest that as projects expand, the platform can lack the flexibility and visibility required for large-scale DevSecOps environments. This article explores several mature alternatives that address those scalability and governance challenges more effectively.
Consider a team of 25 developers managing 40–50 microservices across multiple CI/CD systems, such as GitHub Actions, Jenkins, or GitLab. Each service runs its own scans, generating hundreds of isolated results every week. Without a unified view, teams spend more time sorting duplicate issues than fixing critical ones. Aikido centralizes some of this data, but as pipelines multiply and compliance needs expand, visibility and governance often fall behind the pace of development.
The 451 Alliance recently reported that among organizations with existing application security tooling, 20% have already adopted Application Security Posture Management (ASPM) platforms, and another 14% plan to within the next year. This data underscores a clear market shift: security teams are moving beyond isolated scanners to adopt ASPM systems that unify risk data across code, build, and runtime phases.
In this guide, we’ll break down the top five Aikido alternatives for 2026: OX Security, Snyk, Checkmarx, Veracode, and Qualys. Each section breaks down how these tools handle visibility, remediation, and integration, helping you decide which platform aligns best with your team’s DevSecOps maturity and scale.
Why Enterprises Are Exploring New AppSec Options
Many organizations are reassessing their application security stack to address visibility gaps, workflow fragmentation, and compliance requirements that traditional scanners no longer meet.
- Real-time security and ASPM adoption: Teams need ongoing visibility across code, pipelines, and runtime, not point-in-time scans.
- Complex multi-repo and multi-pipeline setups: Security teams need unified control across multiple repositories, CI/CD tools, and deployment targets instead of managing isolated scanners per project.
- Unified visibility and risk correlation: Correlating isolated findings into a single risk view helps prioritize real issues and reduce manual triage.
- Compliance and audit readiness: Centralized platforms simplify audit preparation, compliance tracking, and policy enforcement for enterprises facing stricter reporting requirements.
- DevSecOps workflow integration: Developers prefer tools that integrate directly with their CI/CD and IDE workflows, allowing them to fix vulnerabilities during development instead of after deployment.
When to Look for an Aikido Alternative
Teams often reach a point where their security needs surpass what Aikido’s all-in-one setup can handle. Here are a few clear indicators that it might be time to evaluate other options.
1. Limited Pipeline Visibility Across Security Stages
When vulnerability data is split between code, build, and runtime environments, teams lose track of where the actual risk lies. A platform with unified visibility helps connect these stages and streamline remediation.
2. Difficulty Scaling Security Workflows for Large Teams
As development groups and repositories grow, enforcing consistent scanning policies becomes harder. Enterprise-grade platforms allow centralized control while keeping developer autonomy.
3. Limited Integration Depth with Existing Toolchains
If connecting Aikido to CI/CD systems, ticketing tools, or vulnerability databases requires workarounds, productivity suffers. Broader API coverage and native integrations simplify adoption and reduce maintenance overhead.
4. Compliance and Governance Requirements Outpacing Capabilities
Meeting frameworks like SOC 2, NIST, or ISO 27001 demand detailed audit logs and custom policies. Alternatives providing governance dashboards and compliance templates make these requirements easier to meet.
5. Need for Contextual Prioritization and Risk Correlation
Raw vulnerability counts mean little without context. Platforms that correlate findings across scanners and environments help teams focus on the few issues that actually pose business risk.
Top 5 Aikido Alternatives in 2026
1. OX Security: End-to-End ASPM for Full Pipeline Visibility
Overview
OX Security provides Active Application Security Posture Management (ASPM) that connects every stage of the development lifecycle: from source control to build, deployment, and runtime. From code creation to build, deployment, and runtime, OX provides live visibility into application risk by bringing together advanced scanning with dynamic context and automation.
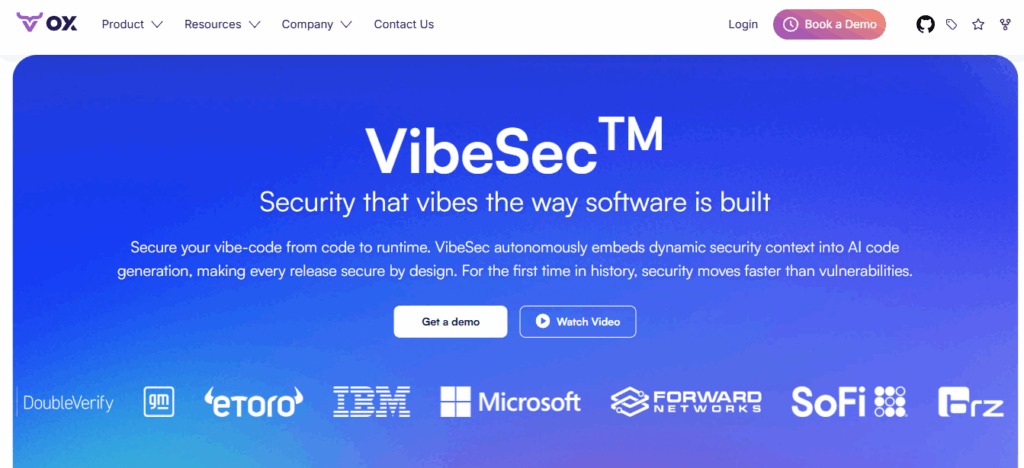
At the heart of the platform lies VibeSec™, OX Security’s adaptive intelligence layer that understands how advanced code is built, shared, and deployed. It analyzes context across developers, pipelines, and environments to automatically detect risk patterns and enforce security controls as code moves through the lifecycle.
OX’s Pipeline Bill of Materials (PBOM) constantly tracks code, dependencies, pipelines, and deployments to keep your security posture mapped in real time. With agentic autonomy through the AI-agent and OSC&R (Operational Security & Compliance Remediation) features, policy enforcement is baked directly into every commit, helping teams reduce security debt and stay audit-ready.
Key Features of OX Security
- Active ASPM across the full stack: Constantly correlates findings from SAST, SCA, IaC, and container scans into a unified risk fabric, enabling holistic posture management.
- VibeSec™ embedded security: Security context is built into AI coding tools and developer workflows, avoiding vulnerabilities from being created rather than just detected.
- Live PBOM (Pipeline Bill of Materials): Maintains a live map of code, dependencies, pipelines, and deployments to reflect the current security posture rather than static snapshots.
- Osc&R (Operational Security & Compliance Remediation): Security policies are enforced agentically to be aligned with your standards and automatically applied across workflows and runtime.
- AI-Agent Autonomy & Policy Enforcement: The AI-agent analyzes context, prioritizes issues, and generates tailored remediation suggestions aligned to your environment.
- Seamless integrations + centralized governance: Supports 100+ integrations into IDEs, CI/CD tools, cloud, and scanners, restoring visibility across silos and enabling enterprise scale.
Hands-on Example of Implementing ASPM Across the SDLC with OX Security
You can implement OX Security’s Active ASPM in just a few steps. After creating an organization and API key, connect your repositories (GitHub, GitLab, or Bitbucket) and add the OX scanner to your CI/CD pipeline. The integration runs automatically during pull requests, generating a real-time security posture report visible in the OX dashboard.
For the complete step-by-step implementation, refer to the official OX guide:
Hands-On Example of Implementing ASPM Across the SDLC with OX Security
View the Dashboard
- Once a repository is connected, it displays a unified dashboard that shows vulnerabilities, PBOM coverage, and security posture across the software supply chain.
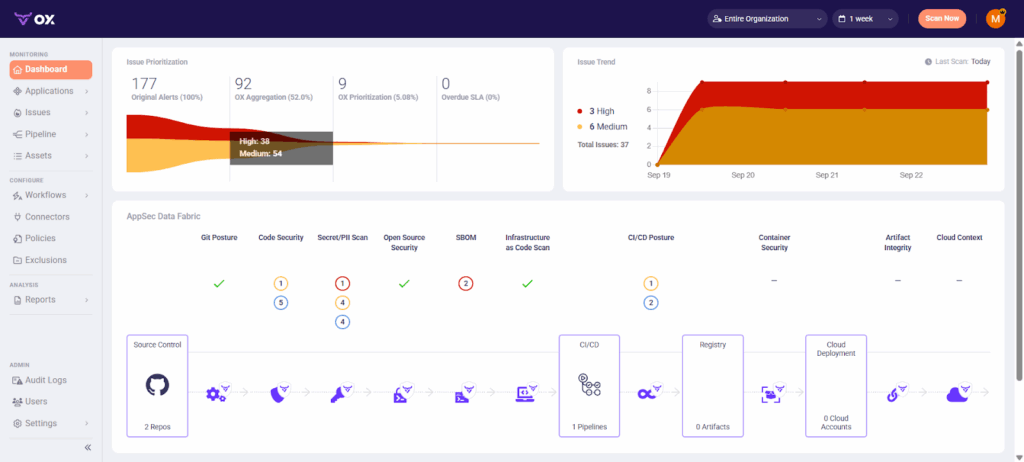
Analyze Risk And Prioritize Fixes
All pipeline scans are automatically pulled into the AppSec Data Fabric. If you also rely on third-party scanners, you can import their results via API. OX normalizes everything into a unified schema, so your team sees one list of findings instead of juggling multiple dashboards.
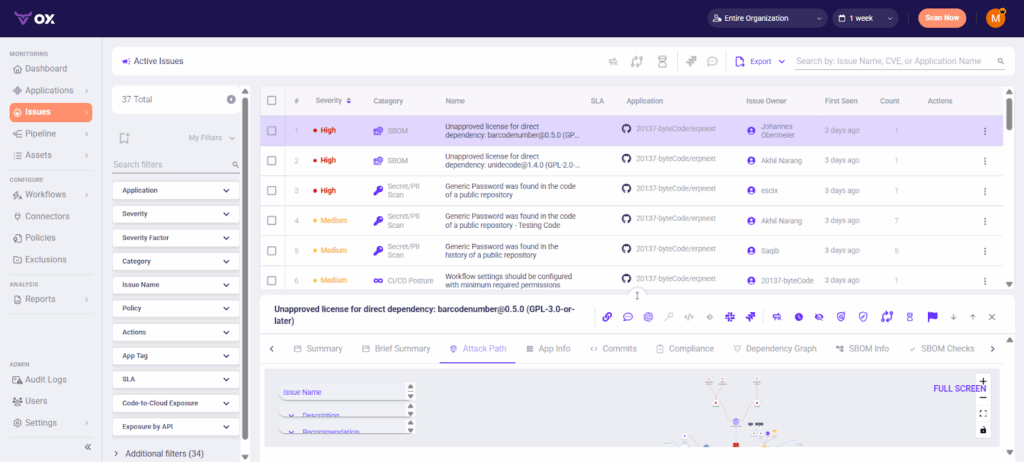
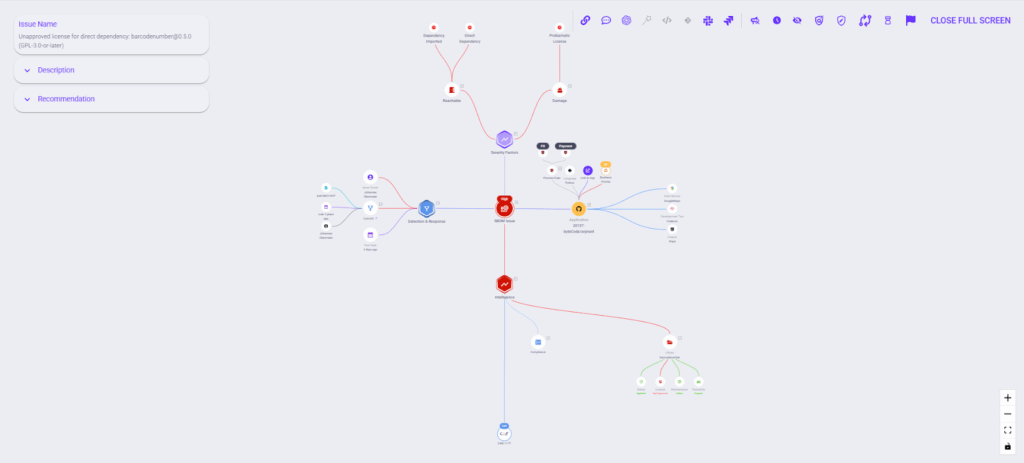
Inspect the Attack Path Graph
Here you’ll see how findings connect across code functions, dependencies, and cloud assets. The view overlays exploitability and business impact, making it clear which vulnerabilities truly pose a threat to production.
- Go to Applications → [Your App] → Attack Path / Reachability.
- Use filters like Reachable, Exploitable, and Business Impact in the UI.
Pros
- Unified security visibility: Combines multiple scanning tools into a single risk map, removing data silos.
- Context-aware prioritization: Uses graph correlation and VibeSec™ to rank vulnerabilities by impact and reachability.
- Enterprise-ready governance: Provides policy enforcement, compliance mapping, and detailed audit trails.
Cons
- Setup complexity: Requires initial onboarding for configuring pipelines and integrations in large environments.
- Enterprise-focused pricing: Tailored plans may be overkill for small teams or startups.
- Learning curve for policy automation: Advanced rule customization needs familiarity with OX’s governance model.
2. Snyk: Developer-Centric Security Platform
Overview
Snyk is a developer-first security platform built to identify and fix vulnerabilities early in the development cycle. It integrates directly with code editors, pull requests, and CI/CD pipelines, allowing developers to detect and remediate issues before deployment. Snyk focuses on speed and usability, helping engineering teams maintain security without slowing down their release process.
Key Features of Snyk
- Comprehensive coverage with SAST, SCA, IaC, and container scanning.
- Inline pull request checks and auto-generated fix suggestions.
- Native integrations with GitHub, GitLab, Bitbucket, Jenkins, and Azure DevOps.
- IDE support for VS Code, IntelliJ, and JetBrains environments for instant feedback while coding.
Hands-On with Snyk: From Detection to Automated Fixes
Snyk makes it easy to identify vulnerabilities in your projects and automatically open pull requests with recommended fixes. Once the GitHub integration is done, Snyk regularly monitors your repositories and alerts you whenever a new issue appears. Below is a step-by-step walkthrough showing how we added our frontend project and used Snyk’s automated remediation workflow.
Step 1: Connect Your Repository to Snyk
- After signing in to Snyk, navigate to Integrations → Source Control and choose GitHub or any other platform.
- Authorize your account and select the repository you want Snyk to monitor. Once connected, Snyk automatically scans the repository’s package.json and any Dockerfiles it detects.
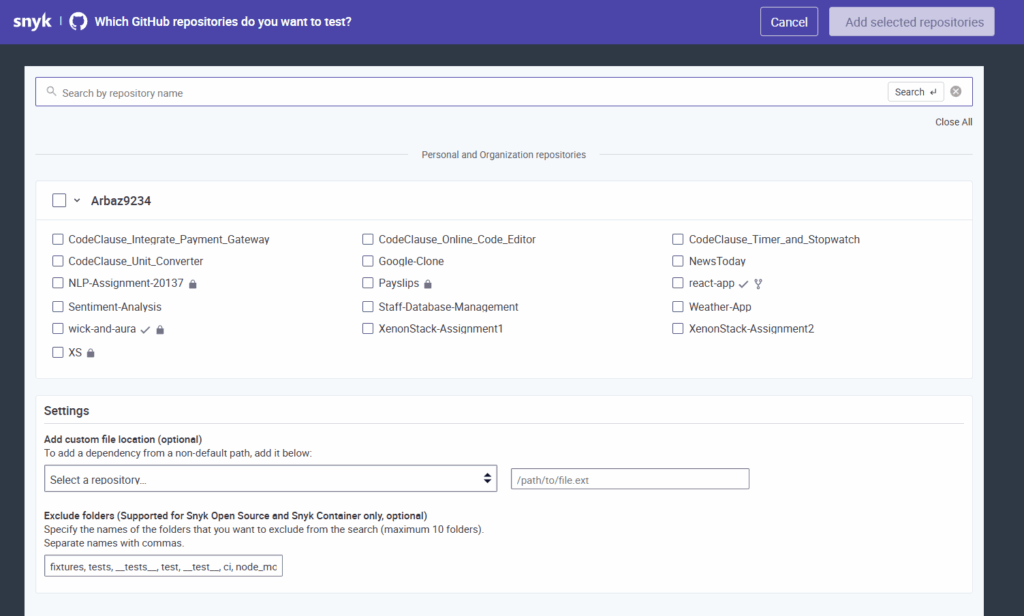
In the Projects tab, your repository now appears as a list of targets, in this case, Dockerfile-java and Dockerfile-react. Each target shows the number of issues, the last scan date, and a summary of severity levels.
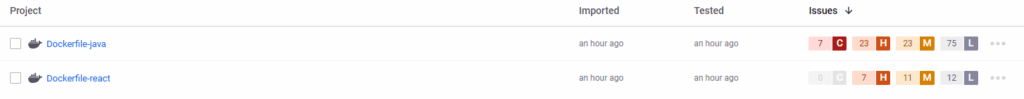
This dashboard gives a quick overview of where the highest-risk components lie.
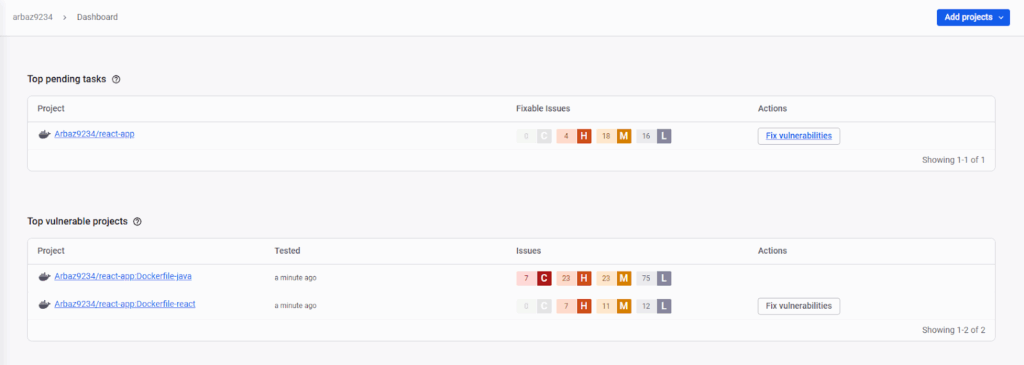
Step 2: Review the Security Report
- Open any project target to view the detailed security report.
Snyk lists each vulnerability with its CVE, severity, priority score, exploit maturity, and whether a fix is available.
In our case, Snyk identified multiple dependency vulnerabilities in npm packages as well as a critical issue in the Docker base image (node:16-alpine).
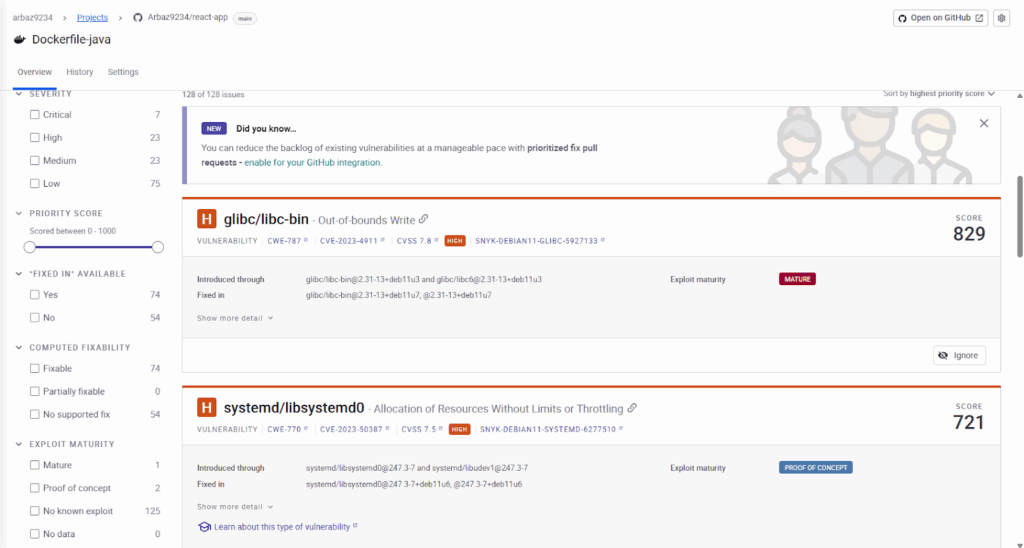
The dashboard also displays overall issue distribution by severity and provides contextual data such as the package version affected and the suggested upgrade path.
Step 3: Generate a Fix Pull Request
To remediate an issue, click Open a fix PR from the issue details page.
Snyk automatically drafts a pull request in your GitHub repository containing the required dependency or image upgrades.
For example, Snyk suggested upgrading the Docker base image from node:16-alpine to node:25.1.0-alpine.
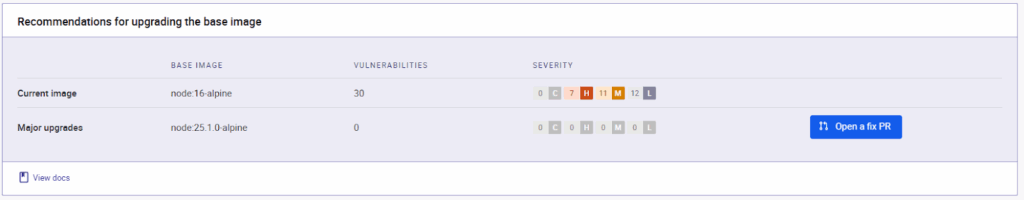
The generated pull request includes:
- A clear title (e.g., [Snyk] Security upgrade node from 16-alpine to 25.1.0-alpine).
- A summary of the vulnerabilities it resolves, with CVE references and severity breakdowns.
- Direct links back to Snyk for verification.
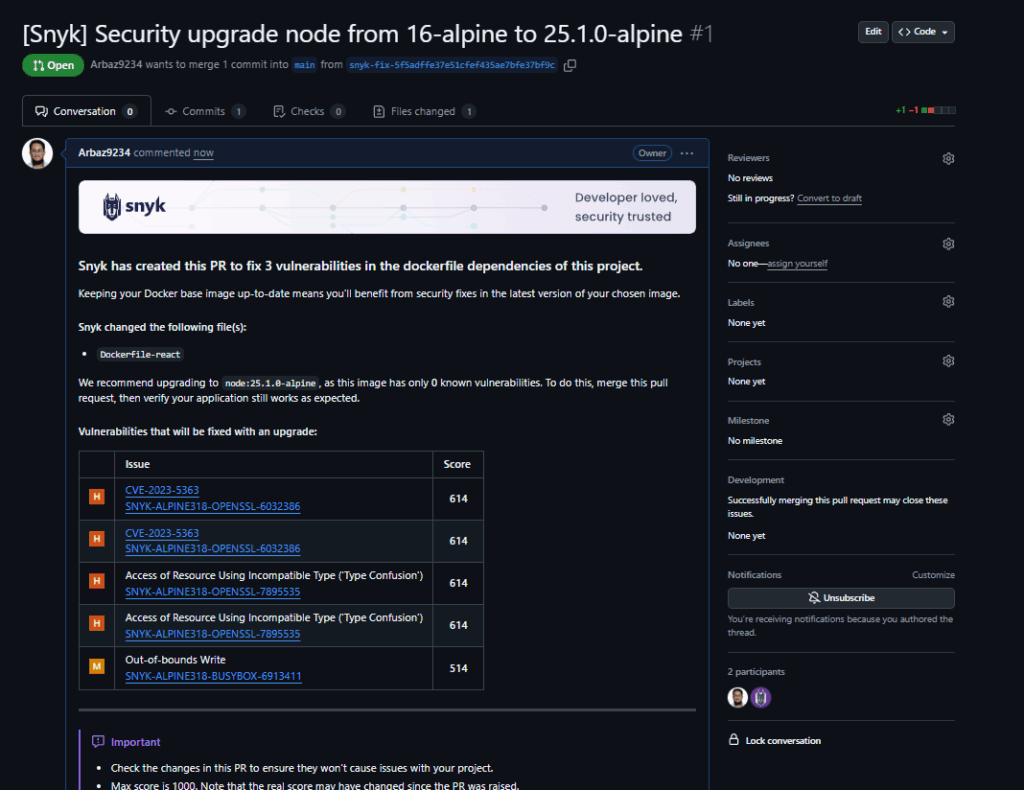
Step 4: Review and Merge the PR in GitHub
- Once the pull request is created, review the changes in GitHub.
- Each fix PR contains only the minimal required modifications — for instance, updating a version number in the Dockerfile or package manifest.
- After your CI pipeline validates the changes, merge the PR to apply the fix.
Snyk automatically re-scans the repository after the merge, confirming that the vulnerabilities have been resolved and updating the project’s status on the dashboard.
Result
By integrating directly with GitHub, Snyk closes the loop between detection and remediation.
In our project, the tool not only flagged outdated dependencies but also handled the entire fix workflow, from identifying the issue to opening and validating the pull request, to allowing developers to maintain a secure codebase with minimal manual effort.
Pros
- Excellent IDE integration: Security feedback appears directly where developers write code.
- Fast vulnerability detection: Enables proactive fixes through automated PR checks and patches.
- Wide ecosystem compatibility: Works smoothly across popular languages, frameworks, and CI/CD tools.
Cons
- Limited enterprise visibility: Risk management and reporting are less advanced compared to ASPM platforms.
- Cost scaling: Pricing increases significantly with large repositories or multiple environments.
- Dependency on cloud connectivity: Some scans require online access, limiting flexibility for restricted networks.
3. Checkmarx One: Enterprise-Grade AppSec Platform
Overview
Checkmarx One is an enterprise-focused Application Security Testing platform built to help large organizations secure complex software delivery pipelines. It provides deep static and interactive testing with governance controls that align with compliance frameworks and enterprise policies. Checkmarx is best suited for teams with hybrid infrastructure setups, long software lifecycles, and regulatory obligations that require strict security validation at every stage of development.
Key Features of Checkmarx One
- Advanced SAST engine with customizable rulesets and language coverage for advanced stacks.
- Interactive Application Security Testing (IAST) and IaC scanning for runtime and infrastructure visibility.
- Centralized risk management dashboards with compliance mapping for frameworks like OWASP, NIST, and ISO 27001.
- Seamless integration with CI/CD systems and ticketing platforms such as Jenkins, GitLab, and Jira.
Pros
- Accurate static analysis: Strong rule engine minimizes false positives and detects complex code-level flaws.
- Granular policy control: Ideal for enterprises with layered security and compliance needs.
- Comprehensive compliance mapping: Built-in templates align with major regulatory frameworks.
Cons
- Complex initial setup: Requires configuration and calibration for large multi-repo projects.
- Longer scan durations: Deep static scans can delay pipelines in large monolithic repositories.
- Higher operational overhead: Managing policies and updates demands ongoing security team involvement.
4. Veracode: Proven Application Security at Scale

Overview
Veracode is one of the most established names in application security, providing a SaaS-based platform that unifies Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), and Software Composition Analysis (SCA). It’s widely used by large enterprises that require strong compliance, structured workflows, and policy enforcement across distributed teams. Veracode’s strength lies in its reliability, governance features, and audit-ready reporting.
Key Features of Veracode
- Centralized reporting and policy management for tracking vulnerabilities across multiple projects.
- Binary static analysis that scans compiled code for deeper coverage across languages and frameworks.
- Integrations with major CI/CD systems such as Jenkins, GitHub Actions, and Azure DevOps.
- Automated ticketing and workflow sync with Jira and ServiceNow for vulnerability lifecycle management.
Pros
- Comprehensive compliance coverage: Meets the needs of regulated industries with detailed audit and reporting capabilities.
- Proven reliability: SaaS-first model simplifies deployment and scales well for large teams.
- Strong enterprise integrations: Native connections to CI/CD tools and ticketing systems.
Cons
- Slower scan performance: Full static and dynamic scans can delay fast-moving CI/CD cycles.
- Limited runtime visibility: Focuses on testing and reporting rather than end-to-end posture management.
- Less flexibility for advanced workflows: Built primarily for traditional release cycles over agile, multi-pipeline environments.
5. Qualys: Unified Vulnerability and App Security Platform
Overview
Qualys is best known for its vulnerability management suite, but it also provides strong coverage for application and cloud security. It provides dynamic scanning and regular monitoring across on-premises, cloud, and hybrid environments. The platform is designed for security and IT operations teams that need full visibility of their infrastructure, web applications, and endpoints within a single ecosystem.
Key Features of Qualys
- Web Application Scanning (WAS) for constant assessment of web apps and APIs.
- Patch management and endpoint visibility to track and remediate vulnerabilities across servers and devices.
- Integration with CI/CD pipelines through APIs and automation connectors.
- Cloud agent technology for real-time asset discovery and drift detection.
Pros
- Advance vulnerability intelligence: Backed by a large threat research database for accurate detection and prioritization.
- Broad infrastructure visibility: Monitors applications, containers, endpoints, and networks from a single dashboard.
- Enterprise scalability: Handles distributed, multi-environment deployments efficiently.
Cons
- Outdated user interface: Navigation and reporting feel less intuitive compared to newer platforms.
- Developer experience limitations: Lacks IDE integrations and PR-based workflows preferred by DevSecOps teams.
- Focused on security operations: Designed more for SecOps than day-to-day developer use.
Which Aikido Alternative Fits You Best?
Each platform brings different strengths depending on team size, integration needs, and security maturity. The table below summarizes how the top Aikido alternatives compare across key dimensions.
| Tool | Primary Strength | Ideal For | Enterprise Readiness | Pricing Model | Community Support |
| OX Security | Active ASPM with full pipeline visibility and risk correlation | Large enterprises | High | Enterprise plan based on pipelines and integrations | Moderate (growing enterprise adoption and documentation-driven community) |
| Snyk | Developer-first security with fast IDE feedback | Dev-focused teams | Medium | Per developer seat with usage-based tiers | Strong (vibrant open-source and developer community) |
| Checkmarx One | Deep static and interactive analysis | Regulated orgs | High | Annual license by app volume | Moderate (active enterprise user forums, limited open community) |
| Veracode | SaaS-based testing with strong compliance support | Mid–large enterprises | High | Per app or portfolio with enterprise SLAs | Limited (enterprise-only community and private knowledge base) |
| Qualys | Vulnerability and web app scanning | Security ops teams | Medium | Modular pricing by asset and product | Limited (customer portal and managed community forums) |
Why Choose OX Security as an Aikido Alternative
When security must match the pace of AI-powered development, OX Security provides a cutting-edge solution built for teams that demand speed, visibility, and context.
1. True Active ASPM built for the entire SDLC
OX’s platform doesn’t just bring the results together from separate tools; it provides Active Application Security Posture Management (Active ASPM), enabling real-time visibility from source control, CI/CD pipelines, artifact registries, all the way to runtime.
2. VibeSec™: Security that “vibes” with how advanced code is built
With VibeSec™, security is embedded at the point of creation so that it dynamically feeds context into AI-coding workflows so that vulnerabilities are prevented, not simply detected.
3. Seamless integration and ecosystem flexibility
The platform supports both native scanning and third-party tools, providing over 100 integrations and auto-discovery across apps, pipelines, containers, and cloud assets.
4. Context-driven prioritization and automation
Using technologies like Code Projection and Pipeline Bill of Materials (PBOM), OX clarifies what is of value to resolve, such as lowering noise, highlighting reachability and exploitability, and enabling automated workflows and remediation.
5. Built for large teams and enterprise scale
With enterprise-ready governance, compliance mapping (35+ frameworks), audit-ready traceability, and AI-driven risk management, OX supports organizations that demand high assurance without sacrificing speed.
Conclusion
Internal Developer Platforms (IDPs) have become a foundation for advanced engineering, bringing structure and visibility to how teams build and release software applications. They create alignment between development, operations, and governance, helping organizations maintain speed without losing control. By acting as a single coordination layer, IDPs ensure that what reaches production is consistent, secure, and cost-aware.
Throughout this article, we looked at how organizations are reassessing tools like Aikido and exploring platforms that provide broader context and deeper coverage. Each option brings its own strengths: some focus on developer-first adoption, others on compliance and governance, while newer ASPM platforms like OX Security bridge both worlds through unified risk mapping and regular monitoring.
In conclusion, the right choice depends on your security maturity and delivery model. For teams managing large and complex pipelines, OX Security’s Active ASPM approach provides constant coverage from code to cloud, thus helping identify, prioritize, and remediate risks in real time. Regardless of which tool you choose, the goal remains constant: to make security a built-in part of your software lifecycle, not a step that comes after deployment.